NAS gateway
What is a NAS gateway?
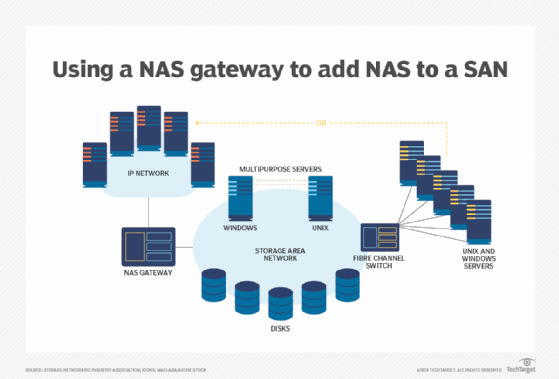
A NAS gateway is a NAS (network-attached storage) system in which the storage media are externally attached, typically over a Fibre Channel interface. The external storage might be connected by means of a SAN (storage area network), or it might comprise a standalone box shared among multiple servers.
With the use of a NAS gateway, all clients "see" the file serving function as a standard NAS device. The gateway appears as a single folder on every user's computer. If more storage is added to the system, the gateway retains its single-folder interface.
Theoretically, NAS gateways have unlimited storage capacity. This is a principal advantage compared with traditional disk arrays, although, beyond a certain point, a NAS gateway's performance degrades. A NAS gateway can also support Internet Small Computer System Interface, or iSCSI, an IP-based standard for linking data storage facilities.
NAS gateways have proven useful for networking applications in businesses of all sizes because they can be clustered. Clustered network NAS gateways sit in the data path between client servers and the storage arrays they access, acting as one logical server. A clustered file system bundles the different NAS gateway servers together so that each gateway can access storage anywhere in the cluster. This configuration enables storage resources to be scaled out and more options for storage capacity planning.
This article is part of
What is network-attached storage (NAS)? A complete guide
How does a NAS gateway work?
NAS gateways work in tandem with NAS appliances, but there are key functional distinctions between the two.
A NAS appliance combines a file server with a storage appliance. The NAS vendor's operating system (OS) software manages both components. Expanding file storage entails complex configuration when new NAS appliances join the network, an industry practice known as scale-up storage.
NAS gateways emerged to enable high-performance storage and scalability. With a storage gateway, data center and IT managers don't have to remap drives and file preferences to match end users' computers. The NAS OS manages the NAS gateway components, and the storage array software manages the physical array hardware.
Implementing a NAS gateway lets client machines consume NAS services locally but store data in highly resilient cloud storage at the network edge. NAS gateways are sometimes known as edge filers or caching arrays.
NAS gateway architecture explained
With a NAS gateway, NAS devices can seamlessly translate block data from a SAN and present it to clients as file data. All storage is presented to users using a single file folder interface. The gateway becomes a single network node to manage high-performance storage and make scalability easier.
Legacy NAS devices provide storage. By contrast, a NAS gateway contains no drives but instead enables authorized network users to share pools of NAS and SAN storage.
NAS gateways provide a translation layer between different networking models in a data center. When a NAS gateway is implemented, apps see all file storage in a single file folder and access it using Network File System (NFS) or Server Message Block file protocols.
On the front end, a NAS gateway device connects to client servers and application servers using an Ethernet-enabled local area network or a wide area network (WAN). Another common use is to deploy a NAS gateway across a WAN to front a SAN back end. This enables a large number of RAID arrays to interconnect across Fibre Channel (FC) switching technologies. Using a NAS gateway with this latter topology enables shared storage, boosts existing storage performance and aids scalability.
How are NAS gateways used?
IT organizations deploy NAS gateway technology to deliver a range of services, including the following:
- provide a file tier in front of a back-end SAN;
- scale SAN on an IP network;
- maximize existing FC storage investments;
- aid storage consolidation and capacity planning;
- distribute storage for dispersed work teams;
- improve business continuity and disaster recovery; and
- use the cloud as a scale-out object tier.
NAS gateways and object storage
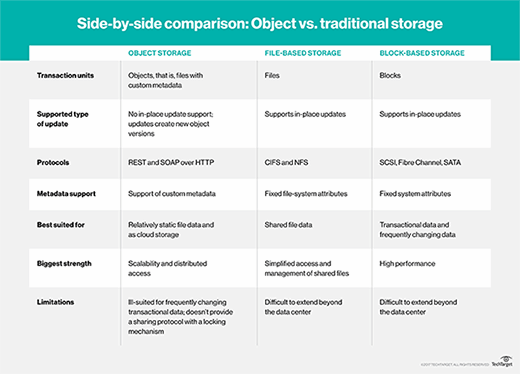
NAS storage systems implement a hierarchical file format, with applications writing data to NFS targets. NFS is well established, with modern OSes embedding a native NFS client to enable ease of use.
By contrast, object storage captures unstructured data, which does not adhere to a traditional file system. Massive scale is the defining characteristic of object storage. Instead of storing data in files and folders, it relies on metadata tables to describe attributes of the data, such as when it was created, by whom and where to access it.
While NFS is ubiquitous, object storage writes data to an Amazon Simple Storage Service (S3) client. To address the gap, storage vendors developed NFS gateway technology to bridge legacy and object storage-based cloud applications. The gateway accepts files from NFS and stores that data in an object system.
Cloud NAS gateways
A cloud storage gateway is a NAS appliance that bridges local storage to data residing in a hybrid cloud. Cloud gateways are installed either as hardware devices or virtual machines.
A cloud gateway translates block and file commands to a cloud repository via representational state transfer application programming interfaces. Using a virtualized NAS appliance, which caches frequently accessed apps, speeds up data transfer.
Most cloud NAS gateways include a storage system, backup and data protection, distributed file services and native data security. For optimal performance, a cloud NAS gateway requires sufficient bandwidth to reduce latency when translating legacy data protocols to the cloud.
NAS gateway providers
Some of the vendors and products that provide NAS gateways are the following:
- AWS Storage Gateway permits customers to use Amazon Web Services as a local appliance to transfer data from the data center to Amazon storage.
- Buurst SoftNAS is a virtual cloud appliance that provides unified block, file and S3 object storage with enterprise-grade data protection.
- Ctera Edge Filer hardware includes a cloud file system, integrated file sync-and-share capabilities and source-side data reduction.
- Hammerspace does not sell a NAS gateway, but it offers Global Data Environment NAS management as a service to make structured and unstructured data visible in a single view.
- Microsoft StorSimple NAS gateway hardware is integrated in the Microsoft Azure suite of cloud-based storage devices.
- Morro Data Edge Gateway is powered by its Global File System to manage file locking, permission sharing and versioning.
- Nasuni software-defined storage filers run the UniFS global file system to support massive scaling of file storage in the public cloud.
Find out more about the advantages and disadvantages of using NAS.
