multiprocessing
What is multiprocessing?
Multiprocessing is the utilization of two or more central processing units (CPUs) in a single computer system. Its definition can vary depending on the context, but generally it refers to a system's ability to support multiple CPUs and its capacity to distribute work among them.
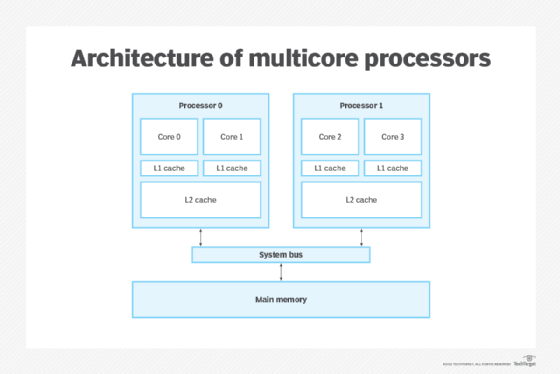
Multicore processors today are easily capable of having 12, 24 or even more microprocessor cores on the same motherboard, enabling the effective and concurrent processing of numerous tasks.
What are processes?
A process, or a running process, is a collection of instructions carried out by the computer processor.
A process's execution must proceed in a sequential manner. For example, a computer program is written in a text file, but once executed, it turns into a process and performs all the tasks mentioned in the program sequentially.
Process examples
A normal computer runs a number of processes continuously to help manage the operating system (OS), the hardware and the applications installed on the machine. This can range from a simple background task like a spell-checker or system event handler to a full-fledged application such as Microsoft Word.
In Microsoft Windows, each process running on a computer can be observed by opening the Processes tab in the Task Manager. The processes are typically background programs that a user doesn't normally see while using the computer.
The following processes can be observed through the Task Manager:
- Winlogon.exe. This process belongs to the Windows login manager and is responsible for security handling, such as loading user profiles and locking computer screens while a screensaver is running.
- Wininit.exe. This process runs continuously and helps set up the system at the initial login. Its primary role is to serve as a launchpad for the majority of background programs and processes that start with Windows.
- Csrss.exe. The csrss.exe process used to manage Windows graphical components, but today, its two most important functions are shutting down Windows and starting the conhost.exe process, which starts the Command Prompt.
- Printer programs. Any printer program is a process that runs in the background, monitoring the ink levels and other settings while a computer is running.
Types of multiprocessing systems
Multiprocessor or parallel processing systems are commonplace. They use shared memory and distribute the computer clock, memory, bus and peripherals among several concurrent processors. Multiprocessing is divided into the following three types:
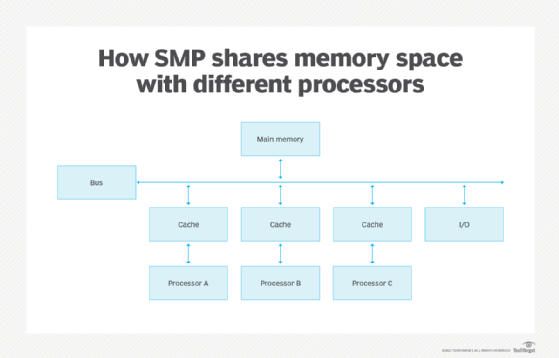
- Symmetric multiprocessing (SMP). In SMP or tightly coupled multiprocessing, the processors share memory and the input/output (I/O) bus or data path. A single copy of the OS manages all the processors. SMP, also known as a shared everything system, doesn't usually exceed 16 processors.
- Asymmetric multiprocessing (AMP). Prior to the development of symmetric multiprocessors, only asymmetric multiprocessors were available. Each processor in an asymmetric system is given a predetermined task. A primary-secondary relationship exists in an AMP system, where all the processors receive instructions from a primary processor. AMP is a cheaper option than SMP.
- Massively parallel processing (MPP). In MPP, or loosely coupled processing, up to 200 or more processors can work on the same application. Each processor has its own OS and memory, but an interconnect arrangement of data paths lets messages be sent between processors. Typically, the setup for MPP is more complicated, requiring thought about how to partition a common database among processors and how to assign work among the processors. An MPP system is also known as a shared nothing system.
