
blade server
What is a blade server?
A blade server, sometimes referred to as a high-density server, is a compact device containing a computer used to manage and distribute data in a collection of computers and systems, called a network. Its role is to act as a conduit between computers, programs, applications and systems.
A blade server typically consists of a chassis, or box-like structure, housing multiple thin, modular electronic circuit boards, known as server blades. They're called blades because of their ultra-thin shape. Each blade contains a single server, often dedicated to a single application. The information within blade servers is stored on a memory card or other memory device.
In addition, the individual blades contain processors, memory, integrated network controllers, an optional Fibre Channel (FC) host bus adapter and other input/output ports. These are used to connect server blades to other server blade units within the system or to connect individual blades to power sources.
Parts of a blade server technology system
A blade server is a small, modular server system made up of various parts that are all optimized to work together. The basic parts of a blade server system include the following:
- Chassis. The chassis is the small outer case of one or more blade servers used to store the mechanical parts, including servers and racks.
- Blades. These small mechanical parts hold servers and contain the memory systems to store data and serve information to the computer systems in a network. They sometimes appear as super thin drawers stacked on top of other blades.
- Servers. The servers within the individual blades are housed within the chassis and contain the memory, processors and programs needed to carry out their functions.
- Racks. Racks are commonly used to store many individual blade servers in a physical location such as a server room.
- A backplane. This area of a server rack connects all the individual modules and servers via cabling or circuit boards.
Uses of blade servers
To maximize their efficiency, blade servers are often dedicated to single-task functionality. Examples of tasks a server performs include the following:
- File sharing. Blade servers can be used to transfer data between digital points or devices.
- Web page serving and caching. Blade servers can be used to deliver web pages to users and to temporarily store information on the user's computer so it can be quickly recalled.
- Secure sockets layer (SSL) encryption of web communication. SSL ensures that information that travels over an internet connection is encrypted and protected from viruses and other malicious software.
- Transcoding. To display website content across a variety of end devices easily and seamlessly, blade servers can provide code conversion of website elements and mobile SEO.
- Streaming. Streaming transmits audio and video content without interruption to enable users to view and listen in real time.
- Virtualization. Blade servers can be used to create abstract versions of applications or real-life activities for digital use.
- Storage. The sleeker, more compact design of a blade server allows a larger amount of information to be stored to support a greater number of applications working in unison.
- Cluster computing. Blade servers are frequently used in cluster computing and server clustering to provide high availability, scalability, load balancing and failover services.
Benefits of blade servers
Because most blade servers are dedicated and focused on a single-use application, they provide more control over how they're accessed and used as well as how data is transferred between devices.
The benefits of blade servers compared to their traditional predecessors include the following:
- Lower heat generation. Fans cool each blade individually. Because the servers are stackable, they can be maintained in smaller climate-controlled areas that keep all of the mechanical parts at a proper temperature.
- Flexibility. Unlike their predecessors, blade servers can be controlled and managed in tandem with other server units within a data center or network. The administrator of a stack of blade servers can balance the workloads spread over many individual server devices.
- Lower costs. Organizations using blade servers can reduce the amount of cabling needed for blade server housing compared to larger models such as box servers. Because the design is modular and compact, individual units can easily be transferred within or between systems. With fewer cables and parts to deal with, IT administrators and other professionals can spend less time managing the infrastructure of their data center and more time ensuring high availability, which maximizes server performance.
- Reduced power consumption. Servers within a rack can share a single power source, reducing storage and power consumption costs compared to other types of servers. In addition, the compact nature of blade servers means they need little power. This decrease in power consumption allows teams to maximize the efficiency of their space.
- Storage consolidation. Each blade in a blade server typically comes with one or two local serial-advanced technology attachment (SATA) or Serial-Attached Small Computer System Interface (SCSI) connections. For additional storage, blade servers can connect to a storage pool facilitated by a network-attached storage, FC or iSCSI storage area network (SAN). The advantage of blade servers comes from the consolidation benefits of housing several servers in a single chassis as well as from the consolidation of associated resources -- for instance, storage and networking equipment -- into smaller architecture that can be managed through a single interface.
- Compact size. Unlike traditional rack servers, blade computing doesn't have minimum size restrictions. Because blade servers are made up of the smallest number of components required for a device to be considered a computer, they can fit in small, tight spaces and run well with other simplified servers as part of a larger overall structure.
- Compatibility. The nature of servers that carry out a highly individualized task makes it possible for an organization to dedicate a single server entirely to mission-critical applications.
- Scalability. Because of their modular design, blade servers provide high scalability, enabling enterprises to quickly add or remove server modules as needed. Blade boards can be inserted one at a time or several at once, making upgrades and technology refresh cycles easier.
Types of blade servers
Blade servers are categorized by type based on various traits, such as differing CPUs, amount of RAM and cache memory or connections.
The following are key distinguishing characteristics in terms of the equipment used in blade servers:
CPU performance
Blade servers can be equipped with different CPUs such as Intel; AMD, or Advanced Micro Devices; Motorola; and Sun Microsystems. The CPU does the processing and computing for the entire system. The more powerful it is, the more functionality the computer system can provide at a given time.
