block cipher
What is a block cipher?
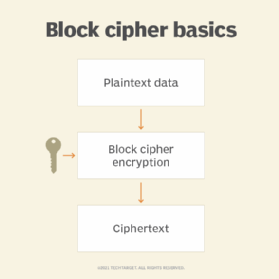
A block cipher is a method of encrypting data in blocks to produce ciphertext using a cryptographic key and algorithm. The block cipher processes fixed-size blocks simultaneously, as opposed to a stream cipher, which encrypts data one bit at a time. Most modern block ciphers are designed to encrypt data in fixed-size blocks of either 64 or 128 bits.
How does a block cipher work?
A block cipher uses a symmetric key and algorithm to encrypt and decrypt a block of data. A block cipher requires an initialization vector (IV) that is added to the input plaintext in order to increase the keyspace of the cipher and make it more difficult to use brute force to break the key. The IV is derived from a random number generator, which is combined with text in the first block and the key to ensure all subsequent blocks result in ciphertext that does not match that of the first encryption block.
The block size of a block cipher refers to the number of bits that are processed together. Data Encryption Standard (DES) and Advanced Encryption Standard (AES) are both symmetric block ciphers.
The DES block cipher was originally designed by IBM in 1975 and consisted of 64-bit blocks and a 56-bit key. This cipher is not considered secure anymore, due to the short key size, and was replaced in 1998 by AES. AES uses a 128-bit block size and a 128-, 192- or 256-bit key size.
What are the different modes of operation in block cipher?
Block ciphers only encrypt messages that are the same size as their block length, so each block of plaintext with more or less blocks needs to be encrypted separately. The following block cipher modes of operation define how these blocks are encrypted:
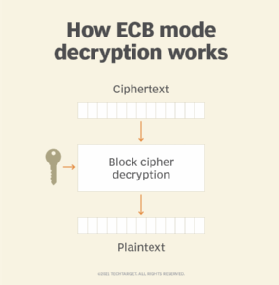
- Electronic codebook (ECB) mode. ECB mode is used to electronically code messages as their plaintext form. It is the simplest of all block cipher modes of operation. It does not add any randomness to the key stream, and it is the only mode that can be used to encrypt a single-bit stream. This means that each plaintext symbol, such as a character from the plaintext alphabet, is converted into a ciphertext symbol using the cipher's key and a substitution alphabet. Each plaintext block is encrypted independently of all the other blocks. If a plaintext block is only 8 bytes, only 8 bytes of the key are used; if a plaintext block is 100 bytes, all 100 bytes of the key are used.
- Cipher block chaining (CBC) mode. CBC mode is a method of encrypting data that ensures that each block of plaintext is combined with the previous ciphertext block before being encrypted. The symmetric key algorithm creates a ciphertext that depends on all plaintext blocks processed before it in a data stream. This is done to ensure that each block of the ciphertext is dependent on all of the previous blocks. Each plaintext block is XORed (exclusive OR) with the previous ciphertext block before being encrypted with the cipher algorithm. CBC mode is used in a variety of security applications. For example, Secure Sockets Layer/Transport Layer Security uses CBC mode to encrypt data that is transferred over the internet.
- Ciphertext feedback (CFB) mode. In contrast to CBC mode, which encrypts a set number of bits of plaintext at a time, it is sometimes necessary to encrypt and transfer plaintext values instantly, one at a time. Like CBC, CFB also uses an IV. CFB uses a block cipher as a component of a random number generator. In CFB mode, the previous ciphertext block is encrypted, and the output is XORed with the current plaintext block to create the current ciphertext block. The XOR operation conceals plaintext patterns.
- Output feedback (OFB) mode. OFB mode can be used with any block cipher and is similar in some respects to CBC mode. It uses a feedback mechanism, but instead of XORing the previous block of ciphertext with the plaintext before encryption, in OFB mode, the previous block of ciphertext is XORed with the plaintext after it is encrypted.
- Counter (CTR) mode. CTR mode uses a block chaining mode of encryption as a building block. The process of encrypting data is performed by XORing the plaintext with a sequence of pseudorandom values, each of which is generated from the ciphertext using a feedback function. The CTR encryption process can be visualized as a series of XORs between blocks of plaintext and corresponding blocks of ciphertext.
Authenticated encryption with additional data modes
The following modes provide message encryption and can supply additional data -- including sequence number or header -- that is not included in the ciphertext:
- Galois/Counter Mode (GCM). In GCM mode, blocks are combined with an IV and encrypted with AES. The result is then XORed with the plaintext to generate the ciphertext.
- Counter Mode with CBC Message Authentication Code Protocol (CCMP). CCMP mode is for use with AES. It uses a 128-bit block size and a 128-bit key size and is capable of handling messages up to 16 bytes. CCMP mode was designed to address some of the problems with the CBC mode of operation in which the same block of plaintext can encrypt to different ciphertexts.
- Synthetic IV (SIV). SIV is a byte-oriented (8-bit) substitution-permutation network AES algorithm. It takes a plaintext message and a secret key and encrypts the plaintext into ciphertext. However, it differs from other cipher modes in that it does not use a random key stream; instead, it uses a fixed key stream that is generated from a pseudorandom number generator.
- AES-GCM-SIV. AES-GCM-SIV is a combination of the AES block cipher and GCM, with the added security feature of a SIV. This enables more messages to be encrypted with the same key than with GCM-SIV.
Learn how cloud providers are tackling multi-cloud key challenges using key management as a service.





