microblogging
What is microblogging?
Microblogging is a short blog post designed for quick and typically direct audience interactions. These concise blogs are shared using social media platforms like Twitter or Instagram, and can include different content formats such as audio, text, images or video.
Microblogging enables users to weigh in on trending topics or reach friends or family, and organizations to reach their prospective audiences. Shared content includes user-generated content, event highlights, news updates, memes and quotes.
The appeal of microblogging is both its immediacy and portability. Posts are brief -- typically 140 to 280 characters -- and can be written or received using a variety of devices, including smartphones.
Microblogging is a fast way to communicate with audiences. As opposed to writing pages of text like in a traditional blog, a microblog enables quick conversational posts with others. For brands, it can be a way to make product announcements or clarifications, link to longer content posts, seem more personable or engage in conversations with customers.
In the U.S., for example, former President Barack Obama microblogged during his campaigns using Twitter, one of the most popular microblogging sites. Traditional media organizations, including The New York Times and the Advanced Press, send headlines and links in microblog posts. Other potential applications of microblogging include live traffic reports, sports updates and emergency broadcast messages.
Benefits of microblogging
Benefits of microblogging include the following:
- More frequent posts. Microbloggers can share short messages more often when compared to writing longer, more in-depth traditional blogs.
- Less time needed to create a post. Users can create shorter microblog posts faster than longer forms of content.
- Conducive for time-sensitive information. Posts or tweets can share breaking news, event information, trending topics or other timely information.
- Mobile friendly. Microblogs are typically shared on mobile devices, making them accessible to people anywhere.
- Direct communication with followers. The short-form communication style of microblogging facilitates interaction by enabling users to leave comments, retweet, like and share and posts.
- Marketing. Organizations can use microblogs as a form of content marketing by sharing images, promotions and links to their products.
Microblogging vs. traditional blogging
The main difference between traditional blogs and microblogs are their length. Blogs are more long form and can be anywhere from one paragraph to many pages. Microblogs, however, are smaller and more concise.
It takes less time to create a microblog while quickly facilitating communication with an audience. Blogs take more time to create and focus on a typical one-way communication. While traditional blogs can be hosted on many different websites, microblogs are typically hosted on social networking websites like Twitter, Facebook or LinkedIn.
Because traditional blogs are longer, they typically contain more in-depth and information-rich content. Blogging sites can also provide instructional resources or provide commentary on a topic. With the limited number of characters, microblogs create quick interactions with an audience and focus on a specific topic or message. They are also conducive to mobile platforms, where short posts can be created and shared quickly while on the go.
Popular microblogging platforms
Microblogging platforms typically include popular social media sites like the following:
- Twitter is a quick way to share short posts, links and other content up to a 280-character limit.
- Users can send messages and share numerous content types with families, friends and groups.
- Owned by Meta (Facebook), Instagram is a visual and video microblogging service.
- A popular platform for connecting with businesses and professionals, LinkedIn is known as a professional networking site.
- This popular short-form video social media app enables users to share video-based microblogs.
- Users can link to photos of products, style inspiration, recipes and other useful information.
Tips for writing effective microblogs
The first step in creating an effective microblog is to choose the platform it will be posted on. The platform selected should fit the type of content to be posted. For example, if an image is the central part of the microblog, then the post would work best on Twitter or Instagram, even though a microblogging site like Facebook would also work. Likewise, short videos work best on TikTok or as a Reel on Instagram. Text posts work well on platforms like Facebook or Twitter, and strictly business -- typically business-to-business -- posts perform best on LinkedIn.
Each platform can host a variety of content types; however, content typically found on each include the following:
- Instagram typically fits visual and short video content.
- Facebook typically fits text, visual and linked content.
- Twitter typically fits text, visual and linked content.
- LinkedIn typically includes text and linked content.
- TikTok typically fits short-form video content.
- Pinterest typically fits visual content.
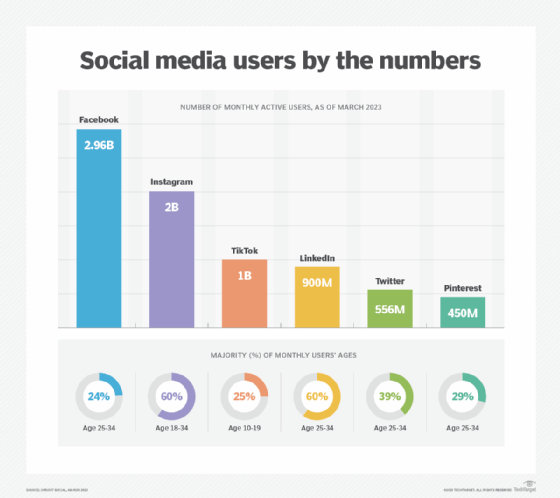
The target demographic of each platform may help determine which is best to post on. For example, according to SproutSocial:
- Facebook has 2.91 billion monthly active users; the majority (5%) are age 25-34.
- Instagram has 2 billion monthly active users; the majority (31.2%) are age 25-34 and 31% are age 18-24.
- TikTok has 1 billion monthly active users; the majority (25%) are age 10-19.
- Twitter has 211 million daily active users; the majority (42%) are age 18-29.
- LinkedIn has 810 million monthly active users; the majority (58.4%) are age 25-34.
- Pinterest has 431 million monthly active users; the majority (38%) are age 50-64.
Demographics and statistics can also be broken down by gender and time spent on the platform.
Microblogs can include any type of content, however, businesses making microblogs should ensure they're posting relevant content that informs their followers but stays within their brand's image. Microblogs could include content like status updates, links to longer-form content, videos, infographics, memes and quotes.
The following are some extra tips for making an effective microblog:
- Make content easily digestible.
- Use humor.
- Share personal stories and experiences.
This can help make posts more relatable and entertaining.
Using an automation tool like SproutSocial will help an organization schedule posts or create the same post for multiple websites at once.
Learn about 12 social media marketing tips that can help boost an organization's microblogging posts in this article.








