binary file
What is a binary file?
A binary file is a file whose content is in a binary format consisting of a series of sequential bytes, each of which is eight bits in length. The content must be interpreted by a program or a hardware processor that understands in advance exactly how that content is formatted and how to read the data. Binary files include a wide range of file types, including executables, libraries, graphics, databases, archives and many others.
Electronic files are typically categorized as either binary files or text files. It could be argued that text files are also a type of binary file because, like any electronic file, they're made up of sequences of bytes. However, the two are generally considered to be different types. Text files are in a human-readable format and typically adhere to specific character sets, such as Unicode.
How is a binary file used?
Binary files are not human readable and require a special program or hardware processor that knows how to read the data inside the file. Only then can the instructions encoded in the binary content be understood and properly processed.
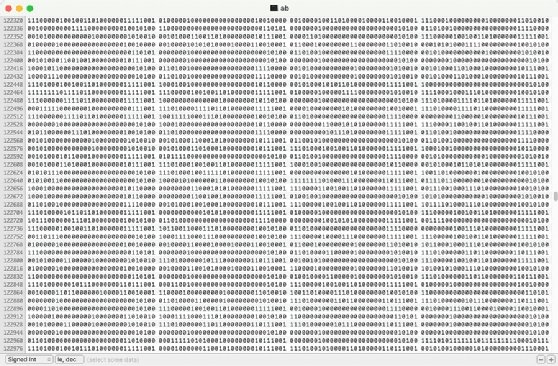
The following screenshot shows part of the content from a file on a Mac computer. The content can be understood only by specific system architectures such as Mac. The file in this figure is a Unix executable binary file. As is typical with binary files, the file's content is a series of sequential bytes, lined up one after the other. Although we can view the bytes that make up the binary data, the file can be properly interpreted only by the target platform.
A binary file often includes some type of header that indicates the type of file. The header might include a few human-readable characters, but a binary file as a whole requires specific software or hardware to read the file and take action. On the other hand, a user can open a text file in a wide range of editors and make sense of the content without needing any special type of interpreter.
Binary files are commonly used when building applications and other types of software. However, developers do not work directly with the binary files. Instead, they build their applications in a high-level programming language such as C++ or Java. The languages use human-readable text files to define the application logic.
At certain intervals in the development process, the text files are submitted to a compiler that translates the source code into machine code, bytecode or another programming language. If the compiler generates bytecode, the bytecode will eventually be converted to machine code.
Machine code is submitted to a computer's processor in the form of binary files. The machine code files must target a specific computer platform, which refers to the combination of operating system and hardware architecture. For example, the binary machine code might target Windows and the Intel line of microprocessors, or it might target macOS and the Apple M-series chips. A different compiler is usually required for each computer platform.
In general, executable -- or ready-to-run -- programs are identified as binary files and given a filename extension such as .bin or .exe. Programmers often talk about an executable program as a binary or will refer to their compiled application files as binaries. These types of files might also be referred to as object code.
In terms of transmitting files from one place to another, a file can be transmitted as a binary, meaning the programs handling it don't attempt to look within it or change it. Instead, they just pass it along as a chunk of ones and zeros, the meaning of which is unknown to any network device.
Learn the differences between interpreted vs. compiled languages, declarative vs. imperative programming and Kotlin vs. Swift open source programming languages.
