uninterruptible power supply (UPS)
What is an uninterruptible power supply?
An uninterruptible power supply (UPS) is a device that allows a computer to keep running for at least a short time when incoming power is interrupted. As long as utility power is flowing, it also replenishes and maintains the energy storage. The more energy stored, the longer power can be maintained, with practical limitations that will be discussed later. The differences among UPS systems lies in the technology that enables them to do their jobs.
Energy can be stored in different ways. Rechargeable batteries are the most common. For simplicity the examples and illustrations in this article will be based on that technology. However, kinetic energy can also be stored in heavy, rotating flywheels or energy can be stored as fuel.
What are the different types of UPSes?
The most commonly used type of UPS is also the most effective, generally called a full-time or full double conversion UPS. For any UPS, incoming utility power is alternating current (AC), which is also what is required by most information technology equipment (ITE).
Batteries, on the other hand, are direct current (DC) devices, so all battery-type UPSes must convert -- or rectify -- the incoming AC power to DC to charge the batteries. The UPS must also still deliver AC to the ITE, so DC power must be converted back to AC through a device known as an inverter.
In a double conversion UPS, power flows continuously through the rectifier and then through the inverter to the ITE. The output voltage and frequency are completely isolated from, and independent of, the input voltage and frequency. They can even be completely different than the input, so this system is technically classified as voltage and frequency independent (VFI).
Voltage and frequency independent: Figure 1 below shows a VFI system in normal operation. Anomalies in the input power are dealt with in two ways. A surge suppression device (SPD) absorbs particularly bad voltage spikes. These can be caused by lightning strikes on power lines, large motors as used on elevators or medical electronics equipment; welders or numerous other sources. But even the smallest variations, including voltage sags or brownouts never make it through a VFI UPS to the output.
Batteries are excellent electrical shock absorbers, but they also maintain a steady and constant voltage to the inverter, which completely resynthesizes the voltage and current so that the power delivered to the ITE is clean and steady. Connecting air conditioners or other motors to the UPS serving the ITE could contaminate this clean output power, so it's not recommended.
Note the bypass circuit going around the UPS. We'll address that later.
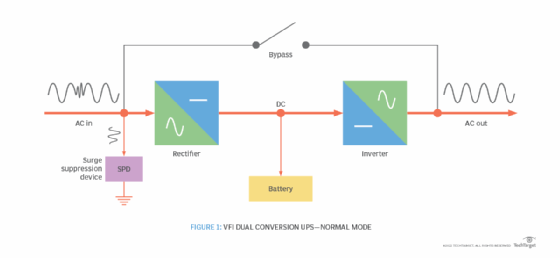
The battery is always in the circuit in normal operation, delivering small amounts of power when needed, such as during brownouts, so there isn't the slightest interruption in output power.
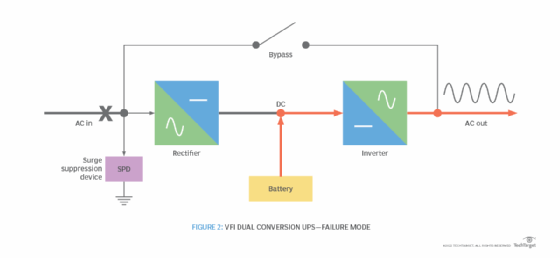
When utility power fails, as shown in Figure 2 below, the battery continues to deliver stored energy to the inverter, which continues to deliver clean power to the ITE. When utility power is restored, power flows back through the rectifier, feeds the inverter and recharges the batteries.
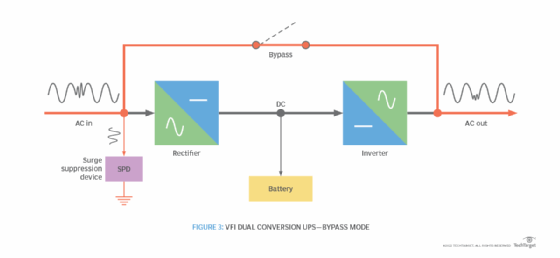
UPS static and maintenance bypass: UPSes are not uninterruptible. They are electrical or mechanical devices, so they not only require routine maintenance, but also are subject to component failures. For these reasons, all UPS systems have a built-in bypass to route incoming power around the system and directly to the ITE when necessary.
The high-quality SPD is still in the circuit but is only slightly better than running your home electronics on a power strip with surge protection. It won't stop utility power interruptions or deal with voltage sags or brownouts. If the UPS fails, the bypass operates immediately as a static switch.
When a technician must work on the system, the bypass is operated manually to render the internal components safe. If utility power fails while the UPS is in bypass, power to the ITE is interrupted. Any installation with only one UPS has this vulnerability. Figure 3 below shows the UPS in bypass mode.
