
unified communications and collaboration (UCC)
What is unified communications and collaboration (UCC)?
Unified communications and collaboration (UCC) is the collection of technology and software that combines enterprise communication with real-time and asynchronous cooperation capabilities. UCC takes the various methods used in individual unified communications (UC) and collaboration services and makes them available through a single interface to improve connectivity and productivity.
Components of UCC include email, voicemail, calendars, scheduling tools, video conferencing, instant messaging (IM), desktop sharing and VoIP. Additionally, functionality may include presence tracking, which is the ability to tell whether a contact is busy or free, and unified messaging, which is the ability to retrieve all messages from a central location.
Organizations should implement UCC technology to streamline employee and customer interaction methods. Tasks such as brainstorming, virtual meetings and peer feedback can be smoothed by implementing UCC tools. Businesses can also take better advantage of hiring remote or globally dispersed employees with easily accessible communications services that bridge geographical gaps.
Popular vendors with UCC products include Google, Microsoft, and Cisco.
Benefits of UCC
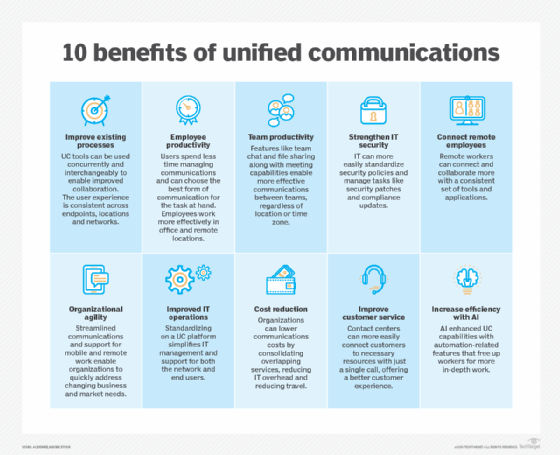
The combination of communications and collaboration tools into a simple interface provides organizations with numerous benefits, including:
- Higher accessibility and productivity as employees with various devices from various locations can work together in a unified environment.
- Faster and more responsive service through real-time notifications and messaging.
- Reduced cost with less telecom, travel and IT expenditure needs.
- Improved customer satisfaction and user experience.
- Easier to facilitate teamwork.
Challenges of UCC
However, UCC poses a number of challenges to networks with old infrastructure, having changed the nature of enterprise network workloads. In a network with compute and storage separate, these dynamic workloads can result in latency and congestion. As UCC and other dynamic workloads have increased, they have driven the adoption of hyper-converged networks to deal with the attendant challenges.
This article is part of
Ultimate guide on enterprise unified communications strategy
Use Cases
Enterprise: While all aspects of business revolve around proper communication and collaboration, UCC tools are especially helpful with product development. Having more streamlined communication channels can also reduce time wasted when waiting for a response and improve operational efficiency.
Education: UCC tools can enhance learning experiences for students by enabling live teaching sessions, video conference review sessions and real-time file sharing.
Healthcare: Healthcare providers could take advantage of UCC services to provide telehealth services, share patient information and consult with additional medical personnel before diagnosis. Tools could also be used to simplify scheduling.






