
telephony
What is telephony?
Telephony is technology associated with interactive communication between two or more physically distant parties via the electronic transmission of data. Long associated with voice communication, telephony has evolved to also include text messaging, video calling, video conferencing, voicemail, call recording and faxing. Telephony provides an efficient and effective means of communication for individuals and businesses.
A telephonic exchange historically required the use of traditional fixed-line telephones, handheld devices containing both transmitters and receivers that connected to local exchange networks via physical wiring. Telephonic communication increasingly happens using modern computing and cellular technology, thus blurring the line between telephony and telecommunication. The definition of telephony and its scope have expanded accordingly.
Internet telephony lets users make calls over Internet Protocol (IP) networks at a much lower cost than over the traditional public switched telephone network (PSTN). Computer applications called softphones behave like legacy telephones but without the need for standalone devices. IP telephony software can reside on a variety of computing hosts, including PCs, smart desk phones, smart mobile phones and tablets.
How telephony works
How telephony works depends on the form of telephony implemented. For example:
- Traditional telephony. Traditional phone systems convert sound waves at one end of a call into electrical signals that travel to their destination via the wires and cables of the PSTN -- the circuit-switched telephone network that crisscrosses the globe. The recipient's phone then converts the transmission back into sound signals, enabling a real-time conversation. Also known as the plain old telephone service or POTS, the PTSN is operated by international, national, regional and local carriers. Its underlying infrastructure originally featured copper lines but now includes fiber-optic cabling, cellular technology and satellite systems.
- Mobile telephony. Using cellular technology, a mobile phone converts sound into electrical signals that it broadcasts via radio waves to a local cell tower. The cellular network uses radio signaling to forward this information to the recipient's phone, which, in turn, converts the signals back into sound.
- Internet telephony. Internet telephony software converts sound waves into data that travels over packet-switched computer networks, enabling voice calls to occur online and independent of the PSTN and cellular systems.
Voice over IP (VoIP), a Layer 3 protocol and subset of IP telephony, delivers voice and other communication services, such as video conferencing and text messaging, across broadband and private IP networks. VoIP and IP telephony are two similar forms of telephony. There isn't a substantial difference between them, as many IT professionals use the two terms interchangeably. However, some experts argue that VoIP specifically refers to sending voice traffic over an IP network -- while IP telephony is a broader umbrella term referring to any telephone-type communication service carried over IP. - Faxing. Legacy fax -- short for facsimile -- technology is similar to traditional voice telephony. Instead of using sound waves as the mechanism for converting data, a fax machine's sensor encodes a printed document, which it interprets as a two-dimensional, fixed bitmap. The machine then converts that graphic into electronic signals. Those signals traverse the telephone network and arrive at the receiving fax machine, which reconverts and decodes the signals, reassembling and printing them to reflect the original document.
IP faxing, also known as fax over IP or virtual faxing, functions much like traditional faxing but via the internet. Software encodes a scanned document and converts it into data that can travel over local or wide area IP networks before being decoded and reconverted on the receiving end.
Benefits of telephony
Telephony provides the following benefits:
- Low-cost calling and messaging.
- VoIP services can talk to anyone with a phone number.
- The recipient of a VoIP voice call doesn't need special equipment.
- Increased accessibility, as telephony systems are available in multiple forms such as text messaging, video conferencing, voicemail and faxing.
- Added mobility using tools such as softphones.
Downsides of telephony
Some downsides associated with telephony, however, include the following:
- Requires a reliable internet connection.
- Not all VoIP providers can connect to emergency services directly.
- Call quality is susceptible to network jitter.
- Emergency calls have limited location tracking options.
History of telephony
The word telephony comes from the Greek root words for far -- tele -- and speak -- phone. In 1876, Alexander Graham Bell famously patented the telephone to electronically transmit human speech, building on the success of the telegraph system. A few days later, he spoke the first words ever communicated via telephone to his assistant, Thomas Watson, who was in the next room: "Mr. Watson, come here. I want to see you." The following year, he made the first distanced phone call in history -- from Salem, Mass., to Boston -- and founded the Bell Telephone Company, which would later become part of AT&T.
This article is part of
Ultimate guide on enterprise unified communications strategy
The earliest telephones came in pairs, with each line directly connecting just two locations. This was impractical, however, as users needed a separate wired device for each contact they wished to call. Soon, the invention of the telephone exchange enabled users to communicate with any other local party wired for service, with the help of a switchboard operator. Trunk lines connected individual telephone exchanges, enabling calls to take place over increasingly significant distances.
AT&T began planning a cross-country telephone line in 1908, eventually laying 3,400 miles of copper wiring from coast to coast. Engineers used innovative loading coils and vacuum tubes to amplify electrical signals as they made their way across the country.
Thirty-nine years after filing his patent, Bell inaugurated the transcontinental telephone service with a ceremonial call from New York to San Francisco. He repeated his now-famous words: "Mr. Watson, come here. I want to see you." Watson replied from California: "It will take me five days to get there now." President Woodrow Wilson and AT&T President Theodore Vail joined them on the call.
Other major milestones in the history of telephony include the following:
- 1889. Almon Strowger invents the first automatic telephone switch.
- 1956. The first submarine transatlantic telephone cable system was launched between Europe and North America.
- 1965. AT&T deployed the first all-electronic telephone switch, enabling advanced features such as call waiting.