Note that major spikes have been removed, but the voltage drop continues through.
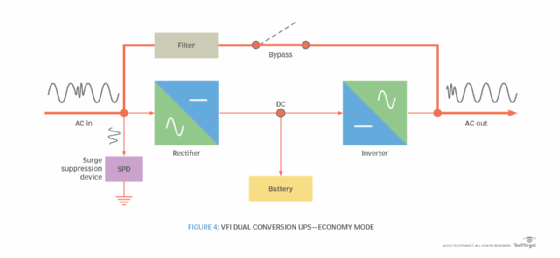
Economy mode operation: The first law of thermodynamics, conservation of energy, states that energy can be neither created nor destroyed. No electrical or mechanical device is 100% efficient, so every conversion incurs a loss, which escapes as heat.
UPS systems are far more efficient than a decade ago, and they maintain close to the same efficiency from low to high load. But there is still loss in both the rectifier and the inverter, which are eliminated when the UPS is in bypass mode. Many VFI UPSes now offer a sophisticated version of bypass known as economy mode (eco mode), as shown in Figure 4 below. An eco-mode UPS can return to full VFI operation when needed.
When rectifier and inverter losses are eliminated, power and cost are saved until power fails and full UPS operation is needed. Some users set the system for VFI operation during the day, and have it automatically switched to eco mode at night if those operations are considered less critical. Eco mode is generally highly dependable, but many users are leery of switching the modes back and forth. Further, new VFI UPS efficiencies are within 1% or less of what can be achieved in eco mode, so many users now consider this alternate operating mode unnecessary.
Note that eco mode UPSes incorporate high-quality filters, which also incur a small loss, and that there is usually a short instability when switching modes. Eco mode efficiency is statistical, but it can be 99% if power failures rarely occur and are short term.
Line interactive UPS: A true line interactive UPS, also known as voltage independent (VI), is called that because the output frequency is the same as the input. They look virtually identical to VFI UPSes in eco mode, except for the size of their rectifiers, and the inability to switch to VFI mode.
The smaller rectifier needs only to charge the batteries, which help absorb anomalies and boost power when there are voltage sags. The batteries take over completely when power fails. Figure 5 below shows how the battery and inverter help compensate for incoming voltage variations by running in parallel with the output.
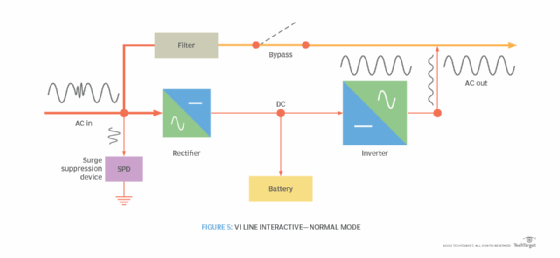
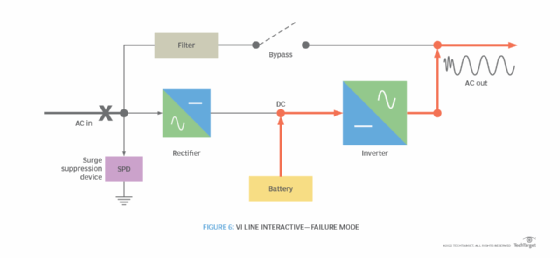
Figure 6 below shows a line interactive UPS when incoming service fails. The battery takes over, just as it would in a double conversion UPS, but the bypass switches the utility out of the circuit. Because the ITE runs on utility power most of the time, the second conversion through the inverter is avoided until power fails, eliminating one of the efficiency loss components.
A decade ago, VI UPSes could have an efficiency advantage of 5% or more over VFI units, but the huge improvements in VFI UPSes has reduced that to 1% or less.
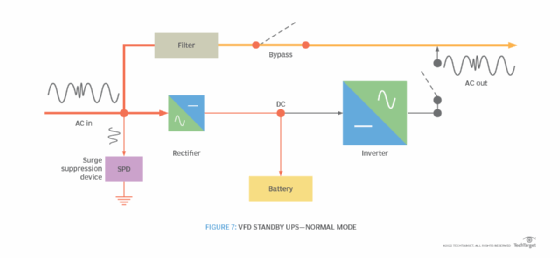
Standby UPS: Figure 7 below is usually called a standby UPS and is classified as voltage and frequency dependent (VFD). Like a VI UPS, power is delivered directly to the ITE, but the battery and inverter are not in the circuit until power fails. The output is filtered, but it isn't as stable as a true VI UPS.