Process vs. thread
There's a common misconception that processes and threads are the same when, in fact, they are separate execution sequences.
The following are examples of the differences between a process and a thread:
- A process is a section of a running program, while a thread is a portion of a process.
- Threads are lightweight compared to processes.
- When a process ends, it does it more slowly than a thread.
- The creation of a process requires more time than the creation of a thread.
- Processes require more time for context switching, whereas threads need less time.
- Unlike threads, which share memory, a process is largely segregated.
- Data isn't shared across processes, but it is shared between threads.
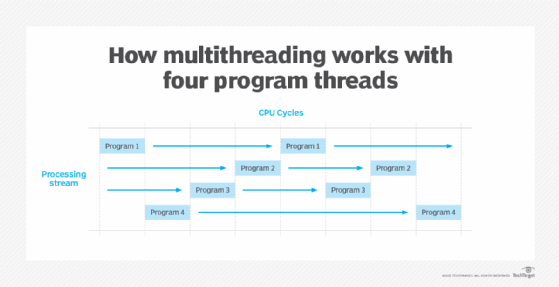
Multiprocessing can also be confused with multitasking or time sharing, the management of programs and the system services they request as tasks that can be interleaved, and with multithreading, the management of multiple execution paths through the computer or of multiple users sharing the same copy of a program.
Multiprocessing challenges
While multiprocessing improves system performance and reliability, it does come with the following challenges as well:
- Expensive. Systems with multiple processors might be pricey. Having just one processor is less expensive than having two or more. It's advisable to only invest in several processers if they will pay off in the long run because, in addition to the upfront expense, maintaining them is expensive.
- Deadlocks. In systems with multiple processors, a deadlock can occur if one processor attempts to access an I/O device while another processor is trying to use it.
- Extra memory requirements. Due to their improved computing capability, multiprocessor computers are widely used. However, they do come with increased memory requirements. In multiprocessing architectures, memory is shared across all processes and each processor requires memory space. All processors work together and simultaneously access the main memory directly, which causes an increase in memory consumption.
- Complex operating system. In multiprocessing OSes, each CPU has its own operating system, which assigns each processor with several minor tasks and the load is distributed among the processors. However, the use of multiple processors makes it more complex for the OS to function.
Multiprocessing advantages
Multiprocessing environments are widely adopted and offer a wide range of advantages such as increased speed, throughput and reliability. Common benefits of multiprocessing include the following:
- Reliability. If one processor fails in a multiprocessor system, the other processors can pick up the slack and continue to function. While the shutting down of one processor might cause a gradual slowdown, the system can still function smoothly. This makes multiprocessing systems highly reliable.
- Increased throughput. Throughput is the number of processes executed at a given time. Given that multiprocessor systems use many CPUs to handle data, increased performance is expected when the system uses parallel processing. This means more tasks can be accomplished in a shorter amount of time, as they're divided among different processors.
- Cost saving. Multiprocessing systems are more economical compared to multiple single processor systems. This is because multiple processors within a single system share the same memory, disk space, buses and peripherals.
Multiprocessing vs. multiprogramming
Besides the process versus thread misconception, multiprocessing is sometimes confused with multiprogramming, or the interleaved execution of two or more programs by a processor. Today, the term is rarely used as all but the most specialized computer OSes support multiprogramming. While multiprocessing and multiprogramming are related concepts, they have different meanings.
Multiprogramming refers to the concurrent execution of multiple programs on a single CPU. The CPU switches rapidly between programs, providing the illusion that they're all running simultaneously. The main benefit of multiprogramming is to increase CPU utilization, as the CPU is never idle.
Multiprocessing, on the other hand, refers to the concurrent execution of multiple processes on multiple CPUs. During multiprocessing, a CPU can execute different processes simultaneously. The main benefits of multiprocessing are increased throughput and reduced latency, as multiple processes can be executed at the same time without interfering with each other.
In a nutshell, multiprogramming involves running multiple programs on a single CPU, while multiprocessing involves running multiple processes on multiple CPUs.
Symmetric multiprocessing, asymmetric multiprocessing and massively parallel processing are types of multiprocessing. Learn how these modes differ from one another and become familiar with each one's unique use cases.








