POODLE Attack
What is a POODLE attack?
The POODLE attack, also known as CVE-2014-3566, is an exploit used to steal information from secure connections, including cookies, passwords and any of the other type of browser data that gets encrypted as a result of the secure sockets layer (SSL) protocol.
In October 2014, the United States Computer Emergency Readiness Team (US-CERT) issued an advisory about a vulnerability associated with the encryption that protects internet traffic. The security flaw, POODLE (Padding Oracle On Downgraded Legacy Encryption), allows attackers to decrypt network traffic between a client and a server.
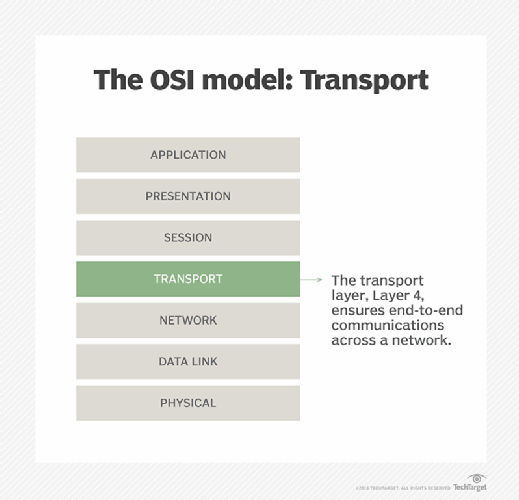
SSL 3.0 and SSL 2.0, older versions of the Transport Layer Security (TLS) protocol used to encrypt and authenticate data sent over the internet, are vulnerable to POODLE attacks. In addition, while the industry deprecated these protocols -- replacing them with newer and more secure TLS connections -- a small number of browsers still support SSL. An attacker attempting to exploit POODLE can force these browsers to downgrade to SSL 3.0 when TLS is unavailable by inserting themselves into the communication session.
How do POODLE attacks work?
The POODLE security flaw enables a man-in-the-middle (MiTM) attacker to eavesdrop on supposedly secure communications. This means attackers can exploit POODLE to steal users' private information and -- possibly -- impersonate the user, resulting in the user losing control over the exploited web application.
A POODLE attack is not simple to employ and requires success at each of the following three stages:
- In the initial stage, an attacker gains access to victims' sensitive data by performing a successful MiTM attack. An MiTM attack is a form of active eavesdropping where an attacker surreptitiously inserts themselves between two parties communicating over the internet to intercept and relay messages to and from them. So, while the victims believe they are talking directly to each other over a private connection, the attacker is in fact controlling the entire conversation.
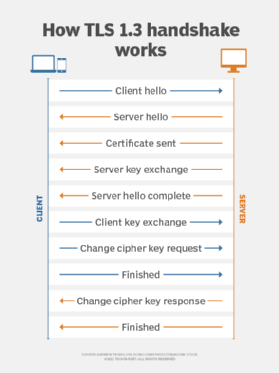
- During the second stage, the attacker forces the server to switch to SSL 3.0 protocol. They do this by continually dropping connections during the MiTM attack until the service switches to an older protocol if it is not possible to switch to a newer protocol such as TLS 1.2. This stage of the POODLE attack is known as the downgrade attack.
- Once the server switches to SSL 3.0, the attacker uses POODLE to retrieve information from encrypted packets. This means they can intercept the vulnerable client's session and view the information in unencrypted data as plaintext.
How to prevent and repair POODLE attacks
Any server that supports SSL 3.0 and older versions of TLS is vulnerable to a POODLE attack. Modern versions of TLS are safe, and today's browsers block sites that use old versions of TLS (1.0, 1.1). A server configured to support only newer protocols (TLS 1.2, 1.3) prevents the possibility of a POODLE attack.
What is the POODLE vulnerability?
The POODLE vulnerability impacts certain cipher suites defined within a security protocol, including TLS and SSL. Cipher suites are cryptographic algorithms and key exchange methods used to establish secure connections between a client and a server. When block ciphers encrypt cipher suites, a private and public key is generated using asymmetric encryption. The communication between the user and server uses the key for encryption.
The POODLE attack relies on victims using the least secure encryption mode possible: cipher-block chaining (CBC) mode. CBC mode is a message encryption mode for block ciphers. In this mode, each block is XORed with the previous ciphertext block before encryption. In cryptography, the XOR logical operator applied to two equal-length strings yields a result that has the same length as the operands.
What is padding?
In cryptography, padding -- the P in POODLE attack -- refers to data added to plaintext before encryption. Padding is necessary to prevent a cipher from being vulnerable to a known plaintext attack.
In the context of SSL/TLS (HTTPS) connections, padding ensures the length of the plaintext transmitted over an encrypted connection is a multiple of the cipher block size as required in block cipher algorithms. Cryptographers refer to the process of adding padding as "padding" or "padding oracle."
A padding oracle on CBC mode encryption allows a passive attacker to decrypt ciphertext without knowing the encryption key or even the plaintext. The attacker modifies encrypted data, and the server responds with an error message indicating that either the padding or message authentication code (MAC) is incorrect. By knowing that the same plaintext was encrypted using the same initialization vector (IV), an attacker is able to determine the plaintext bytes size with a high probability.
MAC-then-encrypt. The SSL/TLS protocol secures data exchanged over the network and ensures the integrity of data in transit. MAC, on the other hand, is a cryptographic technique -- sometimes referred to as a cryptographic hash -- used to verify no one has altered a message. The MAC-then-encrypt process calculates and inserts the MAC value, then encrypts data and padding before sending it to another computer.
History of SSL and TLS protocols
SSL and TLS are both established protocols for encrypting connections over the internet. Created by Netscape in the early 1990s, SSL served as a way to secure communication over the internet and make sure that data was authentic. TLS today serves as a more secure replacement for SSL.
A timeline of SSL and TSL development:
- SSL 2.0. Released in 1995, this version of SSL is now prohibited by the Internet Engineering Task Force (see RFC-6176).
- SSL 3.0. Released in 1996, SSL 3.0 is deprecated, but a few browsers still support it (RFC-7568).
- TLS 1.0. Released in 1999 and deprecated in 2020.
- TLS 1.1. Released in 2006 and deprecated in 2020.
- TLS 1.2. Released in 2008 and still has no security issues.
- TLS 1.3. Released in 2018 and continues to be the main protocol used today without any known vulnerabilities.
Other SSL/TLS vulnerabilities
A POODLE attack is not the only SSL/TLS vulnerability. Others include the following:
BEAST attack (CVE-2011-3389) vulnerability is a form of MiTM attack that uses a CBC algorithm in order to exploit vulnerabilities in a browser's implementation of the SSL/TLS protocols.
SWEET32 attack (CVE-2016-2183) vulnerability is a plaintext recovery attack on 64-bit block ciphers in CBC mode.