Unified Extensible Firmware Interface (UEFI)
What is Unified Extensible Firmware Interface (UEFI)?
Unified Extensible Firmware Interface (UEFI) is a specification for a software program that connects a computer's firmware to its operating system (OS). UEFI is expected to eventually replace basic input/output system (BIOS) but is compatible with it. The specification is most often pronounced by naming the letters U-E-F-I.
UEFI functions via special firmware installed on a computer's motherboard. Like BIOS, UEFI is installed at the time of manufacturing and is the first program that runs when booting a computer. It checks to see which hardware components are attached, wakes up the components and hands them over to the OS. The new specification addresses several limitations of BIOS, including restrictions on hard disk partition size and the amount of time BIOS takes to perform its tasks.
Most modern computer systems are equipped to support traditional BIOS, as well as UEFI, although Intel Corp. has stated its intention to phase out BIOS support in newer personal computers (PCs).
What does UEFI do?
UEFI defines a new method by which OSes and platform firmware communicate, providing a lightweight BIOS alternative that uses only the information needed to launch the OS boot process. In addition, UEFI provides enhanced computer security features and supports most existing BIOS systems with backward compatibility.
UEFI contains platform-related data tables and boot and runtime service calls used by the OS loader. Taken together, this information defines the required interfaces and structures that must be implemented for firmware and hardware devices to support UEFI. UEFI is programmable, enabling original equipment manufacturer developers to add applications and drivers and UEFI to function as a lightweight OS.
In general, BIOS is considered a vestige from earlier computing, whereas UEFI is regarded as the wave of the future. However, for ease of understanding, some information technology users refer to the processes collectively as UEFI BIOS, despite their substantial differences.
UEFI's evolution from EFI
BIOS has been in use since the advent of disk OS computers in the mid-1970s. In 1981, IBM was the first vendor to incorporate BIOS in PCs, a move that prompted broad industry adoption. The emergence of UEFI parallels the increased drive densities used for modern application workloads.
Intel developed the Extensible Firmware Interface (EFI) as an outgrowth of its 64-bit Itanium server architecture in the 1990s, a technology codeveloped with computer maker Hewlett Packard (HP). The industry perceived EFI as a way to address the memory and processing limitations of BIOS in X86 server architectures. Those limitations included 16-bit computing mode, bounded system memory and tedious assembly language programming.
EFI, subsequently renamed Intel Boot Initiative, technically remains the property of Intel, although the vendor ceased sole development of the specification following the release of EFI version 1.10 in 2005. (By then, Intel had also phased out its Itanium processor line, following product delays and other hiccups.) Intel contributed EFI 1.10 to the UEFI Forum, an alliance of chipset, hardware, system, firmware and OS vendors.
The industry consortium manages the development of UEFI specification standards. The latest standard, UEFI 2.9, was made publicly available in March 2021.
Booting up: BIOS vs. UEFI
Turning on a computer kick-starts a chain of events that occurs before the OS is loaded. Firmware rouses the computer's subsystem to execute a series of tests and locates the boot loader, which, in turn, starts the OS kernel.
BIOS and UEFI both use low-level software to manage startup functions prior to booting an OS, albeit using different techniques.
BIOS resides on a chip on the machine's motherboard and initializes the central processing unit, random access memory, Peripheral Component Interconnect Express cards and network devices. BIOS runs a power-on self-test (POST) diagnostic sequence. POST ensures that hardware is configured properly and all components are functioning as intended.
BIOS runs only in 16-bit processor mode, which limits the number of software commands the firmware is able to execute at any one time. BIOS allots 1 megabyte of memory in which tasks can be executed. Interfaces and devices thus are initialized sequentially, which can contribute to a sluggish startup.
To accomplish its task, BIOS consults the Master Boot Record (MBR) to locate the OS and launch the boot loader. MBR uses 32-bit values to describe the offset and length of a partition, thus limiting BIOS systems to 2 terabyte (TB) drives and no more than four partitions.
