UDDI (Universal Description, Discovery and Integration)
What is UDDI (Universal Description, Discovery and Integration)?
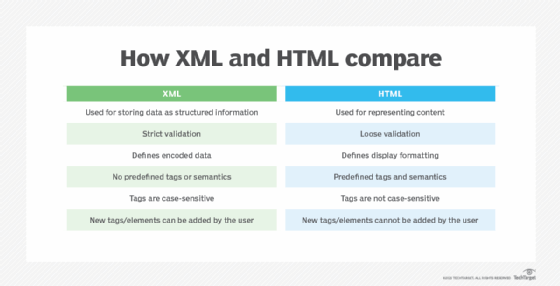
UDDI, or Universal Description, Discovery and Integration, is an Extensible Language Markup (XML)-based standard to describe, publish and find information about web services. It is also a registry for businesses providing web-based services to list themselves and find partners on the Internet.
The UDDI standard includes a set of specifications that define a distributed registry service for web services. It is an XML-based and platform-independent framework that uses Web Service Definition Language (WSDL) to describe interfaces to web services. It is also an open, industry-wide framework since it lets all kinds of businesses list themselves on the Internet and discover, interact with and carry out transactions with each other.
UDDI is often compared to a traditional telephone book's white, yellow and green pages, which correspond to UDDI's categories of Organizations, Categories and Bindings respectively. The project lets businesses list themselves by name, product, location or web services offered. The ultimate goal of UDDI is to streamline online transactions by helping companies find one another on the Web and make their systems interoperable for e-commerce.
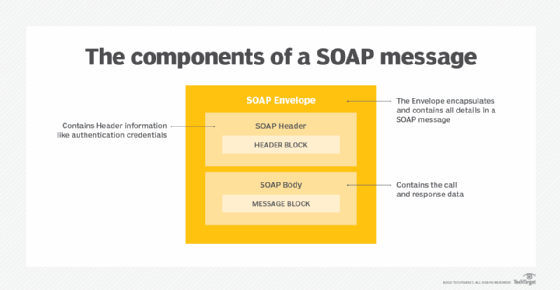
The UDDI specification utilizes World Wide Web Consortium and Internet Engineering Task Force standards such as XML, Hypertext Transfer Protocol, and Domain Name System protocols. It has also adopted early versions of the proposed Simple Object Access Protocol (SOAP) messaging guidelines for cross-platform programming. UDDI can also communicate via Common Object Request Broker Architecture and Java Remote Method Invocation Protocol.
What are the functions of UDDI?
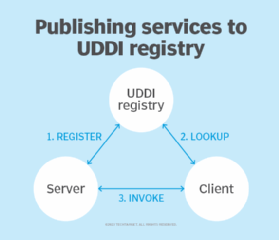
The two main functions of UDDI are to provide a SOAP-based protocol and a set of registries. The registries are globally replicated, and the protocol defines how clients communicate with these registries. A UDDI registry contains the metadata of web services and includes a pointer to the WSDL description of a service. UDDI also includes a set of WSDL port type definitions to manipulate and search the registry.
UDDI's XML schema for SOAP messages defines documents that describe a business and provide information about its services. The schema also includes a common set of APIs (Application Program Interfaces) for querying and publishing information to UDDI directories, plus an API to replicate directory entries between peer UDDI nodes.
What are UDDI registries?
UDDI relies on a distributed registry of businesses plus their service descriptions, implemented in a common XML format, to manage and enable the discovery of web services. Web service providers advertise their services on the UDDI registry that manages all the information about the provider, service implementations and service metadata. Organizing and cataloging web services on a registry allows for sharing and reuse within an enterprise or with an external partner. Today, these registries are based on the UDDI 3.0 specification.
A UDDI registry is a central repository for three primary nodes labeled Providers, Services, and Bindings. Two types of registries are available: private and public. A private registry lets businesses publish and test their internal web applications in a secure, private environment. A public registry consists of peer directories containing information about businesses and their web services. Both private and public registries comply with the same specifications.
UDDI registry directory structure
UDDI has a very specific directory structure and three types of directory listings:
- Organizations (also known as Providers)
- Services
- Bindings (also known as end points)
The Providers folder is where all the service providers are listed in the UDDI server. It includes a Relationships tab to specify organizational structures (parent-child) and partnerships (peer), which describe a company's operational structure and convey business relationships.
The Services, which are logical containers, are below the service providers, and the Bindings for the services are below the services. Services includes a collection of Bindings and Categories. The Bindings listing refers to endpoints or physical locations where the services exist. They are the services' own children. A single service, in turn, is a child of an organization (provider).
Categories are listed at every level in the hierarchy (meaning each level has a Categories tab), and that helps to make UDDI a powerful and expressive standard. A category classifies the different levels through metadata. When a user adds a category to a level of the UDDI structure (providers, services, bindings), they can either use a standard category or create a custom category.
Bindings are the lowest level in the UDDI hierarchy. They represent implementation locations or service details, like WSDLs. In a binding for a service, the access point could be a URL to where the service exists. A WSDL deployment is another possible access point. Regardless of the access point, it's usually better to expose the service and/or its WSDL for simplicity instead of putting all the details of the service, such as its parameters and other technical information, in the UDDI registry.
What is the history of UDDI?
Thirty-six companies announced UDDI 1.0 in September 2000. Microsoft, IBM, Ariba, Dell, Merrill Lynch, Sun Microsystems, and SAP were some of the companies that spearheaded the project. In the years since the original announcement, the UDDI project has grown into an industry-wide initiative sponsored by the Organization for the Advancement of Structured Information Standards (OASIS). It now includes hundreds of companies, including some of the biggest names in the corporate world.
In November 2000, UDDI entered its public beta-testing phase. Each of its three founders -- Microsoft, IBM, and Ariba -- set up registry servers that were interoperable with servers from other members. As information goes into a registry server, it is shared by servers in other businesses. A UDDI server is a directory of available service providers and their services.
The Microsoft UDDI server was originally part of the Windows Server platform. It later became part of BizTalk Server. IBM maintains two public registries. Its test registry lets businesses test and validate their web services and experience the UDDI registration process without placing the service in an official registry.
In 2001, Microsoft and IBM made the UDDI registry live and launched the first UDDI operator sites. UDDI v2 was also launched. In 2005, UDDI v3 became an OASIS Standard 3. As of 2022, OASIS Open sponsors work on the OASIS UDDI Specification TC to improve the foundation of the web services registry developed and published by UDDI.org.
