carrier network
A telecommunications carrier network is the collection of devices and underlying infrastructure used to transmit data from one location to another. The data transmission service is sold as a commodity, either directly to the end user or to a reseller.
For the internet to function, computers and other devices must be connected. For example, for a computer or smartphone to show this webpage, there must a physical path for the data to travel from the TechTarget servers to the user's device. Obviously, a single long cable connecting them is not practical.
Various carriers own and maintain the equipment that handles the job of transmitting data from one point to another and interconnecting different carrier networks. Also, in some cases, internet service providers (ISPs) own these carrier networks and sell services to end users.
As an illustration, when you buy an item online, the store generally does not handle the delivery of the package. It uses various services -- such as the U.S. Postal Service, UPS or FedEx -- to get the package from the warehouse to your front door. The same is true of cellular voice and data services. The originating carrier network, an individual's provider, may not own the networking equipment that delivers texts or calls to their final destinations.
Large and complex configurations of interconnected hardware make up carrier networks. This infrastructure provides communications services to people spread over large geographic areas, and it can distribute massive quantities of data over great distances. Regulatory agencies authorize telecom carriers to operate telecommunications systems and provide service.
Today, most carrier networks are optimized to convey data. Specialized carriers exist for other types of services, such as telephony, television and certain medical or surveillance equipment.
Cellphone carrier networks
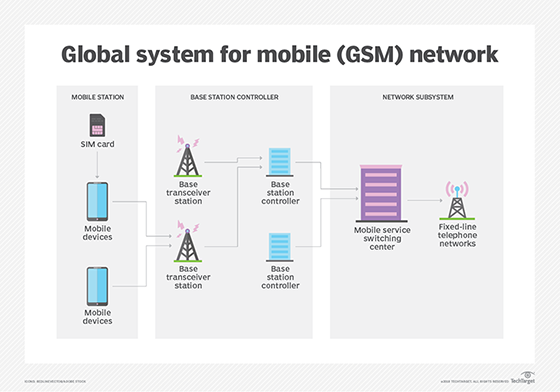
Cellphones require a network to operate. The carrier network licenses the radio spectrum used by the serviced phones and owns the radio equipment base stations and interconnections to transmit data.
The major cellular providers -- such as AT&T, T-Mobile and Verizon in the United States -- are both the service provider and the carrier network. They are responsible for owning the network equipment and radio spectrum, and they sell service directly to the consumer. These companies are known as mobile network operators, and they may be referred to as mobile service providers, wireless carriers, cellphone providers or wireless providers.
Other types of cell service providers do not own the equipment and only resell the service of a major provider. Because they do not own the equipment that handles data transmission, they are not considered a carrier network. Some examples of these types of providers in the United States include Boost Mobile, Mint Mobile and Tracfone. They use another company's network as the carrier network for their service and are referred to as a Mobile Virtual Network Operator (MVNO) or, simply, a service provider.
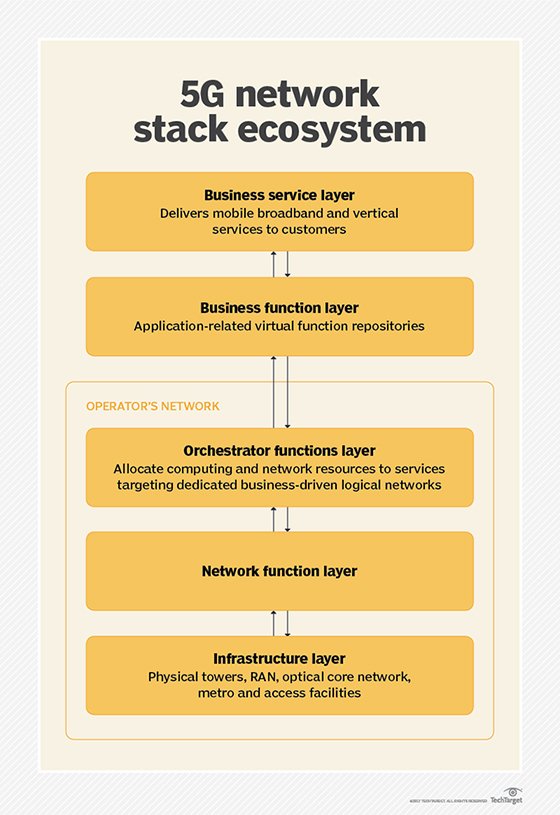
As mobile data use continues to increase, the strength of the underlying carrier network becomes more important. 5G-NR cellular technology, the latest performance standard, provides faster speed to cellphones and wireless broadband modems than the existing LTE network 4G wireless communications standard. Additional wireless spectrum and faster backbone connections to the wireless base stations are required to support this increase. If cellular networks do not increase capacity to meet increasing demand, slow connections and network congestion will result.
Data carrier networks
Data carrier networks form the backbone of the internet and are responsible for transmitting vast quantities of data. Most data served over the internet must traverse several of carrier networks to go from origin to requester. These carrier networks may charge a fee to transmit data to other networks, or they may have agreements to waive the fee for their preferred partners.
Networks come together at internet connection points or peer exchanges. These connections between peer networks use Border Gateway Protocol to control the flow of data traffic.
Carrier networks are generally divided into tiers denoting how much of the internet they can reach and their Peering agreements.
- Tier 1 networks can reach 100% of the internet with peering arrangements.
- Tier 2 networks will have some peering arrangements and are charged for using other networks to access some areas of the internet.
- Tier 3 networks are usually charged for access to all higher tiers, and they generally resell service to the end consumer as an ISP.
Underlying carrier networks employ various connection technologies. Fiber optic cable is the most common transmission method. This includes undersea fiber optic cables to connect continents. In total, one network may own hundreds of thousands of miles of fiber optic cable. Another connection technology, point-to-point microwave transmission, may be used in areas where carriers are not able to employ cables. Carrier networks may also use dedicated satellite networks.