broadband
What is broadband?
Broadband refers to telecommunications in which a wide band of frequencies is available to transmit information. Because a wide band of frequencies is available, information can be multiplexed and sent on many different frequencies or channels within the band concurrently. Multiplexing enables more information to be transmitted in a given time, much as more lanes on a highway support more cars.
Digital Subscriber Line (DSL) and cable television are downstream broadband services. As of February 2015, the U.S. Federal Communications Commission (FCC) benchmark for broadband data transfer rates is 25 megabits per second (Mbps) for download speeds. The FCC's upload speed benchmark is 3 Mbps.
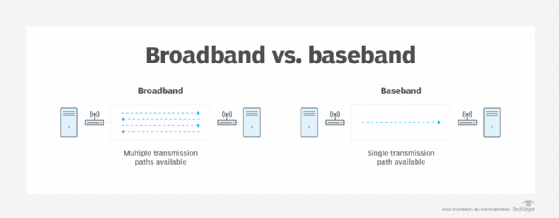
Broadband is also referred to as wideband. Baseband is a one-channel band, and narrowband is a limited-capacity transmission channel, just wide enough to carry voice.
What does broadband do?
Broadband technology transmits data over a high-speed, high-bandwidth communication network. It's typically used to provide a high-speed internet connection via an internet service provider (ISP). ISPs can deliver both wired and wireless broadband internet connections, but these broadband providers most often use a wired connection for high-speed internet access. These types of broadband internet services use one of several different technologies, such as the following:
- Copper twisted pair.
- Ethernet via fiber optic cable.
- Coaxial cable.
- DSL from the local telephone company.
- 4G or 5G mobile communication technology.
- Satellite links via a fixed earth station.
Broadband vs. baseband
A broadband data transmission system supports multiple frequency bands, whereas baseband serves only one base band for transmission. Both technologies support multiple concurrent transmissions, but certain equipment must be deployed at each end to accommodate the different signaling methods.
Broadband vs. Wi-Fi
Wi-Fi is the wireless delivery of high-speed connections. IEEE maintains numerous wireless standards based on the 802.11 specification; each describes different parameters for wireless data delivery, wireless devices and wireless access points (AP) that connect to an internet source.
In a home or small business, a wireless router transmits and receives signals from a laptop, tablet, smartphone or other device with built-in wireless components. The router can be physically connected to another network that links to an ISP, or the device can connect directly to a wireless carrier for the internet connection.
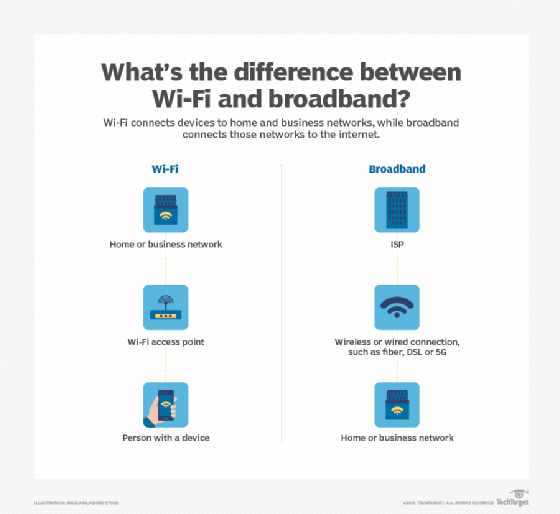
When these technologies are disrupted, it's important to identify where the disruption occurred. With Wi-Fi, the in-building wireless AP may be unaffected, and the disruption has likely occurred somewhere else in the link to company applications and the internet.
With broadband, the physical connection between devices and the internet or corporate networks can be disrupted at many different points. Diagnostic equipment can isolate the likely point of disruption.
A physical broadband connection is more secure than the wireless portion of a Wi-Fi connection, which can be compromised. Regardless of the technology used, security is essential.
Strengths and limitations of broadband
Broadband delivers higher data speeds than baseband. Reliability and availability are also better with broadband connections. A broadband connection is typically on all the time, ready when a device is activated. And many different types of physical and wireless connections can be supported.
On the negative side, disruptions to an ISP can interrupt connections. Broadband networks may be more expensive than baseband, depending on the service configuration and carrier that provides the service. As with any network connection, security can be compromised, underscoring the need for strong protective measures.
Learn more about wireless communications in our complete guide.