Storage media
A blade server can contain a variety of memory systems, including static RAM (SRAM), dynamic RAM (DRAM) and double data rate synchronous dynamic RAM (DDR SDRAM):
- SRAM is one of the earlier forms of information storage common in digital cameras and printers. It stores data exactly as it is.
- DRAM updates as it works and is common in more complex systems, such as video game consoles.
- DDR SDRAM is most used in servers and computers with a great deal of visual content. RAM is used to manage and store information as well as complete processing and calculations in real time.
Connection options
While blade servers have a modular, uniform design that makes them easy to move between data centers, they can have a variety of outer connectors. For example, they can be equipped with an Ethernet output, a token ring, a fiber channel that can be up to six miles long or a fieldbus network protocol. The bi-directional fieldbus network protocol enables communication between input and output devices without connecting each individual device back to the programmable logic controller. In addition, blade servers can be connected via different methods:
- Apple FireWire. FireWire ports are often used to connect digital cameras, external hard disk drives, phones, tablets and devices that require high data transfer speeds. A FireWire connection can transfer data at up to 400 megabytes per second.
- SATA. A SATA connection is a bus-style port that connects host bus adapters to hard drives, solid-state drives or other larger storage devices.
- SCSI. SCSI connects computer parts in a SCSI system and creates ports of communication between them.
- Directed attached storage. DAS is within a computer itself, or directly connected to it, and isn't part of an external storage network system. A common example is the internal hard drive of a computer or laptop.
- FC. An FC connection, or FC SAN storage connection, lets network storage devices share information with servers at high speeds with high performance.
- iSCSI. An iSCSI storage connection is based on IP and includes a storage system that's used to link various network storage locations within the same server system.
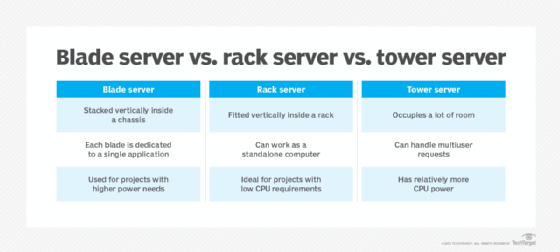
Difference between blade servers, rack-mounted servers and tower servers
Blade servers, rack servers and tower servers are common features of data centers. While similar, they have some significant differences in terms of performance and form factor.
Blade servers
Blade servers, like rack-mounted servers, are typically stored in a vertical stack in a data center or server room. However, they often appear in larger data centers and are used for projects with higher power needs.
One key difference between blade servers and rack-mounted servers is that blade servers are stripped down, with simple, sometimes singular functionality. This allows for multiple small, flat, horizontal blades containing individual servers to be stored within a chassis and stacked vertically. Unlike rack servers, blade servers generally don't function as standalone servers. They work best when placed with other servers in a chassis and combined into a blade service stack.
Another major difference between rack servers and blade servers is that each individual blade server is typically dedicated to a single application, as it typically only contains a CPU, controller and memory. Blade server systems are easier to fix than larger rack-mounted servers because the modular parts can be repaired individually or hot-swapped without disrupting the larger system.
When an organization selects a specific model of blade server, it must consider the possibility of vendor lock-in. Switching between products is costly, as it involves a complete overhaul of all the available equipment. Blade servers also require fewer wires and cables than typical stack-mounted servers, and are powerful processors compared to the space they occupy.
Rack servers
Typically, rack servers -- also known as rack-mounted servers -- are created to fit vertically within a shelf-like structure, called a rack, that's housed in a data center or server room. They're ideal for projects with low CPU requirements or that require limited physical space.
The number of servers stacked within a rack-mounted system can vary depending on the size and extent of an organization's project needs. Rack servers are fully equipped to work as a standalone computer and can run multiple, complex applications and processes using powerful memory and CPU resources. Their modularity and configurability make them convenient to assemble and store. Without the need for a large chassis to hold the servers, rack-mounted servers are ideal for projects that require less than 10 servers.
Tower servers
Tower servers are integrated desktop PCs that are much larger than blade servers or rack servers. They have a more powerful CPU, fast read memory and offer additional services such as Dynamic Host Configuration Protocol or domain name system. Although rack servers are smaller and can fit in a server chassis, tower servers can be just as powerful in terms of computing power, enabling network administrators to stack more than one server in a closet. Additional processing power and storage can be added as needed.
Future of blade servers
While blade servers are common in many organizations' server rooms, other technologies are being used as well. Brick servers -- which, unlike a blade server, don't require a chassis outer container -- offer the benefits of compactness and adaptability. Similarly, cartridge servers are as small as printer cartridges and are commonly used in various industries. In addition, modular hybrid servers address some issues with hard-wired connections, temperature management and ease of movement within a server system.
As power consumption and thermal design power increase with ever-improving technologies, the demand for servers that can be stored seamlessly and easily cooled will continues to grow.
A server's strength and adaptability are huge advantages for businesses, but selecting the right server hardware can be challenging. Discover the best server for your needs by learning about the pros and cons of various server types.







