W3C (World Wide Web Consortium)
What is W3C (World Wide Web Consortium)?
The W3C (World Wide Web Consortium) is an international organization that creates standards for the World Wide Web. The WC3 is committed to improving the web by setting and promoting web-based standards.
The W3C's goal is to create technical standards and guidelines for web technologies worldwide. These standards are intended to keep a consistent level of technical quality and compatibility concerning the World Wide Web. Developers who create web applications can have confidence in the tools they're using, as web applications using these standards have been vetted by experts. An example of a W3C standard is web browsers. Most use W3C standards, which enables them to interpret code such as Hypertext Markup Language (HTML) and Cascading Style Sheets (CSS).
What is the organizational structure of the W3C?
Founded in 1994 by World Wide Web inventor Tim Berners-Lee, the W3C is made up of several hundred member organizations from different IT industries. Berners-Lee currently serves as the director, and Dr. Jeff Jaffe is CEO. From an administrative sense, W3C is structured as a joint agreement among four host institutions: Massachusetts Institute of Technology (MIT), European Research Consortium for Infomatics and Mathematics (ERCIM), Keio University in Tokyo and Beihang University in China.
Although the WC3 doesn't have a traditional organizational structure or a single physical headquarters, it's led by a director and CEO, with a management team responsible for resource allocation and strategic planning. From a process sense, in addition to the director and CEO, the WC3 comprises an Advisory Committee, Advisory Board, a Technical Architecture Group and chartered groups. The function of these team members is as follows:
- The director and CEO assess the consensus for W3C-wide decisions.
- The Advisory Committee is made up of a representative from each W3C member. They review the roles in W3C processes and elect the Advisory Board and Technical Architecture Groups.
- The Advisory Board acts as a consultative body.
- The Technical Architecture Group documents new principles for web architectures.
- Chartered groups are made up of members and invited experts, producing most of W3C's deliverables.
W3C membership is open to all for-profit and not-for-profit organizations -- including commercial, educational and government -- and individuals. Many of the member organizations that are part of W3C Community Groups and Business Groups are doing web development for products, conducting research on the web or developing specifications based on W3C work. According to the W3C website, there are currently 462 members in these working groups.
Although W3C is partially funded by industrial members, it's vendor-neutral, and its products are freely available. In addition to member funding, W3C generates revenue through research grants and other sponsorships and donations. In June 2022, the W3C filed for 501(c)(3) nonprofit status and will be electing a Board of Directors.
Purpose of the W3C
W3C is designed to bring interested parties together from different areas of IT to work on developing web standards. The W3C also focuses on developing protocols and guidelines that help ensure the growth and longevity of the web. Developing new standards is a consensus-based process by different teams in the W3C, as these standards are intended to help ensure quality for web-based developers and end users. This helps ensure web applications built with these standards will work with all others and anyone can access them.
W3C standards
W3C standards describe a range of recommended programming languages to generally accepted principles in web services and open architectures. Web design and application standards include, but are not limited to, the following:
- Common Gateway Interface (CGI)
- CSS
- Document Object Model (DOM)
- Extensible HTML (XHTML)
- Extensible Markup Language (XML)
- Gleaning Resource Descriptions from Dialects of Languages (GRDDL)
- HTML
- JavaScript Object Notation for Linked Data (JSON-LD)
- Resource Description Framework (RDF)
- Simple Object Access Protocol (SOAP)
- SPARQL Protocol and RDF Query Language (SPARQL)
- Speech Recognition Grammar Specification (SRGS)
- Speech Synthesis Markup Language (SSML)
- Scalable Vector Graphics (SVG)
- VoiceXML (VXML)
- Web Real-Time Communications (WebRTC)
- Web Services Description Language (WSDL)
Though it's a good practice to follow these standards, the W3C standards aren't enforced formally, and there's no penalty for ignoring them.
History of W3C
The W3C was founded at the MIT Laboratory for Computer Science in collaboration with the European Organization for Nuclear Research, Defense Advanced Research Projects Agency and European Commission.
In 1995, the French Institute for Research in Computer Science and Automation (Inria) became a W3C host, followed by Keio University in Japan in 1996. In 1997, W3C began creating regional offices around the world.
In December 1996, the W3C added both CSS and HTML as a standard. In 1998, the W3C added XML as an approved standard.
In 2003, ERCIM became the European host of the W3C, taking the role from Inria. By 2009, the number of W3C world offices expanded to 18, creating worldwide standards across countries, including Australia, Brazil, China, Germany, India and Sweden. In 2020, the W3C Offices Program evolved into the W3C Chapters Program.
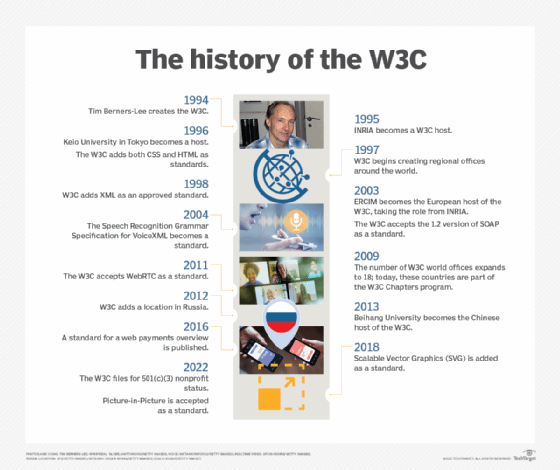
Also in 2003, the W3C accepted the 1.2 version of SOAP as a standard. In 2004, the W3C recommendation for SRGS VXML was accepted.
By 2009, the U.K. and Ireland offices were added. In 2011, the W3C accepted WebRTC as a standard.
In 2012, W3C added a location in Russia and organized a community of major web players and publishers to create a MediaWiki. The MediaWiki's goal was to document open web standards.
In 2013, Beihang University became the Chinese host of the W3C. In 2016, a standard for a web payments overview was published.
In 2018, SVG was added as a standard. Picture-in-Picture became a standard in 2022.
Learn more about W3C and how it relates to software accessibility standards, as well as what the W3C's four principles of software accessibility are.
