accumulator
What is an accumulator?
An accumulator is a type of register for short-term, intermediate storage of arithmetic and logic data in a computer's central processing unit (CPU). However, the term is rarely used in reference to contemporary CPUs, having been replaced around the turn of the millennium by the term register.
Role of an accumulator
An accumulator is primarily used as a register in a CPU to store intermediate logical or arithmetic data in multistep calculations. For such calculations, it functions as a temporary storage location. It holds the intermediate results of each such operation, with the value getting progressively overwritten after every operation.
For example, in an operation that involves adding multiple numbers, the accumulator would first hold the result of adding the first two numbers. Then the next number is added and the new result replaces the previous result in the accumulator. This action continues until all the numbers have been added and the final total is available. Once this sum has been determined, it's written to the main memory or another register.
Need for an accumulator in older computing systems
A CPU with an accumulator-based architecture always stores the intermediate results of calculations in a special register even if it has several others. This special register is the accumulator. An accumulator machine is known as a 1-operand machine.
The main purpose of accumulators in 1-operand machines was to speed up calculations. Without an accumulator, the CPU would have to write the result of each calculation to the main memory in a multistep operation and then read back the result for use in the next step. The more steps in the operation, the more times the CPU would have to perform these write/read functions.
A computer's main memory is larger than an accumulator. Also, the technology used for it is slower and cheaper. As a result, it takes longer to access this memory compared to the accumulator register, which slows processing speeds and performance and thus generates results at a slower speed. These speeds can be increased by using an accumulator for intermediate storage.
Evolution of accumulators
In the early days of computing, the accumulator was an integral part of computing systems because it provided a much-needed way to temporarily hold intermediate values for lower processing requirements.
For instance, the world's first programmable general-purpose electronic digital computer, the ENIAC (Electronic Numerical Integrator And Computer), had more than a dozen accumulators built into its CPU. Other early computers were also accumulator machines, including:
- IBM 701
- IBM 650
- IBM 7070
- Digital Equipment Corp.'s (DEC) PDP-6 and PDP-10
- Hewlett-Packard (HP) 2100
However, as computing and CPU technology advanced, the accumulator became obsolete. Newer computing architectures and multicore designs usually avoid the term accumulator and more often reference a general-purpose register. Also, modern CPUs are usually 2-operand or 3-operand machines where more general-purpose registers are used for these additional operands.
The registers are used as the source and destination for calculations, which is why they aren't considered accumulator machines. In modern computers, any general-purpose register can function as an accumulator since it offers greater flexibility. However, accumulators are still used in some special-purpose processors for intermediate data storage.
Accumulator in noncomputing applications
The term accumulator is also used in many noncomputing applications and activities, including:
- Electrical engineering. An energy storage device such as a rechargeable battery or ultracapacitor.
- Hydraulics. As an energy storage device.
- Stock trading. Refers to a contract or agreement that involves buying or selling equities.
- Gambling. Refers to a parlay bet where a bettor makes multiple wagers and ties them together into the same bet.
Hydraulic accumulators
In hydraulics, an accumulator is an energy storage device. In this sense, it's analogous to a rechargeable electrical battery. A hydraulic accumulator stores and discharges energy in the form of a pressurized fluid. It uses the ability of a gas, such as nitrogen, to be compressed and decompressed to store and maintain hydraulic pressure.
In addition, a hydraulic accumulator is used to:
- reduce pressure peaks;
- dampen shocks, vibrations and pulsations;
- support power chassis suspensions; and
- improve the efficiency of hydraulic systems.
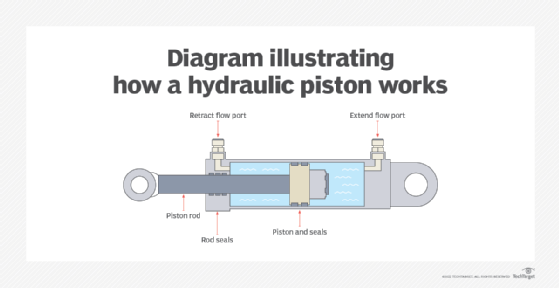
How a hydraulic accumulator works
A typical hydraulic accumulator holds hydraulic fluid and uses a compressible gas to store hydraulic pressure. When the fluid flows into the accumulator, the gas inside is compressed so the fluid is stored as "fluid with energy."
To use the device, the gas volume is pre-charged, which results in its expansion. When that happens, the gas fills most of the accumulator and only a small amount of fluid remains inside. When the hydraulic pump is operated, the system pressure increases, which forces the fluid to enter the accumulator. Since the fluid pressure exceeds the pre-charge pressure, the gas volume becomes compressed, creating a source of stored energy.
When the system and gas pressures are in equilibrium, the flexible barrier inside the pump -- usually a piston or rubber bladder -- stops moving. At that point, the charging cycle restarts. When there's a system demand due to actuator movement downstream, for example, the pressure in the hydraulic system falls and the accumulator releases the stored, pressurized fluid to the circuit.
Types of hydraulic accumulators
There are three main types of hydraulic accumulators.
Bladder accumulators. Most hydraulic systems use bladder accumulators, which are well-suited for general-purpose and shock applications. These accumulators have large ports for rapid fluid discharge and a pressure ratio of 4:1. This is the maximum pressure to gas-charged pressure. It helps protect the accumulator's bladder from distortion and material strain.
Piston accumulators. A piston accumulator consists of a movable aluminum piston separating the fluid and gas sections. They're suitable for large stored volumes of fluid -- 100 gallons or more -- because of their high flow rates. They can also be used in rugged and heavy-duty applications. The drawbacks of these accumulators is that they're more sensitive to contamination and prone to seal damage.
Diaphragm accumulators. Diaphragm accumulators operate in a similar manner to bladder accumulators, but instead of a rubber bladder they use an elastic diaphragm to separate the fluid from the gas. These accumulators can handle compression ratios of up to 10:1, and are relatively economical, compact and lightweight devices. They can quickly respond to changes in pressures and are insensitive to contamination. These benefits make them suitable for shock applications and for applications with cycle demands of 1 million to 3 million.
See also: cache, arithmetic-logic unit, stack pointer, program counter
