Top 10 spyware threats
What are the top 10 spyware threats?
The top 10 spyware list describes the 10 common spyware threats behind famous spyware attacks and is frequently identified by Webroot's Spy Audit, a free spyware scanner tool.
What is spyware?
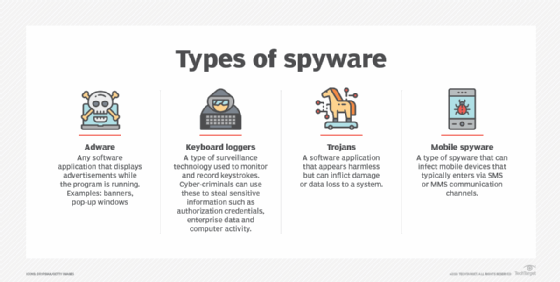
Spyware is a term that refers to malicious software that is purposely designed to access a computer and record its activity. Spyware can track and record a user's browsing habits, login credentials, passwords, etc. The spyware author uses the information obtained in this data breach to engage in fraudulent activity, or sell it to a third party.
Visit our spyware feature page to learn more about this problem and how to beat it.
The top 10 spyware threats
The top spyware threats facing organizations today include:
1. Advanced Keylogger
Advanced Keylogger, a keystroke logger, monitors keystrokes and takes screenshots.
2. CoolWebSearch (CWS)
CoolWebSearch (CWS) is a software suite used to exploit Internet Explorer (IE) vulnerabilities and may hijack a user's web searches, homepage and other IE settings. CWS spyware is known to rewrite search engine results, modify the infected device's host file to redirect DNS lookups and direct traffic to advertisements.
3. FinSpy (aka FinFisher)
FinSpy, or FinFisher, is an advanced suite of surveillance tools sold to law enforcement and intelligence agencies. FinSpy works on Windows, macOS, Linux, Android and iOS operating systems. Its capabilities vary depending on the platform. Law enforcement, intelligence agencies, and threat actors often use FinSpy to secretly turn on microphones to record conversations, switch on cameras, record and transmit images, transmit key logs in real time, modify files and much more.
4. Gator (GAIN)
Gator is a type of adware that may display banner advertisements based on user web surfing habits. Gator is often bundled with numerous free software programs and pirated applications. Gator monitors online user behavior and targets them with personalized ads.
5. GO Keyboard
GO Keyboard is a virtual Android keyboard app that masquerades as a legitimate mobile application. Once installed on an Android device, GO Keyboard transmits personal information to its remote servers without explicit consent from users.
Information shared by GO Keyboard spyware includes:
- Android OS version
- Device model and screen size
- Google account email address
- International Mobile Subscriber Identity (IMSI)
- Location
- Network type
- Preferred language
- Social media interactions
GO Keyboard executes code from a remote server to breach Google Play privacy policies.
6. HawkEye
HawkEye, a keylogger virus, was dormant for years but returned during the early days of the COVID-19 pandemic. Infected machines track key logs and other inputs and share this information with a remote server.
New versions of HawkEye are increasingly difficult to detect due to exceptional anti-detection features. A recent version took the form of a spyware email threat pretending to be an alert from the director-general of the World Health Organization. This social engineering attack encouraged users to download a (malicious) attachment to access information about COVID-19 and the vaccine.
7. HuntBar
HuntBar is a Trojan application that hijacks web browser settings and downloads and installs adware without the user's knowledge. Also known as Adware.Websearch or WinTools, HuntBar tracks browsing behavior, redirects web traffic to affiliate websites, forcefully displays advertisements and installs more spyware programs and toolbars on IE.
8. Look2Me
Look2Me is spyware that tracks user behavior, website logs and social media interactions and shares this information with a remote server. The information is then used to show intrusive advertisements. Look2Me spyware also downloads and installs various add-ons, extensions, toolbars and other unwanted programs on a user's computer. This makes the spyware threat more dangerous than traditional adware. Removing Look2Me is difficult because of its rootkit-type functionality.
9. Pegasus
NSO Group's Pegasus spyware is one of the latest spyware threats making headlines. Although Pegasus was initially developed to fight terrorism, evidence suggests that many clients use Pegasus to spy on journalists, political activists, political opponents and almost anyone the client desires. The governments in France, Hungary, India, Saudi Arabia, United Arab Emirates, the United Kingdom and the United States are known to have used Pegasus spyware.
10. PhoneSpy
PhoneSpy is an example of a spyware virus that pretends to be a mobile application to gain access to and infect Android mobile devices. This approach allows threat actors to remotely control mobile devices and steal data. Mobile applications with PhoneSpy aren't available on Google Play Store, so it's believed to spread through social engineering attacks and third-party platforms.
See also: Top 10 types of information security threats for IT teams, 10 ways to prevent computer security threats from insiders and top 4 mobile security threats and challenges for businesses.
