POP3 (Post Office Protocol 3)
What is POP3 (Post Office Protocol 3)?
Post Office Protocol 3, or POP3, is the most commonly used protocol for receiving email over the internet. This standard protocol, which most email servers and their clients support, is used to receive emails from a remote server and send to a local client.
POP3 is a one-way client-server protocol in which email is received and held on the email server. The "3" refers to the third version of the original POP protocol.
A recipient or their email client can download mail periodically from the server using POP3. Thus, POP3 offers a means of downloading email from a server to the client so the recipient can view the email offline. POP3 can be thought of as a "store-and-forward" service.
Once the email is on the client, POP3 then deletes it from the server. With some implementations, users or an administrator can specify that mail be saved for some time, allowing users to download email as many times as they wish within the specified period.
POP3 and email applications
POP3 is built into most popular email clients, including Microsoft Outlook. The protocol will work provided that the email program is configured to host POP3. Each POP3 mail server has a different address that must be entered into the email program for it to connect with the protocol. Users must also enter their username and password to receive email successfully.
Additionally, since POP3 is built into standard internet browsers, including Internet Explorer and Mozilla Thunderbird, users can check their email even without an email client.
POP3 ports
POP3 works on the following two ports by default:
- port 110: default, non-encrypted port; and
- port 995: should be used when the user needs to connect using POP3 securely.
How POP3 operates
The server starts POP3 service by listening on TCP port 110. When a client wishes to use POP3 for email retrieval, it establishes a TCP connection with the server host. Once this connection is established, the POP3 server sends a greeting. At this point, the session enters the authorization state.
In the transaction state that follows, the client and server exchange commands and responses until the connection is either closed or aborted. Commands from the client consist of case-insensitive keywords, possibly followed by arguments. Responses from the server consist of a status indicator and a keyword, which may be followed by additional information.
When the client issues the quit command, the session enters the update state. The POP3 server releases any resources acquired during the transaction state, and says "goodbye," which is when the TCP connection is closed.
After the POP3 session enters the update state, the POP3 server deletes the message.
Advantages and limitations of POP3
Although POP3 has been enhanced many times since it originated in the late 1980s, it remains popular because of its simplicity. Another reason for its ubiquity is that it enables email to be retrieved efficiently with minimal errors.
The protocol is ideal when users need to access their email offline and they use a designated device for retrieval. POP3 is also useful for sending and storing bulk email messages.
POP3 is not intended to support email manipulation or synchronization on the server, since the email is meant to be downloaded to the client and then deleted from the server. For these use cases, the more advanced and complex Internet Message Access Protocol (IMAP) is used.
IMAP can also poll an existing connection for newly arrived messages, and it supports multiple folders on the server. POP3 doesn't have these capabilities.
How are POP3, IMAP and SMTP related?
IMAP is an alternative email retrieval protocol. Similar to a remote file server, IMAP allows the user to retain email on the server, where the email can be organized in folders.
Like POP3, IMAP is supported by all modern email clients and web servers. But unlike POP3, IMAP also synchronizes the email across multiple devices or clients, making it more suitable than POP3 when a user is working with many devices or wants to access email from multiple locations. IMAP works on ports 143 and 993.
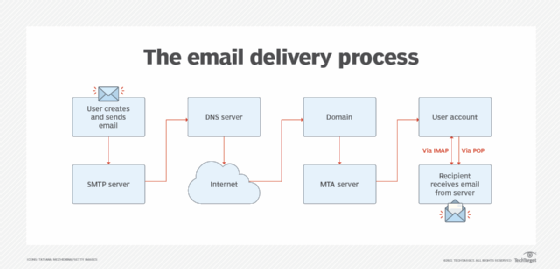
POP3 and IMAP both pertain to the receipt of email but differ from the Simple Mail Transfer Protocol (SMTP), a protocol for transferring email across the internet. SMTP sends email, a mail handler receives it on the recipient's behalf, and the mail is read using POP3 or IMAP.
