
black box AI
What is black box AI?
Black box AI is any artificial intelligence system whose inputs and operations aren't visible to the user or another interested party. A black box, in a general sense, is an impenetrable system.
Black box AI models arrive at conclusions or decisions without providing any explanations as to how they were reached. In black box models, deep networks of artificial neurons disperse data and decision-making across tens of thousands of neurons, resulting in a complexity that may be just as difficult to understand as that of the human brain. In short, the internal mechanisms and contributing factors of block box AI remain unknown.
Explainable AI, which is created in a way that a typical person can understand its logic and decision-making process, is the antithesis of black box AI.
How does black box machine learning work?
Deep learning modeling is typically conducted through black box development. The learning algorithm takes millions of data points as inputs and correlates specific data features to produce outputs.
This article is part of
A guide to artificial intelligence in the enterprise
The process typically includes the following steps:
- Sophisticated algorithms examine extensive data sets to find patterns. To achieve this, a large number of data examples are fed to an algorithm, enabling it to experiment and learn on its own through trial and error. The model learns to change its internal parameters until it can predict the exact output for new inputs using a large sample of inputs and expected outputs.
- As a result of this training, the machine learning model is finally ready to make predictions using real-world data. Fraud detection using a risk score is an example of a use case for this mechanism.
- The model scales its method, approaches and body of knowledge as additional data is gathered over time.
It can be challenging for data scientists, programmers and users to understand how a black box model generates its predictions because its inner workings aren't readily available and are largely self-directed. Just as it's difficult to look inside a box that has been painted black, it's challenging to find out how each black box AI model functions.
In some cases, techniques such as sensitivity analysis and feature visualization can be used to provide a glimpse into how the internal processes are working, but in most cases, they remain opaque.
What are the implications of black box AI?
The majority of deep learning models use a black box strategy. While black box models are appropriate in some circumstances, they can pose several issues including the following:
AI bias
AI bias can be introduced to algorithms as a reflection of conscious or unconscious prejudices on the part of the developers, or they can creep in through undetected errors. In any case, the results of a biased algorithm will be skewed, potentially in a way that's offensive to people who are affected. Bias in an algorithm may come from training data when details about the data set are unrecognized. For example, in one situation, AI used in a recruitment application relied upon historical data to make selections for IT professionals. However, because most IT staff historically were male, the AI algorithm displayed a bias toward male applicants.
If such a situation arises from black box AI, it may persist long enough for the organization to incur damage to its reputation and, potentially, legal actions for discrimination. Similar issues could occur with bias against other groups as well, with the same effects. To prevent such damage, it's important for AI developers to build transparency into their algorithms, enforce AI regulations and commit to accountability for their effects.
Lack of transparency and accountability
The complexity of black box neural networks can prevent individuals from properly understanding and auditing them, even if they produce accurate results. Even their developers don't fully understand how these networks work, despite the fact they're capable of some of the most groundbreaking achievements in the field of AI. This can be an issue in high-stakes fields such as healthcare, banking and criminal justice, as the choices these models make can have far reaching effects on people's lives. It can also be difficult to hold individuals responsible for the judgments made by the algorithm when using opaque models.
Lack of flexibility
One of the biggest problems with black box AI is its lack of flexibility. If the model needs to be changed to describe a physically comparable object, determining new rules or bulk parameters could take a lot of work. Therefore, decision-makers shouldn't process sensitive data using a black box AI model.
Security flaws
Black box AI models are susceptible to attacks from threat actors who take advantage of flaws in the models to manipulate the input data. For instance, an attacker could change the input data to influence the model's judgment to make incorrect or even dangerous decisions.
When should black box AI be used?
Although black box machine learning models pose certain challenges, they also offer some advantages. Black box AI models should be carefully examined and incorporated when it's important to attain the following benefits:
- Higher accuracy. Complex systems such as black box provide higher prediction accuracy than more interpretable systems, especially in computer vision and natural language processing (NLP). This is because these models are able to identify intricate patterns in the data that people might not be able to see. However, the complexity of the algorithms, which provides accuracy in these models, also makes them less transparent.
