actionable intelligence
What is actionable intelligence?
Actionable intelligence is information that can be immediately used or acted upon -- either tactically in direct response to an evolving situation, or strategically as the result of an analysis or assessment.
Regardless of the industry or situation, all actionable intelligence can lead to better decision-making; this lets systems and human users make more accurate and timely decisions that can improve performance and outcomes.
The concept of actionable intelligence, or actionable information, applies to many different industries, including the following:
- IT. Actionable intelligence can be the result of a data analysis -- such as a log analysis -- that reveals potential systemic hardware or software issues, which reactively need, or proactively might need, remediation.
- Business. Actionable intelligence can be the result of big data analytics that offer insights into business operations that suggest possible business opportunities. These could include a new product variation, market opportunity or possible business vulnerabilities such as a workflow bottleneck or inefficiency. This is often called business intelligence.
- Security. Actionable intelligence could be the reveal of a tangible threat such as video surveillance or tripped alarms in a physical setting, or warnings from intrusion detection or antimalware software deployed within a data center infrastructure.
- Government. Actionable intelligence could be the result of a roadway or bridge inspection that requires repairs and upgrades to that physical infrastructure.
- Law. Actionable intelligence can mean that available information meets the legal requirements for a justifiable, or actionable, lawsuit.
- Military. Actionable intelligence can include indications of troop and supply movements from satellite and drone imagery, which provide current indications of opponent objectives and might be current and accurate enough to commit assets for contact.
- Medicine. Actionable intelligence can include data collected from medical devices such as test results or a big data analysis of medical imaging data to help doctors arrive at a fast and accurate diagnosis for the most effective treatment.
How is actionable intelligence used in IT?
From a tactical perspective, actionable intelligence is an indication of an immediate threat or disruption -- such as a system or application failure to the IT infrastructure -- which can affect the applications and data that users rely upon.
Tactical information is typically collected from software instrumentation, agents, logs, tools and platforms deployed within the IT environment. For example, agents might check on the heartbeat of key applications and services to ensure they're operational or use an intrusion prevention system to oversee the flow of network traffic and watch for anomalous activity.
Tactical information is usually delivered to IT administrators and other stakeholders in real time using dashboards and other messaging platforms such as texts and emails. For the examples above, a lost application or server heartbeat, or a potential network intrusion, produces an alarm to administrators. Today, tactical information is increasingly coupled with automation to provide immediate, policy-driven responses to alerts and problems. For example, a lost heartbeat from a containerized application component could automatically respawn that container in an attempt to fix the problem without any human intervention -- warnings and alerts to administrators are intended for follow-up and further investigation.
From a strategic perspective, actionable intelligence represents more long-term assessments and analysis of the data for the IT infrastructure over time across the environment.
Strategic information is frequently collected from logs and varied analytical tools deployed and configured to track and report on key IT resources and assets. For example, a system management tool or platform might watch the bandwidth use of major network segments, keep tabs on storage capacity and utilization, and correlate logs to look for potential system vulnerabilities or recurring errors that might suggest an impending fault.
Strategic information is generally delivered to IT professionals and business managers in the form of periodic reports and visualizations such as charts and graphs intended to illustrate trends. For the examples above, reporting that consistently shows increasing network or storage utilization might be the justification for improvements or upgrades. Similarly, reporting of error or fault trends could call for preemptive system replacement or repair before a significant and unexpected failure results in unplanned downtime.
What are the advantages and disadvantages of actionable intelligence?
The adoption of actionable intelligence resources poses numerous benefits and challenges an organization must consider. Benefits of actionable intelligence in business and IT can include the following:
- Opportunity. The analytical processes of big data and artificial intelligence can be used on actionable intelligence initiatives to yield strategic business insights, expose new business opportunities or reveal potential business vulnerabilities, limitations and risks.
- Safety. Sensors and internet of things technologies can deliver real-world data for real-time analysis and comparison against known-good operational conditions to reveal possible sources of impending failures. For example, an air pressure sensor in a car tire can help drivers maintain optimum tire conditions for best mileage or alert a driver to a tire problem immediately.
- Availability. Knowing the actual operational condition of a device or system can help businesses take proactive steps to better maintain equipment and subsystems to avoid unnecessary troubleshooting and extended downtime. For example, knowing that a server's power supply is delivering voltages outside of recommended ranges can cause the operations staff or automated orchestration tools to move workloads to other servers to take the stricken server offline for repairs before its power supply fails and unexpectedly affects workload availability.
- Revenue and cost-savings. Much of actionable intelligence in business and IT focuses on issues of money -- whether finding new opportunities to generate revenue or forestalling failures and extending system lifecycles to realize cost savings for the enterprise.
