What is Wi-Fi calling?
Wi-Fi calling is a voice service that lets users place and receive calls over a wireless internet connection, as opposed to using a cellular signal. Smartphone users can make use of Wi-Fi calling to talk and text on their smartphones from locations where it's difficult to reach a strong cellular phone signal. Typically, the term refers to cellular calls, as opposed to texting.
What is the purpose of Wi-Fi calling?
Most users are familiar with the process of using Wi-Fi to send messages via Short Message Service, or SMS. Wi-Fi calling is the ability of a Wi-Fi network to facilitate voice or video calls. By default, Wi-Fi calling connects users to a Wi-Fi network so they don't have to use mobile data to place these calls. The service can be used domestically and internationally from most countries.
Wi-Fi calling is available on most Android and iOS devices, and the user experience is like any other phone call. However, the experience and call quality may be affected by the number of people using a Wi-Fi hotspot or if the network connection is faulty and prone to call disruptions.
How does Wi-Fi calling work?
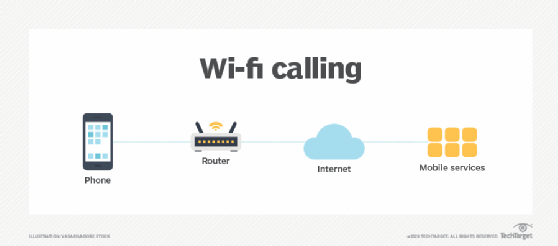
Wi-Fi calling works similarly to other Wi-Fi-enabled voice over Internet Protocol (VoIP) applications, such as Skype or WhatsApp, albeit with slight differences. Wi-Fi calling works through transmitting the same cellular data packets as Wi-Fi VoIP through a Wi-Fi connection and across the internet. From the internet, data is passed to the cellular network and then back to the answering party. Wi-Fi calling must be supported by the user's smartphone to work. The service is a newer version of the Generic Access Network protocol -- a protocol for telecommunications systems that bridges wireless technology and IP networking, enabling cellphone users to access voice, data and multimedia services from any IP network globally. A VoIP system provides one of the easiest ways to make Wi-Fi calls.
Calls and messages appear in normal call and chat logs, and an icon may appear in the phone's notification bar -- normally saying VoLTE, meaning voice over Long-Term Evolution, or with an icon of a phone receiver with a Wi-Fi symbol. Users can also turn their phone on airplane mode to ensure that their call uses Wi-Fi calling.
Wi-Fi calling user considerations
To use Wi-Fi calling, users should first ensure that both their carrier and smartphone support this capability. Most providers have enabled the smartphone feature to avoid losing customers to software apps. If a user's device supports Wi-Fi calling, they can expect to save money on cellphone calls -- particularly international calls -- while also experiencing better call quality.
The requirements for Wi-Fi calling may differ by carrier. For example, a carrier may require the user to enable the high-definition voice setting on their device. Once enabled, the Wi-Fi calling feature is used automatically when the device is connected to Wi-Fi. Depending on the carrier, network or device, a call may drop if it leaves a Wi-Fi router's range.
Wi-Fi calling via apps or websites
Wi-Fi calling may also refer to the use of computers and mobile devices for audio communication across Wi-Fi to telephone numbers through a specialized app or web service. This type of Wi-Fi calling enables users to avoid paying for phone service.
Some apps enable the use of a real number for both inbound and outbound calls for free. For example, WhatsApp enables users to make and receive both voice and video calls from their WhatsApp number to another WhatsApp number using the phone's internet connection rather than its mobile plan minutes. The caller and recipient may be in any country where WhatsApp is available -- if they both use the application for the purpose of calling.
The WhatsApp desktop app also enables Wi-Fi calling, as long as the following are true:
- The caller's phone and desktop have an active internet connection.
- The caller allows WhatsApp to access their computer's microphone.
- The caller has connected an audio output device and microphone to their computer for making calls.
Advantages of Wi-Fi calling
Wi-Fi calling offers a number of advantages:
- It helps users connect to a phone call or messaging in areas where cellular service is weak.
- Phone calls can be made using the individual's phone number -- no additional number is needed.
- It is easy to set up.
- Once enabled, it works automatically.
- It can save minutes on cellular subscriptions or avoid the requirement for the contract altogether, given the availability of a nearby active Wi-Fi network.
- Benefiting from the higher bandwidth of Wi-Fi, Wi-Fi calling can also handle texts and multimedia messaging.
- The service is free in most instances.
How much does Wi-Fi calling cost?
Pricing of Wi-Fi calling varies depending on the carrier.
For example, with Verizon, Wi-Fi calling and texting to and from U.S. numbers is free. However, calls and texts to non-U.S. numbers are chargeable as per the user's international long-distance calling plan or per Verizon's pay-as-you-go rates. When a U.S. user is outside the U.S., they can still make Wi-Fi calls to the U.S. for free. However, they are charged for calls to any other country, Regardless of the call type or user/recipient location, the Wi-Fi calling feature is built into most current Verizon smartphones. And the calls are made/received over an available Wi-Fi network instead of a cellular network.
Like Verizon, Wi-Fi calling within the U.S. is free with AT&T. Rates do apply for premium and international numbers. When a U.S. user is outside the U.S., they can make Wi-Fi calls to U.S. numbers for free. However, international calls are billed based on the user's international roaming package.
It is important to note that Wi-Fi access points that require an access fee incur an additional charge -- even when the provider doesn't charge for Wi-Fi calls.
Which devices support Wi-Fi calling?
Different carriers have different policies for Wi-Fi calling and may support Wi-Fi calling on certain devices and not others. Even if an individual has a smartphone capable of Wi-Fi calling, it may not be able to be turned on if the carrier network doesn't support the device. However, many of the major carriers support Wi-Fi calling.
Both Android and iOS devices feature Wi-Fi calling. IPhones began supporting Wi-Fi calling with iPhone 5c, and most Android devices support Wi-Fi calling.
How to enable Wi-Fi calling
Enabling and disabling Wi-Fi calling differ depending on the device.
Here is the general procedure to enable Wi-Fi calling.
Android devices
- Pull down the notification shade, and select the device settings.
- Search for Wi-Fi calling in the search bar.
- The setting may also appear under the advanced section of Wi-Fi settings.
- Tap the Wi-Fi calling option, and slide the toggle to turn it on.
IOS devices
- Select the Settings app > Phone > Wi-Fi calling.
- Select the slider to turn Wi-Fi calling on.
Both iOS and Android devices require a user to input their address in the event of an emergency for emergency calls.
Here is the general procedure to disable Wi-Fi calling.
Android devices
- Select Setting > Advanced Calling > Wi-Fi Calling.
- Set the On/Off setting to Off.
IOS devices
- Go to Settings > Cellular > Wi-Fi Calling.
- Switch "Wi-Fi Calling on This iPhone" to off.
Wi-Fi is one part of the full wireless infrastructure picture. Learn everything you need to know about wireless communications in our guide. Also, see what IT must do when remote users are dealing with both Wi-Fi and service issues.