Macintosh
What is the Macintosh (Mac)?
The Macintosh, now called the Mac, was the first widely sold personal computer (PC) with a graphical user interface (GUI) and a mouse. Apple Computer Inc. -- now Apple Inc. -- introduced the Macintosh in an ad during Super Bowl XVIII, on Jan. 22, 1984, and offered it for sale two days later.
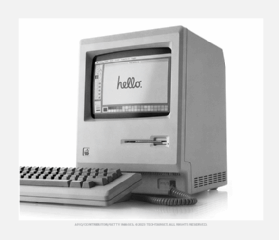
The original Macintosh computer was designed to provide users with a natural, intuitive and user-friendly computer interface. Advances in the Macintosh's user-friendly design included the use of a mouse, icons to represent objects and actions, the point-and-click and click-and-drag actions, and a number of window operation ideas. Many of these GUI ideas came from experiments at the Xerox Palo Alto Research Center, or PARC, in the early 1970s. Microsoft successfully adapted these concepts for its first Windows operating system (OS).
The predecessor to the Macintosh was the Apple Lisa. It had the same interface and operating environment as the Macintosh, but at about $10,000, Lisa's price was steep and out of range for many potential customers. Lisa was also large and heavy, and not a promising platform for a desktop computer. Lisa advanced the capabilities of the GUI and other functions, but the Macintosh ultimately surpassed it.
Who uses the Apple Macintosh?
The Apple Macintosh's powerful GUI and advanced design capabilities made it a popular choice among professionals in creative fields, such as those working in design and architecture. Academics also were early users. When it first debuted, the Macintosh's GUI was easier to use than other PCs of the time. It was an instant hit among designers and architects who needed powerful tools that were easy to use.
In 2006, Apple began transitioning the Mac to using Intel processors, making it possible to run the Microsoft Windows OS and its applications on Apple computers. Boot Camp let users dual boot both the Apple and Windows OSes on a Mac. Virtualization is now used to run Windows on Macs.
Today, many creative professionals still prefer Mac computers, but Macs are also widely used for business applications as well as personal uses, such as gaming or media consumption. Several different models are available, ranging from budget-friendly laptops to high-end workstations.

How the Macintosh works
The Mac runs on its own OS, which was originally called System Software. It was rebranded as Mac OS in 1996 and as the Unix-based Mac OS X in 2001. Mac OS X has since been rebranded as OS X and is now called macOS. The Macintosh originally ran on the Motorola 68000 series microprocessors; Apple later used the Apple, IBM and Motorola -- or AIM -- Alliance's PowerPC central processing unit (CPU) before moving to Intel x86 processors. Today, Macs use Apple M1 and M2 processors.
The Mac is configured the same as other desktop and laptop computers, with CPU, memory, hard drives and solid-state drives, OS, visual display, graphics engine, input/output (I/O) connectors, power supply, keyboard, mouse and connections to external devices.
The Apple products in the Macintosh line today include the following:
- iMac all-in-one desktop.
- Mac mini standard desktop system.
- Mac Studio professional desktop system.
- Mac Pro high-performance system.
- MacBook Air general use laptop.
- MacBook Pro professional laptop.
Why is the Macintosh important?
The Macintosh paved the way for a variety of desktop, laptop and wireless computing devices, such as the iMac, MacBook, iPod, iPad and iPhone. It has always been a powerful system with a user-friendly interface. It opened the door for Microsoft to develop its Windows OS.
In its early years, the Macintosh attracted creative and academic users. However, it has evolved to successfully support business activities. Its many iterations, ranging from laptops to desktop systems and powerful creative production systems, continue to reinforce its popularity.

History of the Macintosh
Some key dates in the history of the Macintosh include the following:
- 1984. Apple released the Macintosh on Jan. 24. It became one of the first commercially successful PCs with a GUI.
- 1985. Steve Jobs left Apple and founded NeXT Inc.
- 1986. Apple introduced the Macintosh Plus with increased memory and Small Computer System Interface, or SCSI, ports for external devices.
- 1987. Apple introduced the Macintosh II, the first expandable Macintosh with color capabilities.
- 1989. The popular Macintosh SE/30 was released with 1 megabyte of RAM, expandable up to 128 MB.
- 1991. The System 7 OS was launched, as were the PowerBook laptops and Quadra desktop machines, offering improved multitasking capabilities compared with earlier versions.
- 1994. Apple introduced the Power Macintosh, which used the more powerful PowerPC processors.
- 1996. The Macintosh System Software OS was rebranded as Mac OS.
- 1997. Jobs returned as CEO of Apple as part of Apple's acquisition of NeXT.
- 1998. The iMac G3 was released with an all-in-one design and USB ports.
- 2001. Apple introduced Mac OS X, which combined the stability of Unix with a user-friendly interface.
- 2006. Apple began using Intel processors in MacBook Pro laptops, along with other updates such as multitouch trackpads and LED displays. Apple also introduced the Mac Pro, a high-performance desktop workstation for professional users.
- 2008. Apple introduced the MacBook Air, an ultrathin, lightweight laptop.
- 2010. Apple released the iPad tablet computer with a touchscreen interface.
- 2011. Apple launched OS X Lion with features including Mission Control, full-screen apps, Launchpad and AirDrop support. The MacBook Pro also got Thunderbolt I/O technology that let users transfer data at faster speeds by connecting peripherals directly to the computer using lightning-fast ports.
- 2012. The MacBook Pro with Retina display was released, capable of displaying ultrahigh resolution for sharper images and text. Mac OS X was renamed Mac OS.
- 2016. The Mac operating system was rebranded as macOS.
- 2020. Apple introduced its M1 chip, designed specifically for Macs, combining high performance and energy efficiency.
- 2022. The M2 chip was announced and began appearing in MacBook Air and MacBook Pro models.
- 2023. Apple continued to evolve its Apple Silicon by introducing the M3, M3 Pro and M3 Max chips. Those chips initially found their way into updated 14-inch and 16-inch MacBook Pro models and the 24-inch iMac with M3 processors
- 2024. At the beginning of the year, Apple released the M3 MacBook Air models and introduced the M3 and M3 Pro Mac mini models. The M3 and M3 Ultra debuted in the Mac Studio and Mac Pro. At the end of 2024, Apple debuted its custom processors M4, M4 Pro and M4 Max, first appearing in the MacBook Pro notebooks and Mac mini desktop.
- 2025. In March, Apple debuted an M4-powered MacBook Air in 12- and 15-inch models, for the first time offering the notebook in a sky blue color. At the same time, Apple released an M4-powered version of the Mac Studio, supporting the M4 Max and M3 Ultra chips.
Find out more about how Macs are being used in the enterprise in our guide to managing Mac hardware and software.
