app
What is an app?
App is an abbreviated form of the word application. An application is a software program that's designed to perform a specific function directly for the user or, in some cases, for another software program.
The term app was popularized in the early days of smartphones, after Apple introduced the iPhone in 2007 and then launched the App Store in 2008. At the time, the term applied primarily to mobile apps, which were lightweight and focused on a specific purpose or task, such as checking the weather, taking notes, performing calculations or reading the news.
Over the years, the term has grown in scope and is now often used to refer to applications running on any type of device. This trend has been reinforced by major vendors who now use the term routinely to reference software applications. For example, Apple refers to the Mac software available from its App Store as apps, and Microsoft refers to the Windows software available from its Microsoft Store as apps. Google Play offers Chromebook apps alongside apps for phones, tablets and other devices.
Despite this trend, some resources continue to use the term app primarily to refer to mobile device applications, although their usage might also include software for devices such as Apple TV or Amazon Fire TV. At the same time, other resources might use the term app for applications with limited functionality, primarily to distinguish them from more robust PC software. There is, in fact, no hard-and-fast rule that dictates exactly how the term should be used, although the general trend has been toward greater inclusivity.
What are the types of apps?
When the term app is used in a more general sense, the apps themselves are often categorized by their characteristics or how they're implemented. The following list describes the more common categories:
- Web apps. In this scenario, the app is hosted on a remote server or distributed across multiple servers. Users access the web app over the internet through one of the supported web browsers. Most of the processing and back-end operations occur remotely. The client system might carry out some of the processing, such as when running client-side scripts, but this is typically minimal. Web apps can be accessed from a wide range of devices, as long as they're running a supported browser.
- Native apps. The app is installed on the local system and uses the resources on that system to perform the required operations. A native app can take full advantage of the system's features and capabilities, unlike other types of apps. For this reason, a native app must be developed specifically for the target platform on which it will run. It usually cannot run in other environments. For example, an app developed for an iPhone cannot run on a Windows desktop PC or Android tablet. In some cases, however, emulation software can be installed on a host system to make it possible to run native apps written for another platform.
- Hybrid apps. The app combines elements of both native and web applications. The final application is, in effect, a web app wrapped in a native app shell that targets a specific environment. Hybrid app development frameworks enable developers to write a single codebase that can be used to create apps for multiple platforms. For example, a developer might build a hybrid app that runs on both iOS and Android devices. Hybrid apps are typically used for mobile devices.
- Progressive web apps. The app is built with modern web technologies such as HTML5 and JavaScript. It can run on any device with a supported browser. However, the app looks and behaves much like a native app. It can be used either online or offline and can often be published through a platform's app store. Progressive web apps have been growing in popularity and are now often used in place of native apps. They do not have full access to all native features and application programming interfaces, but in many cases, this might not be necessary.
- Desktop apps. This type of app is developed specifically for a desktop or laptop computer, such as a Windows PC, Apple MacBook or Linux desktop. Often the app will target specific hardware or operating system (OS) versions, or a combination of both.
- Mobile apps. The app is developed specifically for a mobile device platform, such as iOS or Android. Often the app will target specific hardware or OS versions, or a combination of both.
- Killer apps. A killer app in some way influences the adoption of a larger technology, such as computer hardware or an OS. For example, a successful video game can drive the sale of the specific game console that supports the game. VisiCalc, a spreadsheet program released in 1979, is often credited with being the first killer app because it drove the adoption of Apple II computers.
- Legacy apps. A legacy app is one that is outdated or obsolete. It might have been developed with an older programming language or built for an older platform. It might also have been based on technologies, standards or methodologies now seldom used. Organizations often continue to support legacy apps to meet critical business needs until the apps can be updated or other systems implemented to replace them.
An organization will often develop multiple apps that serve a similar purpose, but can accommodate different platforms. For example, Google offers the Gmail app for mobile devices, but maintains a web app for other devices. Evernote, however, provides apps for mobile and desktop devices, as well as maintains a web app to provide users with more flexibility when accessing their data.
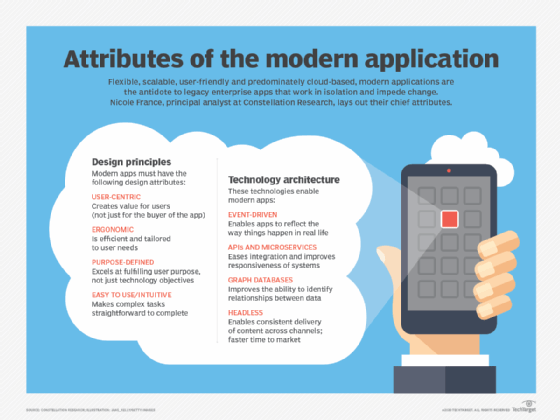
Learn about the rise of modern applications and why you need them. Explore a guide to open source technology in application development and check out the best web programming languages for development. Read more about application development and test your knowledge of mobile app programming languages.






