Photoshop
What is Photoshop?
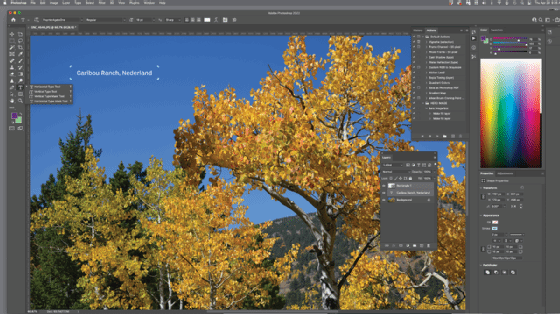
Photoshop is an image creation, graphic design and photo editing software developed by Adobe. The software provides many image editing features for pixel-based images, raster graphics and vector graphics.
Adobe Photoshop was first released in 1988. Created by Thomas and John Knoll, it was initially developed for Macintosh computers but is now available for Windows and macOS platforms.
Photoshop is part of the Adobe Creative Cloud, which includes other popular tools such as Adobe Illustrator, Photoshop Lightroom and Adobe Dreamweaver. Photoshop Creative Cloud allows users to work on image and graphic content from anywhere.
How does Photoshop work?
Photoshop has been the industry standard image manipulation program for so long that its name has become a verb. It is common parlance to say that an image has been "photoshopped," or even just "shopped," meaning that it's been edited or manipulated.
It uses a layer-based editing system that enables raster image creation and altering with multiple overlays that support transparency.
Layers can also act as masks or filters, changing underlying colors. Shadows and other effects can be added to the layers.
Adobe promotes Photoshop as a tool for professionals. However, beginners can use Photoshop as well with many helpful tutorials on the market that train users in how to use Photoshop's various features.
What are Photoshop's features?
Photoshop comes with a multitude of features, fonts, effects, and brush or pen tools. Here are some of the most common ones:
- Brushes are one of the most popular tools in Photoshop. They can be used for various effects, including compositing, painting, erasing and retouching images.
- The Clone Stamp allows you to copy pixels from one area of an image and paste them into another area. This is useful for repairing damaged or corrupt images.
- The Healing Brush is similar to the Clone Stamp, but it blends the copied pixels with the surrounding pixels for a more natural look.
- The History Brush allows you to revert an image to a previous state. This is useful for undoing mistakes or going back to a point in your workflow where you were happy with the image.
- Blur blurs the pixels in an image, making them less distinct. This can be used to create a soft, dreamy look or reduce the appearance of wrinkles and other imperfections.
- Sharpen does the opposite of Blur, making pixels more distinct. This can be useful for making an image appear more transparent or creating a more dramatic effect.
- Dodge and Burn are used to lighten or darken areas of an image. These are commonly used in photo retouching to make subjects appear more defined.
- The Sponge tool can either absorb or release color from an image. This is useful for correcting colors that are too light or too dark.
What is the most recent version of Photoshop?
The most recent version, Photoshop 2022 (desktop), is version 23.3.1 released in April 2022, while Adobe released the latest cloud version in October of 2021.
The newest edition of Photoshop updated copy-paste support from Illustrator to Photoshop, making it easier to move text layers and other typographic properties. Adobe has also improved the quality along edges in objects in its Sky Replacement feature. More enhancements include the addition of multithreaded and GPU compositing options for faster performance, the ability to search cloud documents in recents and improvements in Photoshop's saving preferences.
Adobe has also removed the camera shake reduction function due to incompatibly with newer development platforms and the quick share feature due to lack of use. The company has, however, added support for additional cameras and lenses.
Recent versions of Photoshop also include features such as an object selection tool, a properties panel, updated keyboard shortcuts for paint and brush, an enhanced transform warp and a background image removal option.
They also incorporate some administrative functions such as automation features to reduce the need for repetitive tasks.
Photoshop's feature set can be further expanded through Photoshop plug-ins which are programs developed and distributed independently of Photoshop that can run inside and offer new or enhanced features.
Who uses Photoshop?
Photographers, graphic designers, web designers, Discord emoji creators and meme-makers all use Photoshop to edit images, create new high-quality images, or both.
The software is available for a monthly fee from Adobe or as part of the Adobe Creative Cloud subscription service.
Adobe Photoshop Elements is an alternative to traditional Photoshop. It is a graphics editor for photographers, image editors and hobbyists. It contains most of the features of the professional version but with fewer features and a simpler user interface.
Gimp is an open source alternative to Photoshop that works on macOS, Microsoft Windows and Linux.
What types of projects are best for Photoshop?
Photoshop is ideal for creating graphics and layouts for print projects such as newspapers, magazines and posters. The software can also create website designs, logos and other digital art.
Images edited in Photoshop can be saved in various file formats, including those suitable for the web (JPEG, PNG, GIF) or printing (TIFF).
