Microsoft Edge
What is Microsoft Edge?
Microsoft Edge is a cross-platform browser developed by Microsoft that's installed by default on all new Windows devices. The successor to Internet Explorer and IE Mobile, Edge is Microsoft's flagship browser that can be ported to Android OS, Apple iOS and macOS, Linux and older versions of Windows, including Windows 7 and later.
Microsoft Edge comes pre-installed on Windows 10, Windows 10 Mobile and Windows 11, as well as Xbox One, Series X and Series S consoles.
How does Microsoft Edge work?
In a major revamp in 2018, Microsoft rebuilt Edge from the ground up. This browser now operates on the Chromium Open Source code and the Blink web engine, which was developed by several companies, including Meta, Microsoft, Adobe, IBM and Intel. The Chromium engine offers impressive speeds and compatibility with many browser extensions. Microsoft Edge also operates as a built-in web viewer for applications requiring internet access through Android System WebView2.
The Google Chrome browser also runs on the Chromium engine.
Microsoft Edge features
Many new features have been introduced to Microsoft Edge since its redesign. The following are some popular Microsoft Edge features:
- Tracking prevention. Websites use trackers to collect data about a person's browsing history. Microsoft Edge's tracking protection function shields users from online monitoring by limiting trackers' access to network- and browser-based storage.
- Lightweight structure. Edge has trimmed back the bloat that most modern browsers, including IE, had. For example, it dropped support for ActiveX controls, which lack portability and are notorious for security issues. Edge is a streamlined browser built on web standards and designed for web services. It was code-named Spartan in development, a reference to the browser's lightweight structure, which is designed to make Edge functional across multiple, often mobile, device platforms.
- Support for inking. Microsoft Edge lets users add handwriting and drawings to webpages using an annotation tool. With the Web Notes feature, users can write on webpages, doodle, take notes, crop images and highlight text using their pen on a supported device, such as the Surface Pro tablet.
- Cortana. Microsoft Edge supports the Cortana personal virtual productivity assistant in Microsoft 365. It helps users with various tasks, including typing in response to voice commands, checking calendars, setting reminders and adding new tasks.
- Saving text snippets. The Collections feature keeps track of web links and stores video, images and snippets of text from websites, enabling users to quickly collect and organize information from the internet. It can also be used for tasks such as managing a shopping list, gathering research information and planning a trip. The Collections feature also syncs across all devices that have Microsoft Edge installed.
- Personalized content feed. Edge displays My Feed on startup, which is a collection of news stories, videos and snippets of information relevant to the user's browsing history and personal data, such as the location for weather reports. Users can also customize the feed according to their preferences.
- Private browsing. Microsoft Edge supports incognito browsing through InPrivate mode. The InPrivate feature opens a new, dedicated window that prevents browsing activity from being tracked by cookies and websites. Once the private browsing experience is closed in Edge, the browsing and download history -- along with cached passwords, images and autofill form data --are automatically erased.
- Read aloud. Microsoft Edge can read the text of a webpage audibly. Its control buttons can be used to pause and play the read-aloud cursor. Users can also move forward and backward using the same controls.
- Security. Microsoft Edge comes with many prebuilt security features, including Password Monitor, SmartScreen, InPrivate search and Kids Mode. The SmartScreen feature is designed to protect users from cyber threats, including malware, phishing and social engineering attacks. It generates a warning when a user accesses an unsafe website or download location.
- Gaming homepage. Edge comes with a personalized gaming homepage that's built with exclusive Xbox features. The page offers curated content geared toward gamers and their interests.
- Vertical tabs. Microsoft Edge provides the option to use vertical tabs. This feature enables users to move the traditional tab row at the top of the browser into a column that runs down the left side. Vertical tabs are less cluttered and easier on the hands, as users can slide from left to right instead of up and down while switching tabs.
- Browser extensions. Browser extensions are small applications that enhance the functionality of an app and add personalization. Microsoft Edge users can download their favorite extensions from the Microsoft Edge Add-ons store. For example, AdBlock for Edge, which is a popular ad blocker that automatically blocks ads, can be installed as an extension on Microsoft Edge.
- Immersive reading. Microsoft Edge displays an Immersive Reader icon on the side of the address bar whenever a user accesses certain content, such as articles and blog posts. This provides a cleaner and simpler view and is designed for easier reading.
Microsoft Edge development
Microsoft Edge was created for Windows 10 to replace IE, the browser that debuted with Windows 95 and was a part of Windows operating systems until its retirement on June 15, 2022.
On Feb. 14, 2023, Microsoft released an update that permanently disabled the defunct IE desktop program on select Windows 10 devices. However, Microsoft Edge continues to support IE mode until 2029. Bing, Edge's default search engine, is also using a more sophisticated version of the AI technology that enables ChatGPT in this edition. The icon for IE disappears in June 2023, but customers can continue using their legacy IE-based sites and apps.
