active attack
What is an active attack?
An active attack is a network exploit in which a hacker attempts to make changes to data on the target or data en route to the target.
There are several different types of active attacks. However, in all cases, the threat actor takes some sort of action on the data in the system or the devices the data resides on. Attackers may attempt to insert data into the system or change or control data that is already in the system.
Types of active attacks
What follows are some of the most common types of active attacks.
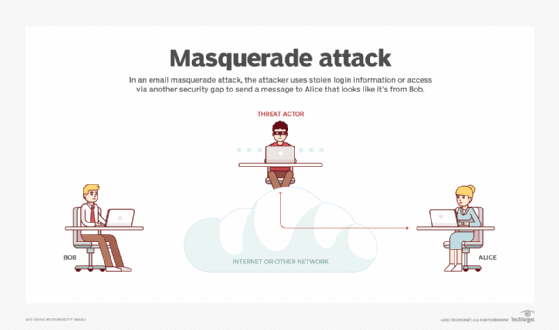
Masquerade attack
In a masquerade attack, the intruder pretends to be a particular user of a system to gain access or to gain greater privileges than they are authorized for. Masquerade attacks are conducted in several different ways, including the following:
- using stolen login identifications (IDs) and passwords;
- finding security gaps in programs; and
- bypassing the authentication
An attempt may come from an employee inside an organization or from an outside threat actor using a connection to the public network. Weak authentication can provide a point of entry for a masquerade attack and make it easy for an attacker to gain entry. If attackers successfully receive authorization and enter the network, depending on their privilege level, they may be able to modify or delete the organization's data. Or they may make changes to network configuration and routing information.
For example, an outside attacker can use spoofed Internet Protocol (IP) addresses to bypass the victim's firewall and gain access from an unauthorized source. To do this, the attacker may use a network sniffer to capture IP packets from the target machine. Another device is used to send a message to the firewall with the forged IP address. The firewall then permits access to the victim's machine.
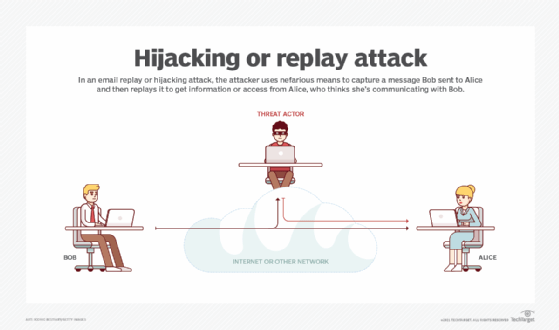
Session hijacking attack
A session hijacking attack is also called a session replay attack. In it, the attacker takes advantage of a vulnerability in a network or computer system and replays the session information of a previously authorized system or user. The attacker steals an authorized user's session ID to get that user's login information. The attacker can then use that information to impersonate the authorized user.
A session hijacking attack commonly occurs over web applications and software that use cookies for authentication. With the use of the session ID, the attacker can access any site and any data that is available to the system or the user being impersonated.
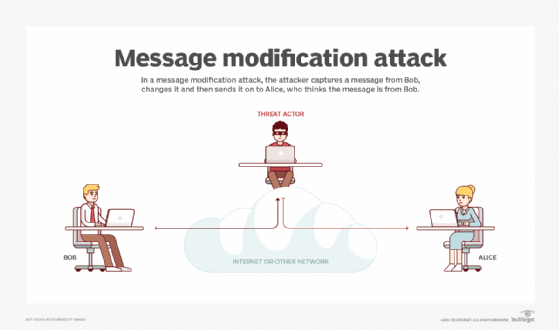
Message modification attack
In a message modification attack, an intruder alters packet header addresses to direct a message to a different destination or to modify the data on a target machine. Message modification attacks are commonly email-based attacks. The attacker takes advantage of security weaknesses in email protocols to inject malicious content into the email message. The attacker may insert malicious content into the message body or header fields.
DoS attack
In a denial-of-service (DoS) attack, the attackers overwhelm the victim's system, network or website with network traffic, making it difficult for legitimate users to access those resources. Two ways a DoS attack can occur include:
- Flooding. The attacker floods the target computer with internet traffic to the point that the traffic overwhelms the target system. The target system is unable to respond to any requests or process any data, making it unavailable to legitimate users.
- Malformed data. Rather than overloading a system with requests, an attacker may strategically send data that a victim's system cannot handle. For example, a DoS attack could corrupt system memory, manipulate fields in the network protocol packets or exploit servers.
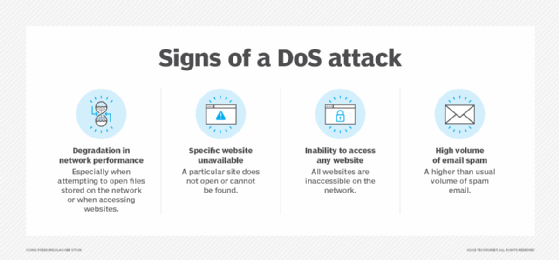
In a distributed DoS (DDoS) exploit, large numbers of compromised systems -- also referred to as a botnet or zombie army -- attack a single target with a DoS attack. A DDoS uses multiple devices and locations to launch requests and overwhelm a victim's system in the same way a DoS attack does.
What are passive attacks?
Active attacks contrast with passive attacks, in which an unauthorized party monitors networks and sometimes scans for open ports and vulnerabilities. Passive attackers aim to collect information about the target; they don't steal or change data. However, passive attacks are often part of the steps an attacker takes in preparation for an active attack.
Examples of passive attacks include:
- War driving. This is a wireless network reconnaissance method that involves driving or walking around with a laptop computer and portable Wi-Fi-enabled wireless Ethernet card to find unsecured wireless networks. Once found, these attackers use these networks to illegally access computers and steal confidential information.
- Dumpster diving. This passive attack involves intruders searching for information on discarded devices or for notes containing passwords in trash bins. For example, the attacker can retrieve information from hard drives or other storage media that have not been properly erased.

How to prevent an active attack
There are several ways to counter an active attack, including the following techniques:
- Firewalls and intrusion prevention systems (IPSes). Firewalls and IPSes are security systems designed to block unauthorized access to a network. A firewall is part of the network security infrastructure. It monitors all network traffic for suspicious activity and blocks any it identifies. It also has a list of trusted senders and receivers. Similarly, an IPS monitors network traffic for malicious activity and acts when an attack is detected.
- Random session keys. A session key is a temporary key created during a communication session that is used to encrypt the data passed between two parties. Once the session ends, the key is discarded. This provides security because the keys are only valid for a specific time period, which means no one else can use them to access the data after the session has ended.
- One-time passwords (OTPs). These passwords are automatically generated numeric or alphanumeric strings of characters that authenticate users. They are only valid for one use. OTPs often are used in combination with a username and password to provide two-factor authentication.
- Kerberos authentication protocol. This authentication protocol is a system for authenticating users for network services based on trusted third parties. It was developed at the Massachusetts Institute of Technology in the late 1980s. Kerberos authentication is a way to prove to a network service that a user is who they say they are. It provides a single sign-on service that enables users to use the same login credentials (username and password) to access multiple applications.
Learn how to create a cybersecurity strategy to prevent active and other types of attacks in this cybersecurity planning guide.