search operator
What is a search operator?
A search operator -- sometimes referred to as a search parameter -- is a character or string of characters used in a search engine query to narrow the focus of the search.
In mathematics and computer science, operators are characters or sequences of characters that represent an action or cause an action to be performed.
A typical search can return hundreds, even thousands, of results that might include responses with little or no relevance to the intended search goals. Search operators add and combine more specific details to the search terms included in a query; this helps improve query efficiency and effectiveness.
Consider a simple example: Using the word music in a query will return countless results involving styles of music, types of music, artists, publishing and other relevant topics. Search operators refine the query to be more detailed, generating search results that are more specific and relevant. Search operators can create a more detailed query that combines desired music types, artists and even song names to elicit more specific results.
How do search operators work?
Search operators represent logical or other specific relationships used to combine or restrict search words. Boolean operators are commonly used in search. For example, AND indicates that website pages in the results must contain both the word or phrase preceding the word and as well as the word or phrase following it. NOT indicates that pages in search results shouldn't contain the word or phrase after it. OR indicates that the pages should include any of the terms on either side in the query rather than pages that contain both or all terms.
Consider finding a restaurant. Searching simply restaurant yields a bewildering array of establishments, cuisines and locations. By narrowing the search using search operators, it can be better targeted. Let's say you're in the mood for sushi somewhere in the vicinity of Worcester, Mass. Your search query could look like restaurant AND sushi AND worcester AND massachusetts or restaurant+sushi+worcester+massachusetts. Either approach narrows the results to sushi restaurants around Worcester, Mass.
Where are search operators used?
Search operators are used along with desired search terms. They're entered into the search bar of a search engine such as Microsoft Bing or Google.
Search operators are usually placed between keywords or directly in front of a query word or phrase with no intervening space. Multiple operators can be combined in a query to further narrow the focus of a search.
What are some types of search operators?
The most common search operators are Boolean relationships, including AND, OR and NOT, as well as simple wildcard operators, like an asterisk, parentheses or quotation marks, which indicate the searcher is looking for an exact match. Search engines typically provide a variety of advanced search operators designed to provide powerful search capabilities.
Here are a few examples of Google advanced search operators:
- site: is an operator that when followed by a website or domain, without a space, returns files located there.
- filetype: when followed by a file extension, such as DOC, PDF, XLS and INI, returns files of the specified type. Multiple file types can be searched for simultaneously by separating extensions with the vertical line symbol, as in the query filetype:DOC|PDF. The ext: operator, short for file extension, performs the same job.
- inurl: when followed by a particular string, returns results with that sequence of characters in the URL.
- allinurl: is used to search for webpages that contain multiple specific words in the URL.
- intext: when followed by the searcher's chosen word or phrase returns files with the string anywhere in the text.
- allintext: searches for webpages that contain multiple specific words in the pages.
- related: looks for websites that are related to a particular domain, such as techtarget.com.
- intitle: looks for webpages that contain a specific word in the page title.
- allintitle: searches for webpages that contain multiple specified words in the title.
Other Google search operators include inanchor: and allinanchor: when searching for pages with backlinks using specific anchor text, loc: for location and daterange: for searching a specific date range, but they return results that aren't as reliable.
Search operators can be combined in a search query to fine-tune a search. A complex search engine query, sometimes referred to as a Google dork query, can be used to find information that a site owner hasn't purposefully made available. The practice, also known as Google hacking, is often recommended as a way to discover site vulnerabilities that need attention.
Examples of how search operators are used
Students, researchers and various professionals use search operators to locate relevant information of interest. Common Boolean operators are particularly handy for narrowing search results by adding or subtracting details from the search query.
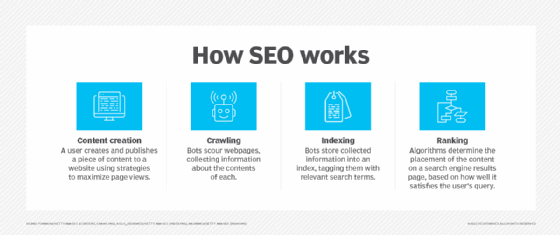
However, advanced search operators are also powerful tools for website designers and business experts seeking to master the nuances of search engine optimization. SEO is a technology and marketing discipline oriented to enhancing the search results of one or more owned website properties.
For example, someone researching competitors or supporting information for a specific site might use the related: operator, such as in the query related:firefox.com.
This query returns a list of results related to the firefox.com domain. Similarly, using the site: operator will return a list of pages on the specified site, as in the query site:firefox.com. This lets users see all the pages on a site without having to browse the site itself.
Users seeking webpages with specific words in the URL can use the inurl:, allinurl: or allintitle: operators to check results. For example, if a user were interested in flipping old homes, they might search for websites with a query such as allinurl:flipping old homes or allintitle:flipping old homes.
Such commands can offer insights on specific websites of interest and help identify possible indexing issues with pages on an owned website. Indexing is one of many considerations an SEO strategy might address in trying to keep up with search engine algorithms and advance the goals of an owned website.
Search operator best practices
Search engines, and the algorithms that drive them, are always evolving. While most search efforts require some amount of trial and error, there are best practices that can help save time and reduce search frustration.
- Avoid simple or common keywords. Operators are helpful, but they aren't magic. Using more specific, relevant keywords will narrow a search more effectively than using longer search strings. For example, allintext:hello is virtually useless, while allintext:hello adele lyrics will immediately show the lyrics for music artist Adele's popular song from 2015.
- Remember that common words rank low. Another problem with common words is that they're used so often and broadly that they rank poorly and are frequently lost in search results. Select more relevant or industry-specific words. For example, an electronic engineer might prefer to search the word capacitor rather than its older, simpler term, condenser.
- Capitalize Boolean operators. Operators such as AND, OR and NOT should be entered using uppercase letters. Lowercase operators are often treated as keywords rather than operators.
- Understand case sensitivity. While it's helpful to capitalize Boolean operators, keywords can be entered as upper- or lowercase and are not case-sensitive.
- Eliminate space after advanced operators. Do not use a space after the colon of an advanced operator. For example, related:firefox.com is preferable to related: firefox.com.
Remember that there is no substitute for experimentation. Whether looking for web content created by others or testing your own web content, it's worth trying different operators in different ways to see how search results compare.
Learn the techniques that various companies have used to improve search capabilities of their organizations.