QWERTY keyboard
What is the QWERTY keyboard?
The QWERTY (pronounced KWEHR-tee) keyboard is the standard typewriter and computer keyboard in countries that use a Latin-based alphabet. QWERTY refers to the first six letters on the upper row of the keyboard.
The key arrangement was devised by Christopher Latham Sholes, whose Type-Writer, as it was then called, was first mass-produced in 1874. Since that time, it has become what may be the most ubiquitous machine-user interface of all time.
Why was the QWERTY keyboard created?
The QWERTY arrangement was intended to reduce the jamming of typebars as they moved to strike ink on paper. Separating certain letters from each other on the keyboard reduced the amount of jamming.
In 1932, August Dvorak developed what was intended to be a faster keyboard, putting the vowels and the five most common consonants in the middle row, with the idea that an alternating rhythm would be established between left and right hands.
Although the Dvorak keyboard has many adherents, it has never overcome the culture of learning to type on a QWERTY keyboard.
_mobile.jpg)
The benefits of using a QWERTY keyboard
The QWERTY layout quickly became the standard for typewriters and has remained so for computers and other digital devices to this day. There are a number of variations of the QWERTY layout, depending on the language and region, but the basic arrangement of the keys is generally the same.
One of the main advantages of the QWERTY layout is that it is easy to learn and use. Most people who have used a computer or typewriter are familiar with the layout, and it is generally considered to be intuitive and efficient.
Another advantage of QWERTY keyboards is that they are widely available and relatively cheap, making them a popular choice for both personal and professional use.
The challenges of using a QWERTY keyboard
There are, however, some criticisms of the QWERTY layout. Some people argue that it is not the most efficient or ergonomic layout and that other keyboard layouts, such as the aforementioned Dvorak or Colemak layouts, may be superior in terms of speed and comfort.
While these layouts have their supporters, they have not gained widespread adoption, and the QWERTY layout remains the dominant standard.

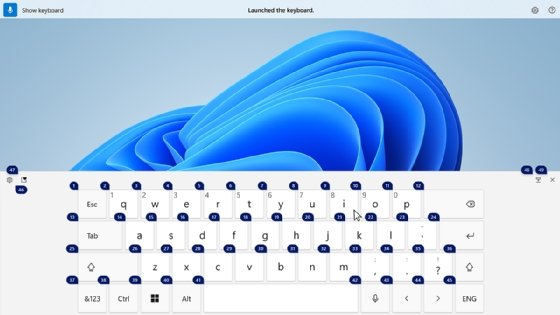
The virtual QWERTY keyboard
In addition to traditional physical QWERTY keyboards, there are also virtual QWERTY keyboards that can be used on touchscreen devices, such as smartphones and tablets.
These keyboards use software to mimic the layout and functionality of a physical keyboard, enabling users to type on a virtual keyboard displayed on screen. Virtual QWERTY keyboards are often used in situations where a physical keyboard is not available or practical, such as when typing on a mobile device or when using voice recognition software.
Overall, the QWERTY keyboard is an integral part of the modern IT landscape. While there may be other keyboard layouts that offer advantages in specific situations, the QWERTY layout is widely recognized and familiar, making it a reliable and effective choice for many users.
See how keyloggers, which monitor and record each keystroke on a specific computer or mobile device, are used as a spyware tool and how to protect from them.