- 1969. The Advanced Research Projects Agency Network, an experimental predecessor of the internet, came to fruition with the successful interconnection of four university computers.
- 1973. Computer scientist Danny Cohen pioneered Network Voice Protocol, the forerunner to VoIP, at the University of Southern California.
- 1983. Motorola debuted the first commercially available mobile phone. Nicknamed "The Brick," the DynaTAC weighed two pounds, took 10 hours to charge and sold for $3,995 each.
- 1994. Smartphones became available to the public with the launch of IBM's Simon Personal Communicator.
- 1995. VocalTec released Internet Phone, considered the first commercially available VoIP service.
- 1999. The Internet Engineering Task Force standardizes Session Initiation Protocol, a key network protocol underlying many online telecommunication services.
- 2003. Skype launched its revolutionary free VoIP service, later adding video functionality.
- 2011. Google debuted the open source Web Real-Time Communications project, enabling voice and video communication across standard web browsers without the use of plugins.
- 2020. The COVID-19 pandemic forced businesses that relied on on-premises infrastructure to rethink their communication strategies when employees began working remotely. Many businesses began using telephony tools such as Zoom or Microsoft Teams, which provided features such as video calling, call recording and file sharing.
- 2023. The rivalry between Zoom and Microsoft Teams continues, as many organizations provide their employees with a flexible hybrid work environment where employees work partly in the office and partly remote.
4 types of telephony systems for the enterprise
- Legacy, circuit-switched PBX. In traditional phone systems, on-premises private branch exchange (PBX) boxes act as in-house switching centers, connecting calls between internal devices directly and routing external calls to and from the PSTN via dedicated trunk lines. Human operators managed the earliest PBX systems but were eventually replaced by modern automated attendants.
While expensive and complex -- and more or less obsolete -- legacy PBX systems have historically been most attractive in areas with unreliable network connectivity or electrical power. Some hard-wired phone lines continue to work even in the event of electrical outages. - VoIP PBX. Similar to the traditional PBX, a VoIP or IP PBX essentially creates a private phone network within a business but does so via the internet or a private local area network rather than dedicated voice circuits.
Because it doesn't require a separately wired network or rely on the PSTN -- with its long-distance charges -- internet telephony is significantly less expensive than legacy PBX systems. It also offers more geographic flexibility to users, as they can access softphone applications across their devices, rather than staying tethered to desk handsets.
On-premises IP PBX telephony systems consist of software running on servers. An onsite IP PBX typically offers more sophisticated feature sets and greater reliability than a cloud-based VoIP service, but it's also more expensive and complex to deploy, manage and maintain. - Hybrid PBX. Some organizations deploy a hybrid PBX model that uses both legacy and IP telephony technology -- whether for redundancy, cost savings or to enable a staged migration to VoIP. These environments use gateways to bridge VoIP and PSTN functionality.
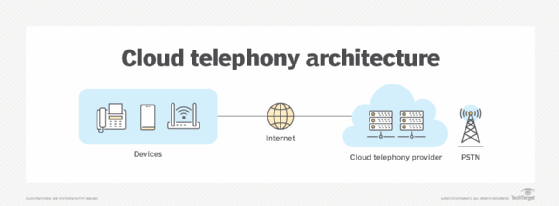
Alternatively, some use the term hybrid PBX to refer to a VoIP telephony system with both on-premises and cloud-hosted resources. - Cloud VoIP. Cloud VoIP, also known as cloud telephony or cloud calling, is a VoIP service provided by a third party. By outsourcing its system, an enterprise can eliminate the need to provision, manage and maintain an onsite IP PBX, reducing infrastructure costs and increasing scalability. Features, functionality and controls tend to be less comprehensive than on-premises options, although many analysts expect that difference to shrink with time.
Key telephony use cases
There are a range of potential individual and business use cases for telephony technologies. For example, telephony is used for sending text messages, making voice calls, video calling, business conferences, leaving voicemails as well as sending faxes.
Other use cases of telephony systems include the following:
- Making international calls.
- Sending Short Message Service (SMS) text messages.
- Sending or receiving banking documents via fax.
- Conducting video and audio business calls.
- Using communication software that can integrate with other business tools.
- Group or team messaging.
- File sharing.
Telephony platforms and vendors
Today, organizations can choose from a plethora of on-premises and cloud-based VoIP telephony vendors, from major carriers to up-and-coming startups. These include the following examples:
- 8x8.
- AT&T.
- Avaya.
- Broadvoice.
- Cisco Webex.
- Dialpad.
- Google.
- Microsoft.
- Mitel Networks.
- RingCentral.
- Verizon.
- Vonage.
Some example telephony services include the following:
- Cisco Unified Communications Manager. CallManager is an on-premises voice-based VoIP telephony system.
- MiVoice Business by Mitel. MiVoice is a voice-based VoIP phone system featuring call center software and collaboration tools.
- Ringover. Ringover offers text, voice and video telephony systems using mobile and web apps.
- JustCall by SaaS Labs. JustCall is a VoIP telephony software for voice calls and SMS and Multimedia Messaging Service messages.
- Ultatel Cloud Business Phone System. This is a cloud-based voice, video, SMS and fax telephony service.
IP telephony and VoIP are similar technologies. Learn more about each and the differences between them.







