Unix
What is Unix?
Unix -- trademarked as UNIX -- is a multiuser, multitasking operating system (OS) designed for flexibility and adaptability. Originally developed in the 1970s, Unix was one of the first OSes to be written in the C programming language. Since its introduction, the Unix operating system and its offshoots have had a profound effect on the computer and electronics industry, offering portability, stability and interoperability across a range of heterogeneous environments and device types.
History of Unix
In the late 1960s, Bell Labs (later AT&T), General Electric and the Massachusetts Institute of Technology attempted to develop an interactive time-sharing system called Multiplexed Information and Computing Service (Multics) that would enable multiple users to access a mainframe simultaneously.
Disappointed with the results, Bell Labs pulled out of the project, but Bell computer scientists Ken Thompson and Dennis Ritchie continued their work, which culminated in the development of the Unix OS. As part of this effort, Thompson and Ritchie recruited other Bell Labs researchers, and together, they built a suite of components that provided a foundation for the operating system. The components included a hierarchical file system, a command-line interface (CLI) and multiple small utility programs. The OS also brought with it the concepts of computer processes and device files.
A month later, Thompson deployed a self-hosting operating system with an assembler, editor and shell. The name, pronounced YEW-nihks, was a pun based on the earlier system -- an emasculated or eunuch version of Multics. Unix was much smaller than what the original developers intended for Multics, and it was a single-tasking system. Multitasking capabilities would come later.
Prior to 1973, Unix was written in assembler language, but the fourth edition was rewritten in C. This was revolutionary at the time because OSes were thought to be too complex and sophisticated to be written in C, a high-level language. This increased Unix's portability across multiple computing platforms.
In the late 1970s and early '80s, Unix amassed a strong following in academia, which led commercial startups, such as Solaris Technologies and Sequent, to adopt it on a larger scale. Between 1977 and 1995, the Computer Systems Research Group at the University of California, Berkeley developed Berkeley Software Distribution (BSD), one of the earliest Unix distributions and the foundation for several other Unix spinoffs.
In 1991, Linus Torvalds, a student at the University of Helsinki, created a Unix-based OS for his PC. He would later call his project Linux and make it available as a free download, which led to the growing popularity of Unix-like systems. Today, a variety of modern servers, workstations, mobile devices and embedded systems are driven by Unix-based OSes, including macOS computers and Android mobile devices.
What is Unix used for?
Unix is a modular OS made up of a number of essential components, including the kernel, shell, file system and a core set of utilities or programs.
At the heart of the Unix OS is the kernel, a master control program that provides services to start and end programs. It also handles low-level operations, such as allocating memory, managing files, responding to system calls and scheduling tasks. Task scheduling is necessary to avoid conflicts when multiple programs attempt to access the same resource at the same time.
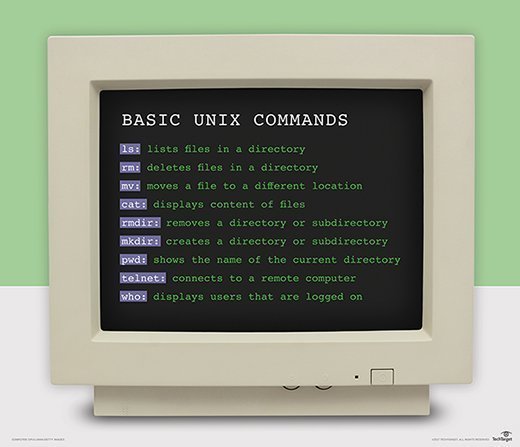
Users interact with the Unix environment through the shell, a CLI for entering commands that are passed to the kernel for execution. A command is used to invoke one of the available utilities. Each utility carries out a specific operation, such as creating files, deleting directories, retrieving system information or configuring the user environment.
Some Unix commands take one or more arguments, which provide a way to refine the utility's behavior. For example, a user might enter the command rm OldFIle.txt. The command is calling the rm utility, which deletes files in a directory. The command also includes the argument OldFIle.txt, which is the file to be deleted. When the user enters this command in the shell, the kernel runs the rm program and deletes the specified file.