Despite the benefits, there are several disadvantages organizations must consider before and during adoption of actionable intelligence practices, including the following:
- Investment. Actionable intelligence isn't free. An enterprise must invest considerable resources into building the computing infrastructure needed. This ranges from sensors to networks to computing and data sets, and even the tools that process data and generate actionable intelligence outputs. Investments can also include additional staffing needed to deploy, maintain and operate the actionable intelligence infrastructure.
- Alignment. Actionable intelligence is all about answering questions. But to get the right answers, a business must ask the right questions. This requires careful planning from inception and use case development, through design and deployment, to reporting and human follow-through. Actionable intelligence only has value when it has an actual purpose. Lack of business alignment, or purpose, can easily leave insights ignored -- wasting the entire investment.
- Change. Actionable intelligence is an ever-evolving effort, as models change and new data becomes available. A business must regularly revisit its actionable intelligence infrastructure and update those resources regularly to keep the effort relevant and useful. This requires ongoing investment.
- Reliability. Actionable intelligence isn't perfect. A preemptive warning isn't a guarantee of impending failure, and a suggested business vulnerability isn't a foreshadowing of bankruptcy. Actionable intelligence can be wrong. Business and technology leaders must review output objectively and triage each warning or report based on business needs.
What is the difference between intelligence and actionable intelligence?
Intelligence is knowing what's going on. Actionable intelligence is knowing what to do about it. In practical terms, actionable intelligence is information that's coupled with intent or context.
Consider the example of a home thermostat that reports an uncomfortably warm indoor temperature of 82 degrees Fahrenheit. Simply knowing the indoor temperature represents intelligence -- the current temperature measurement is little more than a data point.
The data becomes actionable when it's coupled with context such as the setpoint for a home heating and cooling system. When the homeowner sets the desired inside temperature to 74 degrees Fahrenheit, the thermostat's reading becomes actionable because it now drives the operation of the home's central air conditioning which should automatically engage to maintain the desired temperature.
The data can be further actionable if the home's air conditioning doesn't engage in response to the measured temperature, or the home's interior temperature doesn't experience an adequate drop over time. Such situations could indicate a failure in the air conditioning system -- which could require repair services -- or an open door or window -- which could indicate a potential security issue. Both cases require the direct intervention of the homeowner.
How to use actionable intelligence
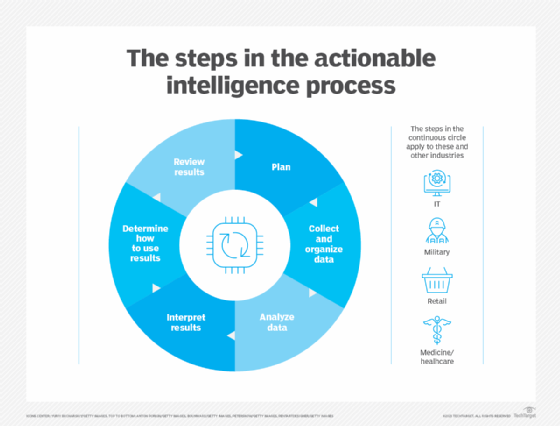
There are many types of actionable intelligence applied to industries from logistics to military to retail environments and beyond. Consequently, there's no single way to gather or use actionable intelligence. Practitioners can often employ the following six-step process:
- Plan. Any actionable intelligence project should start with the end goal in mind. Understand the purpose of the project and how the organization should benefit from the results now and into the future.
- Collect and organize data. With the goals in mind, consider the data that should be generated and collected to reach those goals. For business and IT-oriented projects, gathering data typically involves deploying sensors and software instrumentation.
- Analyze data. Consider how the collected data should be analyzed. Various types of data can require preprocessing such as data normalization and data cleaning. The business will rely on models and data analytics tools to ingest the data, perform correlation and processing, as well as yield outputs. The models and processing requirements can vary dramatically, depending on the scope and goals of the project.
- Interpret results. Once outputs arrive, human operators can interpret results to consider recommendations or recognize potential problems. Results might be specific and detailed or general and basic, depending on the complexity of the project and the data detail available.
- Determine how to use the results. With outputs in hand, business and technology leaders can make informed decisions about the disposition of those results -- whether to take immediate action or plan more long-term responses such as upgrades or workflow changes to best utilize the actionable intelligence.
- Review results. The review is often the most difficult and overlooked part of the project. Practitioners must ask whether the actionable intelligence -- and the decisions arising from that intelligence -- had the intended impact on the business. If not, the project might need to be re-evaluated. For example, if a logistics business fits sensors into its truck fleet to track locations to optimize routes, the business should objectively consider whether the optimizations improved delivery performance or saved fuel costs.
Business intelligence can help give organizations an edge over their competitors. Learn how to create and implement an effective BI strategy







