IT controls
What are IT controls?
An IT control is a procedure or policy that provides a reasonable assurance that the information technology (IT) used by an organization operates as intended, that data is reliable and that the organization is in compliance with applicable laws and regulations. IT controls can be categorized as either general controls (ITGC) or application controls (ITAC).
IT controls provide criteria an IT organization should follow to ensure that staff members are performing roles and responsibilities according to standards, regulations and established good practices.
Why are IT controls important?
An IT general control should demonstrate that the organization has a procedure or policy in place for technology that affects the management of fundamental organizational processes such as risk management, change management, disaster recovery and security. IT application controls, which are actions that a software application does automatically, should demonstrate that software applications used for specific business processes (such as payroll) are properly maintained, are only used with proper authorization, are monitored and are creating audit trails.
Controls provide a framework for how specific activities and functions should perform. They are particularly important when it is necessary to demonstrate compliance with specific standards (e.g., ISO 27001 and NIST SP 800-34), regulations (e.g., GDPR) and legislation (e.g., SOX, GLBA, HIPAA and FISMA).
Senior management needs to know and have evidence that the IT department is managing the firm’s IT operations in a way that maximizes performance and minimizes risk. Audits using IT controls can demonstrate that the technology infrastructure is supporting the company's business goals.
Who needs to know about IT controls?
Within an IT department, the IT audit team (if one is available) needs to know about the IT controls that are in place. Corporate internal audit departments will likely have information on IT controls, especially if they perform IT audits. Third-party audit firms will need to have (and demonstrate) significant expertise in and knowledge of IT controls.
Members of IT audit teams will need to be knowledgeable of not only their own areas, but also other areas and activities. Typically, they can be either specialists in specific activities such as data storage, or they can have broader expertise in many IT functions.
What are IT general controls?
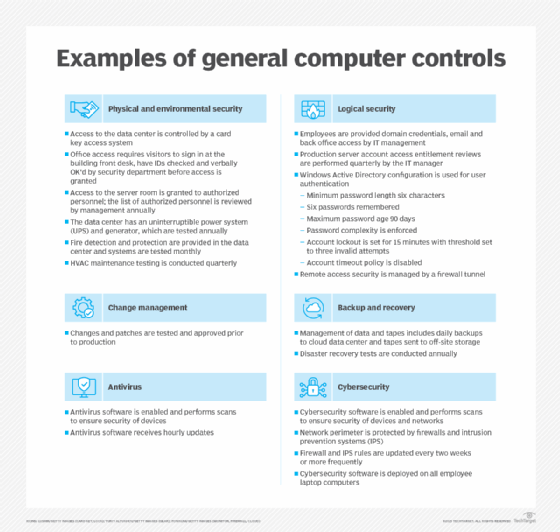
IT general controls (ITGCs) focus on how systems perform within the context of the confidentiality, integrity and availability of information. The table below, "Examples of general computer controls," presents a sampling of IT general controls by category followed by examples of actual control statements.
IT application controls (ITAC) are similar to ITGCs and focus on applications and the technology platforms supporting them.
Audit controls to ensure compliance
IT controls are often linked to specific standards, regulations, legislation and other good practice guidelines. They can be structured to align with requirements specified in the rules being addressed. As an audit progresses, the IT controls being examined are concurrently indicating how well the IT organization is complying with the rules and guidelines. For example, IT controls addressing information security can be mapped to requirements of ISO 27001 or NIST SP 800-53. These are two of the most widely used standards for information security; compliance with their specifications is an important achievement.
Compliance with specific frameworks is also important. Two important frameworks include the Committee of Sponsoring Organizations (COSO) and Control Objectives for Information and Related Technologies (COBIT). The former integrates IT and other control types into business operations, while the latter focuses more specifically on IT controls and their impact on the business.
Follow our checklist of six IT general controls you need to address. Compare ISO 31000 versus COSO risk management standards.







