audio
What is audio?
Audio is sound that is within the acoustic range of human hearing. It is the audible portion on the spectrum of sound frequencies, distinct from inaudible sounds heard by certain animals or used in science and medicine. An elephant, for example, can hear sounds at lower frequencies than humans, and porpoises can hear sounds at higher frequencies. In both cases, they hear sounds that fall outside the range of human hearing.
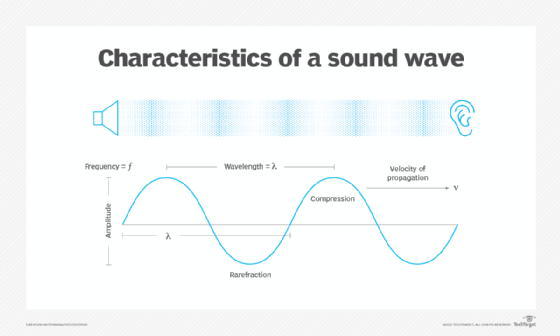
Sound is a form of mechanical energy that travels in waves through air and other substances. It is measured in hertz (Hz), with one Hz equal to one full wave cycle per second. Humans can hear only a portion of the full spectrum of sound frequencies. The audio portion is typically between 20 to 20,000 Hz, but aging and hearing damage can shorten this range.
Although audio has a distinct meaning in relation to sound, the term is often associated with computing and other electronic devices. Within this context, audio refers to the field of technology concerned with recording, processing, storing and delivering audible sound using electricity. Most computers, for example, now support vocal interaction through a microphone audio file, can store and run sound audio files in multiple formats, and can deliver sounds through speakers or headphones. These features represent a computer's audio capabilities.
How is audible sound produced and transmitted?
Audible sound is produced by using electricity and is transmitted as either analog or digital signals:
- This form of audio uses alternating current (AC) voltage to create a signal that coincides with the frequencies and amplitudes of the original soundwaves. An analog signal can be transmitted between devices or recorded on a medium such as vinyl or tape. The signal moves in a continuous series of waves, just like a soundwave. In fact, sound is considered a naturally occurring mechanical wave in an analog format.
- This type of audio is a representation of sound that approximates a soundwave's patterns. The sound data is transmitted and recorded as bits (1s and 0s) and stored as binary files on devices such as flash drives, DVDs or Blu-ray discs. Digital sound data is often converted from analog to digital or from digital to analog, using devices such as analog-to-digital converters (ADCs) or digital-to-analog converters (DACs). For example, an analog signal might be captured through a microphone, converted to a digital signal, stored as a binary file, and then converted back to analog when played over a set of speakers. Most computers include sound cards that contain ADC and DAC converters.
How is digital audio content stored?
Today, most audio content is stored as digital data, even if its original storage format is analog, as is often the case in professional recording studios. The digital trend has given rise to a wide range of audio file types, such as those shown in the table:
| File type | Compressed | Lossless |
| Advanced Audio Coding (AAC) |
Yes |
No |
| Apple Lossless Audio Codec (ALAC) |
Yes |
Yes |
| Audio Interchange File Format (AIFF) |
No |
Yes |
| Free Lossless Audio Codec (FLAC) |
Yes |
Yes |
| MPEG-1 Audio Layer 3 (MP3) |
Yes |
No |
| Ogg Vorbis (OGG) |
Yes |
No |
| Pulse-Code Modulation (PCM) |
No |
Yes |
| Waveform Audio File Format (WAV) |
No |
Yes |
| Windows Media Audio (WMA) |
Yes |
No |
| Windows Media Audio Lossless (WMA Lossless) |
Yes |
Yes |
The Compressed column indicates whether the data is compressed when stored in the specific file format. The Lossless column indicates whether data is lost from its original uncompressed state when converted to that format. If the file type is lossless, the data is preserved, otherwise it is considered lossy, which can affect sound quality.
The table does not show all audio file types; however, the ones included here represent the more common types in use today. These formats also illustrate the variety of file types supported by the audio industry, a list that continues to evolve as the industry enhances and introduces new technologies.
See also: audio frequency, dynamic range, harmonic, A-weighted decibel, bone conduction headphones, sample rate and latency
