SRAM (static random access memory)
What is SRAM (static random access memory)?
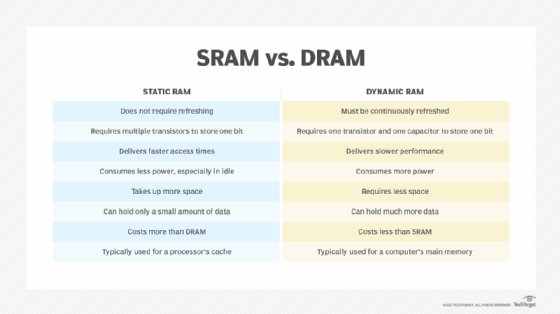
SRAM (static RAM) is a type of random access memory (RAM) that retains data bits in its memory as long as power is being supplied. Unlike dynamic RAM (DRAM), which must be continuously refreshed, SRAM does not have this requirement, resulting in better performance and lower power usage. However, SRAM is also more expensive than DRAM, and it requires a lot more space.
SRAM is commonly used for a computer's cache memory, such as a processor's L2 or L3 cache. It is not used for a computer's main memory because of its cost and size. Most computers use DRAM instead because it supports greater densities at a lower cost per megabyte (MB). However, SRAM is often used for other purposes. For example, it might be part of a RAM digital-to-analog converter (RAMDAC) on a computer's video or graphic card. It might also be used in a disk drive as buffer cache, in a peripheral such as a printer or LCD display, or in a network device such as router or switch.
SRAM can be found in other devices ways as well. For example, SRAM chips are often used in cell phones, wearables and other consumer electronics. They might also be embedded in medical products, which can include anything from hearing aids to body area networks that include multiple devices embedded in the body. In addition, SRAM is used in toys, appliances, automobiles, industrial equipment and a wide range of IoT devices.
Static RAM vs. dynamic RAM
Both SRAM and DRAM are types of volatile memory, which means they lose their data if the power goes out. Despite this similarity, they differ in important ways. Much of this difference lies in how they're constructed. SRAM uses a flip-flop circuit to store each data bit. The circuit delivers two stable states, which are read as 1 or 0. To support these states, the circuit requires six transistors, four to store the bit and two to control access to the cell. Because of all these transistors, a SRAM chip has a much lower capacity that a DRAM chip of comparable size.
DRAM requires only one transistor and one capacitor to store a bit. The capacitor holds the electrons that determine whether the bit is a 0 or 1. The transistor acts as a switch for reading and changing the capacitor's state. Unfortunately, DRAM capacitors have a tendency to leak electrons and lose their charge, so they must be refreshed periodically to retain their data, which can affect access speeds and increase power usage.
Because of the different architectures, SRAM tends to perform better and require less power, especially when it sits idle. However, it cannot store as much data as DRAM, and it is more expensive. The following table outlines several of the key differences between SRAM and DRAM.
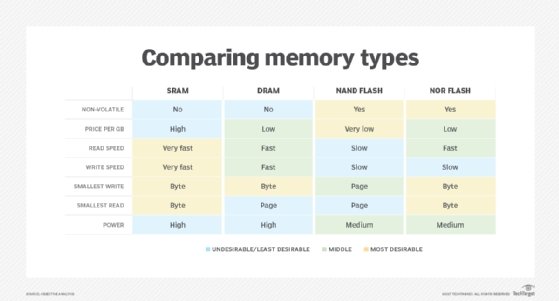
Both SRAM and DRAM easily outperform most of today's nonvolatile memory, even the latest generation of flash drives and storage class memory devices such as Intel Optane. Computer systems are likely to rely on SRAM and DRAM for some time to come, although there is a great deal of research underway looking into alternatives to both memory and storage.
Until then, SRAM and DRAM offer both advantages and disadvantages that make them best suited for specific use cases. This is why DRAM is used for a computer's memory and SRAM is used for its cache, which requires the fastest possible access speeds. In fact, SRAM could potentially benefit any type of device in which performance and power usage are of primary concern.
See also: Cache vs. RAM: Differences between the two memory types and Flash memory vs. RAM: What's the difference?
