SCADA (supervisory control and data acquisition)
What is SCADA (supervisory control and data acquisition) and how does it work?
SCADA (supervisory control and data acquisition) is a category of software applications for controlling industrial processes, which is the gathering of data in Real Time from remote locations in order to control equipment and conditions. SCADA provides organizations with the tools needed to make and deploy data-driven decisions regarding their industrial processes.
One of the most commonly used types of industrial control system, SCADA can be used to manage almost any type of industrial process.
SCADA systems include hardware and software components. The hardware gathers and feeds data into field controller systems, which forward the data to other systems that process and present it to a human-machine interface (HMI) in a timely manner. SCADA systems also record and log all events for reporting process status and issues. SCADA applications warn when conditions become hazardous by sounding alarms.
Components of a SCADA system
SCADA systems include components deployed in the field to gather real-time data, as well as related systems to enable data collection and enhance Industrial automation. SCADA components include the following:
- Sensors and actuators. A sensor is a feature of a device or system that detects inputs from industrial processes. An actuator is a feature of the device or system that controls the mechanism of the process. In simple terms, a sensor functions like a gauge or meter, which displays the status of a machine; an actuator acts like a switch, dial or control valve that can be used to control a device. Both sensors and actuators are controlled and monitored by SCADA field controllers.
- SCADA field controllers. These interface directly with sensors and actuators. There are two categories of field controllers:
- Remote telemetry units, also called remote terminal units (RTUs), interface with sensors to collect telemetry data and forward it to a primary system for further action.
- Programmable logic controllers (PLCs) interface with actuators to control industrial processes, usually based on current telemetry collected by RTUs and the standards set for the processes.
- SCADA supervisory computers. These control all SCADA processes and are used to gather data from field devices and to send commands to those devices to control industrial processes.
- HMI software. This provides a system that consolidates and presents data from SCADA field devices and enables operators to understand and, if needed, modify the status of SCADA-controlled processes.
- Communication infrastructure. This enables SCADA supervisory systems to communicate with field devices and field controllers. This infrastructure enables SCADA systems to collect data from field devices and to control those devices.
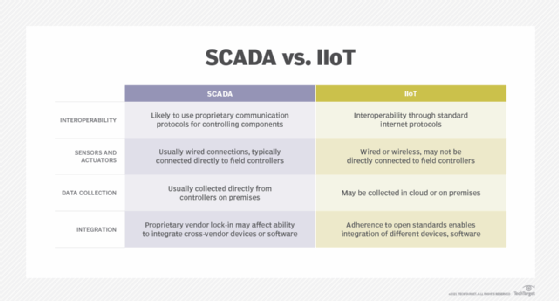
SCADA is sometimes compared with the industrial internet of things (IIoT), and while there is considerable overlap, the two terms are different. SCADA vendors tend to provide more complete, monolithic systems with tight integration across levels and devices, while IIoT vendors are likely to provide greater interoperability and more options for deploying systems and devices across an organization.
Features of SCADA systems
Although SCADA systems may include special features for specific industries or applications, most systems support the following features:
- Data acquisition is a foundation of SCADA systems; sensors collect data and deliver it to field controllers, which, in turn, feed data to the SCADA computers.
- Remote control is achieved through the control of field actuators, based on the data acquired from field sensors.
- Networked data communication enables all SCADA functions. Data collected from sensors must be transmitted to SCADA field controllers, which, in turn, communicate with the SCADA supervisory computers; remote control commands are transmitted back to actuators from the SCADA supervisory computers.
- Data presentation is achieved through HMIs, which represent current and historical data to the operators running the SCADA system.
- Real-time and historical data are both important parts of the SCADA system, as they enable users to track current performance against historical trends.
- Alarms alert SCADA operators to potentially significant conditions in the system. Alerts can be configured to notify operators when processes are blocked, when systems are failing, or when other aspects of SCADA processes need to be stopped, started or adjusted.
- Reporting on SCADA system operations can include reports on system status, process performance and reports customized to specific uses.
