smart home
What is a smart home?
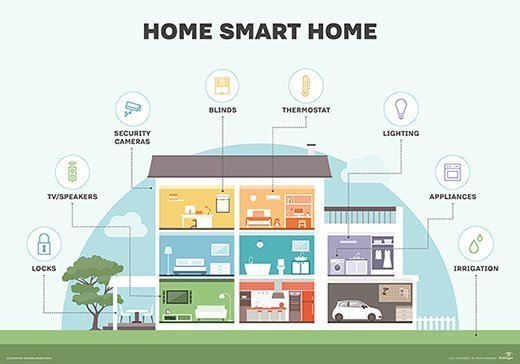
A smart home is a residence that uses internet-connected devices to enable the remote monitoring and management of appliances and systems, such as lighting and heating.
Smart home technology -- also often referred to as home automation or domotics from the Latin word domus, meaning home -- provides homeowners security, comfort, convenience and energy efficiency by letting them control smart devices, often using a smart home app on their smartphone or another networked device.
A part of the internet of things (IoT), smart home systems and devices often operate together, sharing consumer usage data among themselves and automating actions based on the homeowners' preferences.
How does smart home technology work?
A smart home isn't a collection of disparate smart devices and appliances, but rather ones that work together to create a remotely controllable network.
This article is part of
Ultimate IoT implementation guide for businesses
All devices -- such as lights, thermostats, security systems and appliances -- are controlled by a master home automation controller, often called a smart home hub. This hub is a hardware device that acts as the central point of the smart home system and can sense, process data and communicate wirelessly. It combines all the disparate apps into a single smart home app that homeowners can control remotely. Examples of smart home hubs include Amazon Echo, Google Home and Wink Hub. While many smart home products use Wi-Fi and Bluetooth to connect to the smart home network, others depend on wireless protocols such as Zigbee or Z-Wave.
Smart home devices can be either programmed to follow specific schedules or commands or they can be set to respond to voice commands through home assistants such as Amazon Alexa or Google Assistant. For example, a smart thermostat can learn the homeowner's habits and automatically adjust the temperature based on their specific schedule.
Examples of smart home technologies
Nearly every aspect of life where technology has entered the domestic space -- including lightbulbs, dishwashers and other appliances -- has seen the introduction of a smart home alternative:
- Smart TVs. These TVs connect to the internet to access content through applications, such as on-demand video and music. Some smart TVs also include voice or gesture recognition.
- Smart lighting systems. In addition to being able to be controlled remotely and customized, smart lighting systems can detect when occupants are in the room and adjust lighting as needed. Smart lightbulbs can also regulate themselves based on daylight availability.
- Smart thermostats. Smart thermostats, such as Google Nest, come with integrated Wi-Fi, letting users schedule, monitor and remotely control home temperatures. These devices also learn homeowners' behaviors and automatically modify settings to provide them with maximum comfort and efficiency. Smart thermostats can also report energy use and remind users to change filters.
- Smart door locks and garage door openers. Homeowners can use smart locks and garage-door openers to grant or deny access to visitors. Smart locks can also detect when residents are near and unlock the doors for them.
- Smart security cameras and systems. With smart security cameras and doorbells, such as Ring, residents can monitor their homes when they're away. Smart motion sensors can identify the difference between residents, visitors, pets and burglars and can send notifications to authorities if suspicious behavior is detected.
- Smart pet and lawn care. Pet care can be automated with connected feeders. Houseplants and lawns can be watered using connected timers.
- Smart kitchen appliances. Brands such as LG, GE and Samsung offer smart kitchen appliances of all sorts. These appliances include smart coffee makers that can brew a fresh cup automatically at a programmed time; smart refrigerators that keep track of expiration dates, make shopping lists or even create recipes based on ingredients currently on hand; slow cookers and toasters; and, in the laundry room, washing machines and dryers.
- Smart household monitors. Household system monitors can, for example, sense a power surge and turn off appliances, sense water failures or freezing pipes and turn off the water so the home doesn't flood.
- Smart plugs. These connect to wall sockets to transform simple home devices, such as lamps and ceiling fans, so they can be controlled remotely via mobile apps and voice assistants such as Alexa.
Smart home pros and cons
Smart technology offers numerous advantages, ranging from the convenience of running household appliances such as the washing machine while at work, to the comfort of remotely adjusting the thermostat on a chilly winter day.
Common advantages of a smart home include the following:
- Provides assurance. Homeowners can monitor their homes remotely, countering dangers such as a forgotten coffee maker left on or a front door left unlocked.
- Accommodates user preferences for convenience. For example, users can program their garage door to open, the lights to go on, the fireplace to turn on and their favorite music to play once they arrive home.
- Offers peace of mind. IoT devices enable family members or caregivers to remotely monitor the health and well-being of seniors, allowing them to safely remain at home longer, rather than moving to an assisted residence.