UEFI behaves like a like a miniaturized OS that sits between firmware and the OS. It performs the same diagnostics as BIOS at startup but offers more flexibility. The OS boots directly in UEFI. This eliminates the need to repeatedly press toggle keys, as is required to boot BIOS.
UEFI stores initialization data in an EFI file partition in nonvolatile flash memory, rather than in the firmware. UEFI also can load during boot from a drive or a network share. UEFI also deploys a more flexible partitioning scheme than MBR, known as a Globally Unique Identifier Partition Table, or GPT. GPT was also created by Intel as part of EFI. GPT uses 64-bit values to enable the creation of up to 128 partitions and is required for systems launched from 2 TB drives and larger. The EFI partition uses the file allocation table, including FAT16, FAT32 or virtual FAT.
Most new desktop PCs, laptops and some tablets bundle UEFI firmware that runs in compatibility support mode for older 32-bit Windows. Computer manufacturers are expected to support BIOS in the near term, but the transition to UEFI is well underway. In 2013, custody of the Advanced Configuration and Power Interface (ACPI) was transferred to UEFI Forum.
Originally developed collaboratively by HP, Intel, Microsoft, Phoenix Technologies and Toshiba, ACPI is an open standard for BIOS that governs how much power is delivered to each peripheral device.
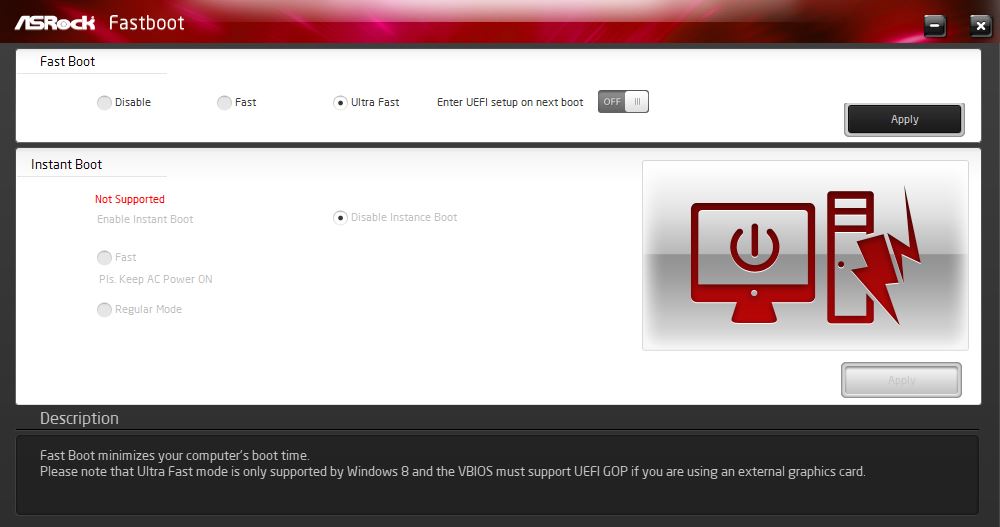 Motherboard- or system-specific utilities for accessing UEFI/BIOS differ from vendor to vendor and how they appear but vary little in terms of functionality.
Motherboard- or system-specific utilities for accessing UEFI/BIOS differ from vendor to vendor and how they appear but vary little in terms of functionality.
Advantages of UEFI
UEFI provides many significant enhancements over BIOS, including the following:
- Boot mode. Microsoft Windows users can run 32-bit UEFI or 64-bit UEFI, although experts recommend that the OS bit mode and the firmware bit mode should be the same to avoid communication issues during runtime.
- Drives. According to UEFI Forum, UEFI supports boot drives of 2.2 TB and higher capacities, including drives with theoretical capacity of 9.4 zettabytes. That far exceeds the maximum drive capacities currently available.
- Drivers. UEFI supports discrete drivers, whereas BIOS drive support is stored in read-only memory, which necessitates tuning it for compatibility when drives are swapped out or changes are made.
- Graphical user interface (GUI). UEFI enables new modules to be added to the GUI more easily, including device drivers for motherboard hardware and attached peripheral devices.