Edge installs along with Windows 10 and Windows 11 much the same way IE did with previous versions.
Since the rebuild of Edge on the Chromium platform, the classic version of Edge that came pre-installed with Windows 10 is now called Microsoft Edge Legacy. Microsoft ended support for Edge Legacy on April 13, 2021.
Microsoft Edge vs. competitors
According to DataReportal's "Digital 2023: Global Overview Report," the average person spends almost seven hours each day on the internet, making browsers an essential part of the online world. While each browser offers unique browsing features, not all browsers are created equal.
According to StatCounter's "Browser Market Share Worldwide" study conducted in January 2023, Google Chrome has a global market share of 65.4%, making it the most used browser in the world. Apple's Safari takes second place with 18.7%. Microsoft Edge and Mozilla Firefox have a global share of 4.5% and 3%, respectively.
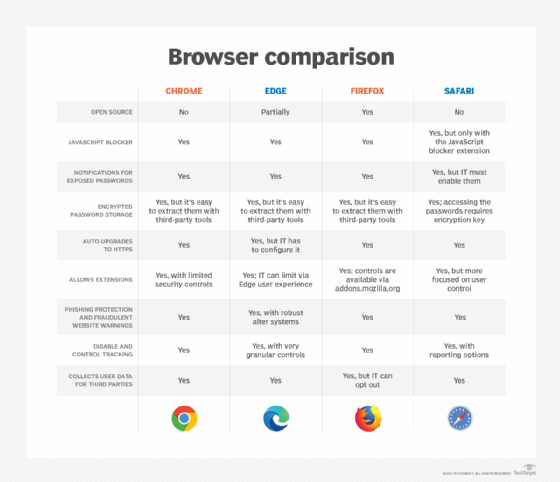
The following compares the features of Google Chrome, Apple Safari and Mozilla Firefox to understand how Microsoft Edge stacks up against its three biggest competitors.
Google Chrome
Chrome entered the browser market in 2008. Within a few years, it overtook Edge's precursor, IE, which, at the time, had a peak market share of 95%.
The following are key features of Google Chrome:
- Synchronization across devices.
- Tab groups that let users organize tabs into groups and collapse them in the tab bar to minimize space.
- Horizontal tabs that can provide a rapid overview of fewer tabs.
- Bookmarks that are synced to the user's Google account for all computers logged in to Google Chrome.
- A reading list that's similar to bookmarks and temporarily saves articles and websites.
- Browser extensions for adding features and functions to a browser.
- Browser history, or the list of websites that a user has recently visited.
- Themes, including dark mode.
- Password manager, a software app that stores and manages user credentials.
- Task manager for websites that displays usage statistics and enables the user to end individual processes when a website freezes.
- Private browsing, which involves the browser setting up a temporary session that's separate from the user data and the main session.
- Sidebar and price track panel.
Apple Safari
Safari debuted in 2003 as the default web browser for macOS. It's primarily based on open source software and WebKit. It has been the default browser on iOS since 2007. Designed with privacy and speed in mind, Apple Safari currently requires all third-party browsers to use WebKit engines.
Apple Safari offers the following key features:
- Intelligent tracking prevention that's designed to block third-party cookies.
- Sandboxing, which separates one tab from the others, ensuring that any malicious code performed from one tab won't affect other tabs or apps running outside of Safari.
- Fingerprinting protection that safeguards users from being followed by advertising.
- Autofill suggestions.
- Speed and battery optimization.
- 4K high dynamic range video playback and streaming for YouTube, Netflix and Apple TV+.
- Tab groups.
- Quick Note for taking notes in any app on an iPhone.
- Language translation.
- Visual lookup that helps identify popular landmarks and sites that appear in photos.
- Synchronization across devices.
- Privacy report, which details when Safari prevents trackers from following users across different websites.
Mozilla Firefox
Firefox is one of the earlier open source browsers and uses the Gecko rendering engine to display webpages. Firefox made recent improvements to protect user privacy and offers many advanced security updates and features.
Mozilla Firefox offers the following key features:
- Expanded dark mode.
- Private browsing windows.
- Unified search bar.
- Customizable menu or toolbar.
- Faster browsing speed.
- Ad tracker blocking.
- Password manager.
- Synchronization between devices.
- Picture-in-picture pop-out video.
- Fingerprint blocking.
- Browser extensions.
The transition from Microsoft's proprietary browser technology to the open source, Chromium-based engine has brought many improvements to the new Microsoft Edge browser. Learn what has changed between Edge and Chromium Edge, as well as any issues that users might encounter.