As shown in Figure 8 below, when power fails, the utility is switched out of the circuit, and the battery and inverter are switched in. There is some switching instability, but the delay is short enough for most computer power supplies to ride through.
When power is restored -- either utility or generator -- the inverter is disconnected, line power is switched back in and the batteries are recharged by the rectifier, which is much smaller than in a VFI or VI UPS.
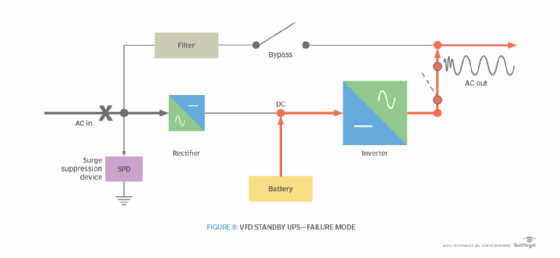
Unfortunately, standby or VFD UPSes are sometimes advertised as line interactive. It's important to be sure which type a UPS is. The internationally recognized VI and VFD identifications provide absolute distinctions, but aren't always used by manufacturers, particularly for smaller systems.
Mechanical and non-battery UPS systems
There are three major types of mechanical UPSes, two of which are also non-battery. All three are true VFI or double conversion systems, but the intermediate conversion is purely mechanical:
- Motor-generator (MG) sets combine a motor with a generator. The motor is equivalent to the rectifier in a VFI UPS, and the generator is equivalent to the inverter. Utility power drives a rectifier that runs a DC motor and charges the batteries. When power fails, the batteries keep the motor turning so the generator continues to deliver power to the load. MG sets are more often used to maintain power to other mechanical equipment, such as air conditioners, than to power actual ITE, although there was a time when they were quite prevalent with old mainframe computers.
- Diesel-rotary UPSes (DRUPS) are similar to MG sets except that there are no batteries -- other than for generator start -- and a built-in diesel engine starts and maintains power when a utility failure occurs. A flywheel keeps the generator turning long enough for the generator to stabilize before a mechanical clutch attaches it to the generator. Again, these tend to be used more to maintain power to air conditioners than to power the ITE. They are often selected as a cost-effective alternative to separate generators when uninterrupted cooling is particularly critical to maintain.
- Flywheel UPSes have similarities to both MG sets and DRUPS but with a major difference. The generator is turned by an electric motor when utility power is available, but the system incorporates only a heavy flywheel to keep the generator turning, usually until an auxiliary generator resumes power. The flywheel rides on nearly friction-free air or magnetic bearings in a vacuum-sealed case that can maintain power for as long as 30 seconds. Combined units can extend duration to several minutes without generating the heat common to other UPSes.
UPS power factor: Power factor (pf) is the difference between real power and apparent power. This is greatly misunderstood but very important for the buyer to know. Historically, most large UPSes had a pf of 0.8, which meant a 100 kilovolt-Ampere (kVA) UPS could only deliver 80 kilowatts (kW) of real power. Most of today's modern UPSes have pfs of 0.9 to 1.0, which means the real power in kW is much closer to, or even equal to, the apparent power in kVA.
Central vs. distributed UPS: Distributed UPS usually means small UPSes mounted in each equipment cabinet, although sometimes there is a UPS for each cabinet row. Small VFI UPSes exist, but many are VFD or VI designs, so it's important to know which technology is being purchased. Small, rack mounted UPSes often have pfs of only 0.7, so a UPS advertised as 1,000 kVA might only deliver 700 watts. These have their place, but usually in situations with only one or two equipment racks where a centralized, standalone UPS would be uneconomical.
Small, distributed UPSes aren't always maintained as well as larger systems, so failed batteries often go unrecognized until it's too late.
Considerations for selecting and using UPS systems
There are a couple important considerations for choosing a UPS system, including:
Modularity: Most modern battery-based UPSes are modular. They are comprised of multiple, smaller UPS and battery units that can be combined as required to provide capacity, redundancy or both. It's no longer necessary to over-buy in anticipation of long-term growth. The frame just has to be big enough for long-term expectations.
Actual modules can be purchased and installed as needed, and an additional module or two can be installed to provide redundancy. For example, a 100 kW UPS might have six 20 kW modules to provide N+1 redundancy. Battery capacity can be added modularly in the same way. Further, modules in most systems are hot swappable, so a failed module can be removed and returned to the factory and a replacement sent overnight for user installation without interrupting operations.
As noted above, Flywheel UPSes can also be modularly combined for increased size, run duration and/or redundancy. These, however, must be added and maintained by trained personnel.