- Multiple OS support. Whereas BIOS allows a single boot loader, UEFI lets users install loaders for Debian-based Ubuntu and other Linux variants, along with Windows OS loaders, in the same EFI system partition.
- Programming. UEFI firmware is written predominantly in C language, which enables users to add or remove functions with less programming than BIOS, which is written in an assembler language, sometimes in combination with C.
- Security. Secure Boot is a UEFI protocol for Windows 8 or later Windows versions. Secure Boot makes a system's firmware the root of trust to verify device and system integrity. The goal is to prevent hackers from installing rootkits in the time between bootup and handoff to the OS. Secure Boot also enables an authorized user to configure networks and troubleshoot issues remotely, something a BIOS administrator must be physically present to do.
As computer makers gradually move away from BIOS, they typically integrate UEFI firmware that runs with Compatibility Support Module (CSM) in modern devices. Although not intended as a long-term solution, CSM enables UEFI-based machines to launch in legacy BIOS mode to work with older Windows versions and other OSes. However, users may find it preferable to upgrade to the latest version of the OS to realize the value of UEFI.
UEFI disadvantages, or when to boot from BIOS
Software is always a target for threat actors, and UEFI is no exception. One such attack, dubbed TrickBot, surfaced in December 2020. TrickBot malware works by attempting to spy on device firmware, which could permit malicious actors to subvert the boot process and gain access to the OS.
The TrickBot episode came on the heels of 2018 findings by ESET Research, a Slovak outlet for the information security community, which claimed to have discovered a rootkit in the wild that potentially enabled hackers to surveil UEFI firmware and install malicious code.
Aside from security issues, organizations switching to UEFI may incur a cost related to booting from flash. While this is faster than booting from hard disk drives, older systems may require a retrofit, namely a larger flash die on the motherboard.
Another potential drawback is UEFI's reliance on the FAT file format, which is maintained by the OS. Larger drive partitions can add too much system overhead, thus defeating some of the performance advantages. This is an example in which BIOS can be a more useful option, especially for a computer running an older OS version and smaller boot disks.
UEFI accessibility
Users can download the UEFI specification from the UEFI Forum website. The most recent version, UEFI 2.9, features several enhancements, including the following:
- supports devices based on the new Compute Express Link interconnect;
- supports publishing Linux Device Tree Blob binary format files that identify computer components in the UEFI configuration table; and
- clarifies how UEFI-based update runtime calls are made on certain Advanced Reduced Instruction Set Computing Machine server
To determine whether a computer boots from BIOS or UEFI, press the Windows and R keys on the keyboard to launch the Run configuration box. Type MSInfo32 in the dialog box, and hit the Enter key. A system summary screen appears. Look for the entry entitled BIOS Mode, and make note of the corresponding value. If the value says Legacy, the system has BIOS. Otherwise, UEFI will appear in the value field.
Windows users can access UEFI via the PC Settings option in the search bar. The path is PC Settings > Update & Security > Recovery > Advanced Startup, and select the Restart Now option. From the menu, select Troubleshoot > Advanced Options > UEFI Firmware Settings, and restart again.
Linux machines with UEFI installed will show it in the sys/firmware/efi directory. This will also be reflected in the Linux Grand Unified Bootloader boot manager as grub-efi, rather than grub-pc for BIOS.
Coreboot and UEFI
With the industry gradually phasing BIOS out, UEFI receives most of the attention as the heir apparent. However, open source Coreboot is another option vying to replace legacy BIOS, and its proponents claim it is faster than UEFI. Coreboot, formerly known as LinuxBIOS, is purportedly able to replace proprietary BIOS and UEFI firmware -- with underlying benefits of extreme performance, minimal resources to boot machines and security measures that include a minimal trusted computing base and virtual boot disk.
Coreboot code was first introduced in 1999, and the community-based development project's supporters include Google, whose Chromebook devices replaced BIOS with Coreboot since the first generation. Coreboot's market penetration has been slow, however, due to the work it entails on the part of manufacturers. Since Coreboot initializes only Bare metal, device makers need to make the effort to port the code for integration in chips and motherboards.