Unix supports multiple shells, including sh, csh, ksh, tcsh and bash. A Unix distribution typically designates a default shell, but users can choose from any of the supported shells. Users can also customize the shell environment, or they can write their own shell scripts.
In addition, the Unix shell supports the use of pipes (|), a powerful tool for linking multiple commands to create complex workflows. When two or more commands are piped together, the output from the first command is used as input for the second command, the output from the second command is used as input for the third command and so on.
Another important Unix feature is the file system, which provides a hierarchical structure for working with files. The file system organizes directories into an inverted tree with the root directory at the top. Files are then assigned to specific directories and accessed through the directory structure. Previous operating systems divided a storage device into sections by a fixed number of levels.
Unix treats all types of files as simple byte arrays, resulting in a much simpler file model than those in other operating systems. Unix also treats devices and certain kinds of interprocess communication as files.
Unix concepts have been influential for a variety of reasons, including the following:
- Unix was a driving force behind the development of the internet and the transformation of computing into a network-centric paradigm.
- Unix developers are credited for bringing modularity and reusability into the practice of software engineering and inciting a software tools movement.
- Unix developers also created a set of cultural rules for software development -- referred to as the Unix philosophy -- that has been highly influential to the IT community.
Types of Unix
Unix became the first OS that could be improved or enhanced by anyone, partly because it was written in the C language and embraced many popular ideas. However, its early success led to multiple variants that lacked compatibility and interoperability. To address these issues, a number of vendors and individuals came together in the 1980s to standardize the OS, first by creating the Portable Operating System Interface standard and then by defining the Single UNIX Specification (SUS).
Since then, Unix has continued to evolve, with new variants being added, some proprietary and some open source. Much of the progress has been the result of companies, universities and individuals contributing extensions and new ideas.
Unix licensing depends on the specific variant. Some Unix variants are propriety and come with a licensing fee, such as IBM Advanced Interactive eXecutive (AIX) or Oracle Solaris, and other variants are free and open source, including Linux, FreeBSD and OpenBSD. The UNIX trademark is now owned by The Open Group, an industry standards organization that certifies and brands Unix implementations.
Unix-like operating systems
The term Unix-like is often used to describe the different Unix variants, but there is no clear definition of what this term means. In general, it can refer to any OS that has some relation to Unix, no matter how distant, including free and open source variations. Some software developers assert that there are three types of Unix-like systems:
- OSes historically connected to the original codebase from Bell Labs, such as the BSD systems developed by researchers at Berkeley.
- Trademarked and branded Unix-like systems that meet SUS, such as HP-UX and IBM AIX. The Open Group has determined that these systems are allowed to use the Unix name.
- Functional Unix-like systems, such as Linux and Minix, that behave in a manner consistent with the Unix specification. For example, they must have a program that manages the login and command-line sessions.
What is the future of Unix?
Unix and its variants continue to run on a wide range of systems, including workstations, servers and supercomputers. Linux, in particular, has taken the lead in Unix-like implementations, gaining a strong presence in data centers and on cloud platforms. In addition, the OS now runs on all of the world's top 500 supercomputers. Linux is available as both free software and commercial, proprietary software.
Although Linux remains strong, particularly for enterprise servers, Unix itself has seen a decline in usage, in part because of the migration from reduced instruction set computer platforms to x86-based alternatives, which can run more workloads and deliver higher performance at a lower cost.
Experts predict that many organizations will continue to use Unix for mission-critical workloads but will decrease their dependency on the system due to IT modernization and consolidation strategies. However, Unix is still the preferred system for many use cases, such as data center application support, cloud security and vertical-specific software.
Future Unix server sales are expected to drop, but applications in financial, government and telecommunications should continue to drive Unix use. Eventually, Unix might be abandoned completely, but it will likely be a long, slow decline before that happens.
Linux, which evolved from Unix, can be tricky to learn. To help you better understand what Linux can do, it's important to examine the different Linux operating system components.