Step function: When large loads are suddenly imposed on electrical equipment, power can become momentarily unstable, such as when power is restored to homes and the lights flicker or when large motors start and lights momentarily dim. This is of most concern when running 2N UPS redundancy, because failure of one UPS requires the second UPS to instantly absorb the total load.
It's also of concern in VFD UPSes where the full load is transferred to the inverter on power fail, and can be problematic in VI systems, or with systems operating in eco mode. In evaluating large UPS systems, it's important that the electrical engineer obtains transient load data from UPS vendors, compares it and explain the results to the owner.
Batteries and battery duration
Batteries are an evolving technology, particular because of their increased usage in electric vehicles. Batteries are heavy, so the floor structural strength should always be verified. Three types of batteries are in common use today:
- Flooded lead acid or wet cells are the most expensive but have the longest service life -- generally 25 years or more. However, they require separate, fire-rated rooms with acid drains, hydrogen detection alarms, exhaust fans, eye wash stations, deluge showers and hazmat protective gear. They are also the heaviest, require regular maintenance, and are generally used in the largest and most sophisticated installations.
- Valve regulated lead acid (VRLA), also known as sealed cells, use a paste electrolyte instead of liquid, and are contained in sealed packaging with small vents. They are charged more slowly than wet cells to avoid hydrogen emission, so can be used in any space without special construction or protection. Warranties are usually 10 years, but actual service life is often only 3-5 years depending on local power stability and how often the batteries are partially discharged and recharged. Longer life VRLA batteries are available at increased cost but must usually be specified. VRLAs are somewhat less heavy than wet cells.
- Lithium ion (Li-ion) are the newest batteries available and can be used without special rooms or construction in most jurisdictions. There might still be cities that consider them dangerous, but their chemistry and construction are totally different from those that have caught fire in ultra-compact electronics. Li-ion batteries are smaller and lighter than VRLAs, can be partially discharged and recharged without degradation and are expected to have a longer service life than VRLAs. However, they're still too new for long-term data.
Battery duration: UPS systems emit heat, regardless of battery type, so there's a limit to how long a UPS can operate without air conditioning. The actual limit depends on factors such as room size, other equipment and building heat load, but the generally accepted rule is 30 minutes to 60 minutes.
At some point the UPS will overheat and go into self-protective thermal shutdown. Therefore, without a generator to restart cooling, longer battery durations are a waste of space and money and greatly increase battery replacement cost, particularly when VRLA batteries are used. Failure of one battery requires replacement of the entire string or other cells will fail prematurely. If IT personnel are concerned about orderly shutdowns, that's better accomplished with a feature available on most large UPSes that sends a signal over the network to shut down ITE when battery life reaches a preset level.
With generators, UPSes are often configured with only a few minutes of battery. Quality generators should start and stabilize within seconds, but longer durations are sometimes requested to provide time in case generators fail to start. This should be unnecessary with redundant generators.
Battery strings: The most common UPS component to fail is a battery. Therefore, the best configuration uses at least two battery strings to provide the required duration.
Battery monitoring and maintenance: Many newer UPS systems incorporate third-party battery monitoring. If they don't, it should be specified as an added requirement. Batteries tend to fail when suddenly put under load, which is exactly when they're most needed. There are several types of monitors, with debate among manufacturers as to which is best, but any monitoring system will alert to weak or failed cells before disaster strikes. Wet cells require regular maintenance. Batteries should be replaced whenever monitoring indicates a weak cell.
Transformers and grounding: Note that there are no input or output transformers shown in the UPS illustrations. Transformers were once standard in electronic UPSes, but are now rarely seen, which accounts for a good deal of the efficiency improvement. Eliminating transformers has one other potential advantage and two potential disadvantages:
- Advantage. If input and output voltages are the same, there's no need for full wraparound bypass that would include the transformers, which the maintenance bypass doesn't.
- Disadvantage. If input and output voltages must be different, transformers aren't only required at either the input or output, but so is a full wraparound bypass that includes another transformer.
- Disadvantage. There is no output transformer to isolate the load from the UPS. Therefore, the electrical engineer must be particularly cautious in designing the grounding system and addressing the mitigation of fault conditions -- commonly called short circuits -- which can destroy UPS output transistors. This is often done with external distribution transformers in large power distribution units.
Considerations for low power quality and generators
VI and VFD UPSes can be problematic with unstable power. Because there are usually one or more flickers before power is restored solidly, these UPSes incorporate logic that keeps them from reverting to normal operation until power is stabilized.
VI and VFD UPSes shouldn't be used in locations with unstable power because they also incorporate a lock-out feature that prevents them from returning to normal if they switch back and forth too often, requiring manual restoration. The same problem can occur if generators are switched to the load too quickly, and wax and wane while trying to absorb the load.