- Rapid conclusions. Black box models often consist of a set of rules and equations, making them quick to run and easy to optimize. For example, calculating the area under a curve using a least-squares fit might offer a solution without requiring a thorough understanding of the problem.
- Minimal computing power. A black box model doesn't need a lot of computational resources because it's pretty straightforward.
- Automation. Black box AI models can automate complex decision-making processes, reducing the need for human intervention. This saves time and resources as well as improves efficiency.
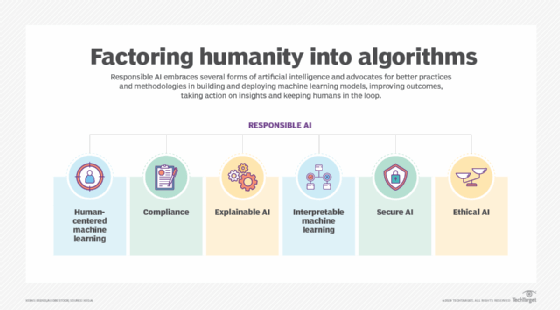
What is responsible AI?
AI that's developed and used in a morally upstanding and socially responsible way is known as responsible AI (RAI). RAI initiatives are largely driven by legal accountability.
To reduce the negative financial, reputational and ethical risks that black box AI and machine bias can create, responsible AI's guiding principles and best practices are intended to assist both consumers and producers.
AI practices are responsible if they adhere to the following guiding principles:
- Fairness. The AI system treats all people and demographic groups fairly and doesn't reinforce or exacerbate preexisting biases or discrimination.
- Transparency. The system is easy to comprehend and explain to both its users and those it will affect. Additionally, AI developers must disclose the collection, storage and usage of the data used to train an AI system.
- Accountability. The organizations and people creating and using AI should be held responsible for the judgments and acts the technology takes.
- Ongoing development. To ensure that RAI outputs are consistently in line with moral AI concepts and societal norms, continual monitoring is necessary.
- Human supervision. Every AI system should be designed to enable human monitoring and intervention when appropriate.
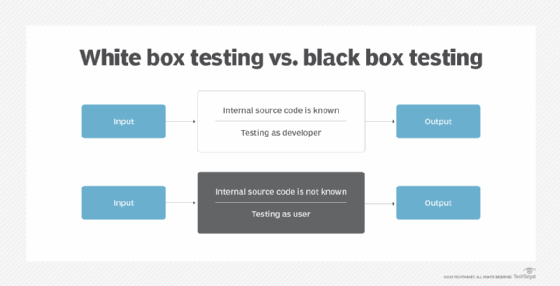
Black box AI vs. white box AI
Black box AI and white box AI are different approaches to developing AI systems. The selection of a certain approach depends on the specific applications and goals of the AI system.
While the input and outputs of a black box AI system are known, the internal workings of the system are opaque or difficult to comprehend. On the other hand, white box AI is transparent and interpretable about how it comes to its conclusions. For example, a data scientist can examine an algorithm and determine how it behaves and what variables affect its judgment.
The black box AI approach is typically used in deep neural networks, where the model is trained on large amounts of data and the internal weights and parameters of the algorithms are adjusted accordingly. This model is effective in certain applications, including image and speech recognition, where the goal is to accurately and quickly classify or identify data.
Since the internal workings of a white box system are transparent and easily understood by users, this approach is often used in decision-making applications, such as medical diagnosis or financial analysis, where it's important to know how the AI arrived at its conclusions.
The following are a few distinguishing features of both AI types:
- Black box AI is often more accurate and efficient than white box AI.
- Compared to black box AI, white box AI is easier to understand.
- Black box models include boosting and random forest models that are highly non-linear in nature and harder to explain.
- White box AI is easier to debug and troubleshoot compared to black box due to its transparent nature.
- White box AI typically includes linear, decision tree and regression tree models.
Neural networks are becoming more popular, as they come with a high level of accountability and transparency. Learn about the possibilities of white box AI, its use cases and the direction it's likely to take in the future.