SCADA architecture
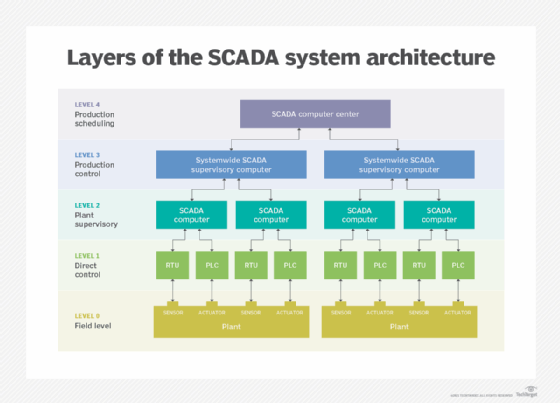
SCADA systems operate at five of the six levels defined in the Purdue Enterprise Reference Architecture for enterprise integration:
- Level 0. The field level includes field devices, such as sensors, used to forward data relating to field processes and actuators used to control processes.
- Level 1. The direct control level includes local controllers, such as PLCs and RTUs, that interface directly with field devices, including accepting data inputs from sensors and sending commands to field device actuators.
- Level 2. The plant supervisory level includes local supervisory systems that aggregate data from level controllers and issue commands for those controllers to carry out.
- Level 3. The production control level includes systemwide supervisory systems that aggregate data from Level 2 systems to produce ongoing reporting to the production scheduling level, as well as other site or regionwide functions, like alerts and reporting.
- Level 4. The production scheduling level includes business systems used to manage ongoing processes.
SCADA use cases and industry examples
SCADA is used to assist in automating and managing industrial processes that have become too complex or cumbersome for human monitoring and control. SCADA is particularly useful for processes that can be monitored and controlled remotely, especially in cases where it is possible to reduce waste and improve efficiency.
Some common industry examples of SCADA industrial automation are the following:
- electricity generation and distribution;
- oil and gas refining operations;
- telecommunications infrastructure;
- transportation and shipping infrastructure;
- fabrication and other industrial processing;
- food and beverage processing;
- chemical manufacturing; and
- utilities infrastructure, including water and waste control.
With SCADA, these processes can be monitored closely and tweaked to improve performance over time.
Evolution of SCADA architecture
The history of SCADA parallels the history of enterprise computing. The earliest SCADA systems were implemented in large industrial enterprises, as they first started to integrate mainframe computing resources with industrial processes.
As computing, networking, and process monitoring and control systems have improved, SCADA evolved through the following four stages:
- First generation: Monolithic systems. SCADA systems implemented in the 1960s and 1970s usually incorporated RTUs at industrial sites connected directly to mainframe or minicomputer systems, usually also on-site or connected over wide area network
- Second generation: Distributed systems. SCADA systems took advantage of wide availability of proprietary local area networks and smaller, more powerful computers during the 1980s to enable greater sharing of operational data at the plant level and beyond. However, the lack of open networking standards prevented interoperability across SCADA product vendors.
- Third generation: Networked systems. SCADA systems depended on greater interoperability provided by industry acceptance and incorporation of standard network protocols during the 1990s. SCADA systems could be scaled more easily, as enterprises were able to integrate systems across their own industrial infrastructure, while using a wider variety of devices and systems.
- Fourth generation: Web- or IIoT-based systems. SCADA systems began appearing in the early 2000s as SCADA vendors embraced web software development tools to enable transparent interoperability and access via universally available interfaces, like web browsers running on handheld devices, laptops and desktop computers.
As cloud computing increasingly dominates the enterprise computing world, it is also changing SCADA systems. SCADA systems can be scaled faster and more easily by allocating cloud computing resources as needed for surges and reducing those resources when demand drops.
Legacy vs. modern SCADA
Organizations still use legacy SCADA computing resources, like mainframes and old proprietary sensors and actuators. These systems may still be functional, in which case organizations can be reluctant to invest in more modern SCADA systems.
Modern SCADA systems that rely on network interoperability, distributed computing and modern communication infrastructures offer better returns on investment of time and resources.
Benefits of modern SCADA
The benefits of updating legacy SCADA systems include the following:
- Scalability. Modern SCADA systems are more scalable than legacy systems for several reasons, including better availability of supported hardware and software and use of cloud computing to meet workload demand.
- Interoperability. Legacy SCADA systems rely on proprietary hardware and software, resulting in vendor lock-in.
- Communications. Modern SCADA systems support more widely supported and modern communications protocols, which enable greater accessibility to SCADA data and controls.
- Support. Legacy SCADA systems may have limited options for support, while modern systems are more likely to be well supported by vendors. Use of commercial off-the-shelf hardware, open networking standards and modern software development platforms makes third-party support more accessible as well.
Improvements to computing are reflected in successive generations of SCADA systems, as well as with security issues in general. Learn how SCADA and IIoT systems can expose the enterprise to security threats and how to defend against them.
