POSIX (Portable Operating System Interface)
What is POSIX (Portable Operating System Interface)?
POSIX (Portable Operating System Interface) is a set of standard operating system interfaces based on the Unix operating system. The most recent POSIX specifications -- IEEE Std 1003.1-2017 -- defines a standard interface and environment that can be used by an operating system (OS) to provide access to POSIX-compliant applications. The standard also defines a command interpreter (shell) and common utility programs. POSIX supports application portability at the source code level so applications can be built to run on any POSIX-compliant OS.
A brief history of the POSIX standard
The POSIX interfaces were originally developed under the auspices of IEEE. However, the POSIX standard is now being developed and maintained by the Austin Common Standards Revision Group, commonly referred to as the Austin Group.
The Austin Group is a joint working group made up of members from IEEE, The Open Group and Joint Technical Committee 1 of the International Organization for Standardization (ISO) and International Electrotechnical Commission (IEC). IEEE owns the POSIX trademark. The Open Group, which owns the Unix trademark, is a global consortium that develops technology standards.
POSIX emerged out of a need to make applications more portable across diverse systems. In the early days of computing, programmers had to rewrite their applications for each computer model and OS. This started to change when IBM introduced its line of System/360 computers, which could all run the same OS, OS/360. With these new systems, applications could be made more portable, saving enormous amounts of development time.
Soon after, Unix entered the scene and introduced an even greater potential for application portability. Unlike other OSes, Unix could run on machines from different vendors. However, multiple variations of the OS soon appeared, and the promise of portability quickly faded. Even so, Unix continued to grow in popularity, and it soon became apparent that some type of standard was needed to meet the challenges of application compatibility. That need led to the development of the POSIX specifications. Released in 1988, the first standard was based on AT&T Unix System V and Berkeley Software Distribution Unix, the two most prominent Unix systems at the time.
What is the POSIX standard?
Over the years, the POSIX specifications have continued to be revised and reorganized. At one time, each standard was informally named POSIX, followed by a decimal and then the standard's number. For example, POSIX.1 was the standard for an application programming interface in the C language, and POSIX.2 was the standard shell and utility interface for the OS. These standards were officially named IEEE Std 1003.1 and IEEE Std 1003.2, respectively.
There were also amendments to the base standard, such as IEEE Std 1003.1b-1993, which dealt with real-time extensions. However, all the various specifications have been rolled into one standard -- IEEE Std 1003.1 -- which was last updated in 2017 and published in 2018. Officially, it is called IEEE Std 1003.1-2017. However, it is also referred to as POSIX.1-2017 or, more informally, POSIX.1.
The POSIX standard goes by other names as well. The Open Group calls it The Open Group Base Specifications Issue 7, 2018 edition, and ISO/IEC refer to it as ISO/IEC 9945:2009. ISO/IEC adopted the standard in 2009 and added Technical Corrigendum 1 in late 2012 and Technical Corrigendum 2 in March 2017, putting it on par with IEEE Std 1003.1-2017.
The POSIX.1-2017 specifications define the fundamental services needed to build POSIX-compliant applications. They establish standard semantics and syntax to help developers write portable applications. POSIX.1 is made up of the following four volumes:
- Base definitions. Provides common definitions for the specifications, including information about terms, concepts, syntax, service functions and command-line
- System interfaces. Provides details about interface-related terms and concepts, and defines the functional interfaces available to applications accessing POSIX-conformant systems.
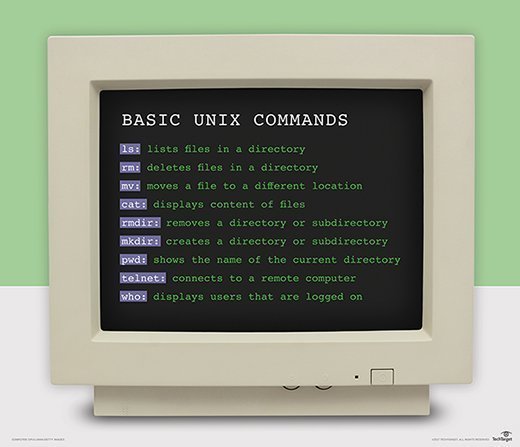
- Shell and utilities. Describes the commands and utilities available to applications accessing POSIX-conformant systems, including the command language used in those systems.
- Rationale. Includes historical information about the standard's contents and why certain features were added or removed.
POSIX.1 takes a "write once, adopt everywhere" approach to the specifications by providing a set of fundamental services needed to efficiently build applications. The standard emphasizes the facilities and characteristics that are important to application development, rather than focusing on the techniques needed to achieve these capabilities. The POSIX standard is intended to be used by both system implementors and application developers.
Linux, which evolved from Unix, can be tricky to learn. Explore the main Linux components to better understand the OS.
