beta test
What is a beta test?
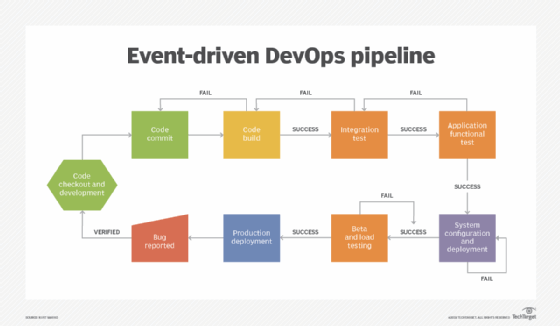
In software development, a beta test is the second phase of software testing in which a sampling of the intended audience tries out the product. Beta testing can be considered pre-release testing.
The first phase of testing in a software development lifecycle (SDLC) is known as alpha testing; alpha is the first letter of the Greek alphabet. This first phase includes unit testing, component testing and system testing.
Beta is the second letter of the Greek alphabet and is used to denote the second testing phase of the SDLC. Specifically, it is pre-release testing -- testing that is performed by a small group of real users in a real-world environment before the software is released to other customers or end users.
Beta testing is also sometimes referred to as user acceptance testing or end-user testing. In this phase of software development, applications are subjected to real-world testing by the intended audience for the software. The experiences of the early users are relayed to the developers, who make final changes before the software is released commercially. This feedback helps the development team improve the product, make it user-ready and minimize the risks of product failure.

Who performs beta testing?
Beta testing can be accomplished in house or by outsiders. In both cases, the performance testing is done in a real environment to assess how the application behaves under actual production conditions and to understand if there are any problems that need to be fixed before the final product release.
For in-house testing, volunteers or paid test subjects use the software. For widely distributed software, developers might make the test version available for download on the web as a free trial. Making software widely available in this way can also serve as a preview to stimulate interest for the final product.
Types of beta testing
There are many types of beta testing a software product. The two most common types are open beta testing and closed beta testing.
- Open beta testing. In an open beta test, a large number of testers put the product through its paces before its final release. Often, these people are members of the general public. In many cases, the product is released via online channels, and the development team determines which feedback provided by the public testers should be incorporated prior to release.
- Closed beta testing. In contrast, a closed beta test involves a limited number of people who evaluate the application and provide feedback to developers. The testers are usually some of the company's current customers rather than from the general public. The product's early adopters and paid beta testers might also be part of a closed beta test.
Other types of beta testing include the following:
- Traditional beta testing. Users from the target market test the product, and their feedback is incorporated to improve the product quality.
- Focused beta testing. Testers evaluate a specific feature, component or functionality of the new or revised software application.
- Technical beta testing. The organization's employees, or groups of employees, test the product and provide feedback to the development team.
Many organizations also adopt post-release beta testing. As the name suggests, this process involves testing the application after it has already been released to end users. A subset of these users test the product and provide feedback that can be incorporated in subsequent releases.
Beta testing lifecycle
A software beta test process always starts with test planning. In this first stage of the beta testing lifecycle, the development team defines the testing goal and creates a beta test plan. The plan includes key information such as the test objective, scope, testing criteria, schedule, budget, and methods for collecting and evaluating feedback. It can also specify the tools that will be used for beta testing. Examples of beta test tools include UserTesting, Instabug, Rainforest QA, TestFlight and TestRail.
Once the beta test strategy and plan are in place, testers are recruited. For closed beta tests, early adopters, existing customers or paid testers are given access to the product's beta version. For open beta tests, the team releases the product online and invites participation from the general public.
Once the product is available for beta testing, the testers use one of the provided tools to test the product. They provide feedback in the required format, which the development team then evaluates. The team then implements relevant or feasible feedback to address as many bugs and errors as possible. Usually, developers don't act on feedback related to suggestions for the addition of new features or functionalities. However, they might choose to introduce a feature if it won't appreciably delay product launch or if it could appreciably improve user experiences.
Once the most serious problems are fixed, the team readies the product for release. They might also reward or pay the testers for their efforts.
Beta testing benefits
Beta testing is important because it reveals bugs and errors in the software application that might have been missed during development and alpha testing. These errors, if left in the software, can affect user experiences and negatively impact the product's success and the organization's reputation. By finding problems before release, undesirable consequences can be avoided.
Beta testing also enables development teams to evaluate the performance of the application being tested. Testers test the product in the "real world" and provide feedback that developers can then incorporate to improve the product prior to release.
A beta test also provides opportunities to test the product's stability and reliability, and to confirm that it meets stated requirements and satisfies user needs. In many cases, the outcomes of a beta test inform the software product's marketing and promotional strategy.
Some beta tests involve end users or customers. Inviting them to test the product before its release helps create an atmosphere of involvement during the product development process, which can help increase interest in the final product as well as cultivate loyalty to the product and organization.
Learn about the phases of the software testing lifecycle.