- Improves efficiency. Instead of leaving the air conditioning on all day, a smart home system can learn homeowner behaviors to ensure the house is cooled down by the time they return home.
- Saves resources and money. With a smart irrigation system, the lawn is watered only when needed and with the exact amount of water necessary. With home automation devices and a smart system setup, energy, water and other resources are used more efficiently, which helps save both natural resources and money for the consumer.
- Manages tasks. Smart virtual assistants, such as Google Home or Amazon Echo, can accomplish tasks through speech recognition and voice commands. For example, homeowners can use voice commands to turn on music, search the web and control their household smart devices.
However, home automation systems have struggled to become mainstream, in part due to their technical nature. Common disadvantages of a smart home include the following:
- Requires a reliable internet connection. An unreliable internet connection or a network going down in the event of an outage can leave the devices and gadgets connected to a smart home inoperable.
- Perceived complexity. Some people have difficulties or a lack of patience with technology. Smart home manufacturers and alliances are working on reducing complexity and improving the user experience to make it enjoyable and beneficial for users of all technical levels.
- Lack of standards. For home automation systems to be truly effective, devices must be interoperable regardless of manufacturer and use the same protocol or, at least, complementary ones. As it's a relatively new market, there's no gold standard for home automation yet. However, standard alliances are partnering with manufacturers and protocols to ensure interoperability and a seamless user experience.
- Questionable security. IoT devices introduce security challenges because most of them lack built-in encryption. In addition, they can serve as access points for the broader network's sensitive data, increasing the attack surface. According to a recent report from consumer IoT market research firm Parks Associates, 55% of consumers are concerned about the security of their smart home devices. If hackers can infiltrate a smart device, they could potentially turn off the lights and alarms and unlock the doors, leaving a home defenseless to a break-in.
- Lack of data privacy. Many smart homeowners also worry about data privacy. According to the Parks Associates' research report, about 72% of consumers expressed worry or strong concern regarding the security of their personal data collected and transmitted by smart home devices. Likewise, they're equally concerned about the potential unauthorized access or control of smart devices without their permission. While smart home device and platform manufacturers collect consumer data to better tailor their products or offer new and improved services to customers, trust and transparency are critical to manufacturers looking to gain new customers.
- Expense. Even though prices are coming down, many smart home devices are still expensive, and an entire house makeover could cost thousands of dollars.
How to set up a smart home
Newly built homes are often constructed with smart home infrastructure in place. Older homes, on the other hand, can be retrofitted with smart technologies.
Zigbee and Z-Wave are two of the most common home automation communications protocols in use today. Both use mesh network technologies and short-range, low-power radio signals to connect smart home systems. Though both target the same smart home applications, Z-Wave has a range of 30 meters versus Zigbee's 10 meters, with Zigbee often perceived as the more complex of the two. Zigbee chips are available from multiple companies, while Z-Wave chips are only available from Sigma Designs. Also, Matter -- the newest smart home standard that was launched in November 2022 -- is gaining momentum. Developed by the Connectivity Standards Alliance -- previously the Zigbee Alliance -- Matter is supported by major smart home manufacturers including Amazon, Apple and Google. This IP-based protocol is specifically designed to solve the compatibility challenges of smart homes, providing a framework that facilitates seamless communication across devices, apps and cloud services.
Some smart home systems can be created from scratch, for example, using a Raspberry Pi or other prototyping board. Other systems can be purchased as a bundled smart home kit -- also known as a smart home platform -- that contains the pieces needed to start a home automation project.
While setting up a smart home can sometimes be complex, homeowners should consider the following general steps:
- Invest in a strong, reliable internet connection. Because smart home connectivity relies heavily on an internet connection, it's important to ensure the homeowner has reliable and fast internet service.
- Select the hub. It's important to decide which hub to use for a smart home. For example, if the homeowner wants a fully automated smart home, a hub that can centrally control every device is most likely required. However, in other cases, a virtual assistant that can link to other devices on the same network could suffice. Most average hubs might not include extra capabilities such as built-in voice control, even if they're compatible with a wide range of devices. On the other hand, smart speaker hubs, such as Amazon Echo, let users provide voice commands and accomplish various tasks, such as inquiring about the weather or requesting a grocery list.
- Start with the basics. Start with basic items such as smart plugs, smart bulbs and switches for the smart home, as they're quick to set up and can easily automate many different things around the house. For example, smart plugs can automate fans, lights, lamps, slow cookers, curling irons and space heaters.
- Secure the devices. Because most IoT and smart home devices don't have in-built security or encryption, it's important to set up strong passwords and multifactor authentication to prevent unauthorized access to these devices.
- Add more devices. As the homeowner becomes more comfortable with creating a smart home, they can add more devices, such as security systems, cameras and video doorbells, to the mix.
In simple smart home scenarios, events can be timed or triggered. Timed events are based on a clock, for example, lowering the blinds at 6 p.m., while triggered events depend on actions in the automated system; for example, when the owner's smartphone approaches the door, the smart lock unlocks and the smart lights go on.
Machine learning and artificial intelligence are becoming increasingly popular in smart home systems, enabling home automation applications to adapt to their environments. For example, voice-activated systems, such as Amazon Echo or Google Home, contain virtual assistants that learn and personalize the smart home to the residents' preferences and patterns.
Smart buildings
While every smart home is a smart building, not every smart building is a smart home. Enterprise, commercial, industrial and residential buildings of all shapes and sizes -- including offices, skyscrapers, apartment buildings and multi-tenant offices and residences -- are deploying IoT technologies to improve building efficiency, reduce energy costs and environmental damage, ensure security and improve occupant satisfaction.
Many of the same smart technologies used in the smart home are also deployed in smart building technology, including lighting, energy, heating and air conditioning, and security and building access systems.
For example, a smart building can reduce energy costs using sensors that detect how many occupants are in a room. The temperature can automatically adjust, turning on cool air if sensors detect a full conference room, or turning the heat down if everyone in the office has gone home for the day.
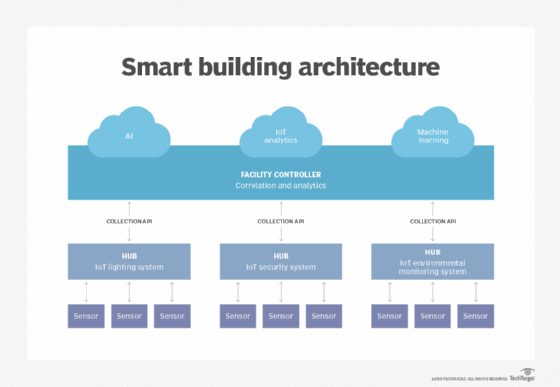
Smart buildings can also connect to the smart grid. Here, smart building components and the electric grid can talk and listen to each other. This technology can manage energy distribution more efficiently, handle maintenance proactively and power outages can be responded to more quickly.
Beyond these benefits, smart buildings can provide building owners and managers with the benefit of predictive maintenance. Janitors, for example, can refill restroom supplies when usage sensors monitoring the soap or paper towel dispensers indicate they are low. Maintenance and failures also can be predicted in building refrigeration, elevators and lighting systems.
The origins of the smart home
Smart home technology has come a long way in the past few decades. The following timeline shows significant events in the history of smart home technology:
- 1975. With the release of X10, a communication protocol for home automation, the smart home, once a pipe dream a la The Jetsons, came to life. X10 sends 120 kHz radio frequency bursts of digital information onto a home's existing electric wiring to programmable outlets or switches. These signals convey commands to corresponding devices, controlling how and when the devices operate. A transmitter could, for example, send a signal along the house's electric wiring, telling a device to turn on at a specific time. However, because electrical wiring isn't designed to be free from radio-band noise, X10 wasn't always fully reliable. Signals would be lost and, in some cases, signals wouldn't cross circuits that were wired on different polarities, created when 220-volt service is split into a pair of 100-volt feeds, as is common in the U.S. Additionally, X10 was initially a one-way technology, so while smart devices can take commands, they can't send data back to a central network. Later, however, two-way X10 devices became available, albeit at a higher cost.
- 1984. The American Association of Home Builders coined the term smart house to promote the concept of technology in home design.
- 2005. Home automation company Insteon introduced technology that combined electric wiring with wireless signals. Other protocols, including Zigbee and Z-Wave, have since emerged to counter the problems prone to X10.
- 2007. The first smart TVs were released. They offered integrated internet-connected services, such as streaming and access to user-generated content.
- 2011. Newly founded Nest Labs released its first smart product, the Nest Learning Thermostat. The company also created smart smoke and carbon monoxide detectors and security cameras. After being acquired by Google in 2015, Nest became a subsidiary of Alphabet Inc.
- 2012. SmartThings Inc. launched a Kickstarter campaign, raising $1.2 million to fund its smart home system. Following additional funding, the company entered the market in August 2013 and was acquired by Samsung in 2014.
- 2014. Amazon Echo, Amazon Alexa and Apple HomeKit were introduced, making a giant leap in voice-enabled smart devices.
- 2016-2018. The arrival of smart speakers, such as Google Home, Google Nest, Apple HomePod and Sonos signaled a significant shift in how users interacted with smart home devices.
- Today. Home automation trends continue to evolve, with more connectivity options and features.
Future developments in smart device technology will combine language models and virtual assistants, such as ChatGPT. Some companies are already using this technology to build their own personal assistants, while Amazon is currently working on a significant language model called large language model to improve Alexa.
When selecting the appropriate IoT communication protocol, it's important to recognize that not all protocols fit every device or deployment. Explore the top 12 IoT protocols and standards to find the best one for your needs.






