business case
What is a business case?
A business case is a formal document or verbal value proposition that outlines the justification for commencing a project or undertaking a specific task. It offers reasoning for addressing a particular business problem or seizing an opportunity. While it's typically presented in a well-organized written format, it can also be communicated verbally or through a presentation. At its simplest, a business case could be a spoken suggestion.
Short-term actions leading to immediate, measurable and substantial business benefits are generally the easiest to argue. For example, if a restaurant's manager notices that the business doesn't make enough money on Sunday evenings to cover operational costs, presenting that fact to the owner might be compelling enough to make the business case for closing the restaurant at 5 p.m. on Sundays.
For more complex issues, a business case should be presented in a carefully constructed document that provides the reader with information about the risks and rewards involved in taking action and, conversely, not taking action. A well-crafted business case explores all feasible approaches to solving the problem so that responsible parties can select which option serves the organization best.
Why do companies need business cases?
A business case can be a crucial tool for project justification, resource allocation, project planning, communication, gaining support from senior management and evaluating the project's success.
The following are some common reasons why companies use business cases:
- Provides justification for decision-making. A business case justifies carrying out a project or effort. It summarizes the advantages and forecasts costs and risks associated with various selections. This helps the decision-makers determine the feasibility and potential worth of the proposed strategy. For instance, a business case can be used to justify the development of a new product by describing the market need, potential customer demand, competitive landscape and projected financial returns.
- Aids in resource allocation. By offering thorough insight into project costs and resource needs, a business case aids companies in effective resource allocation. Using this information, decision-makers can evaluate if the project is in line with the company's strategic business goals and priorities.
- Helps gain buy-in. A well-prepared business case is critical for getting support from senior management and key stakeholders. It helps convince decision-makers to accept and approve the project by offering clear justification, including the expected benefits, drawbacks and risk assessments. For example, a project team of a company considering a new customer relationship management (CRM) system could create a concise business case to present to senior management. By emphasizing the benefits -- such as how the CRM improves customer experience, including its value, rate of investment and alignment with business objectives -- the project team can gain support from senior management.
- Outlines project planning and scope. The business case is the foundation for project planning and outlining the breadth of work required to bring new projects and ideas to completion. It provides companies with a road map for project execution by identifying business objectives, timetables and milestones.
- Encourages effective communication and alignment. A good business case encourages effective communication and alignment among senior management teams and stakeholders, as it clearly articulates the project's objectives, advantages and risks. This ensures that all stakeholders are on the same page and understand the project's purpose and expected outcomes.
- Provides evaluation and accountability. After a project is finished, a business case provides a framework for assessing its outcomes. It helps hold project teams accountable for meeting the stated objectives and lets businesses evaluate if the project generated the anticipated value.
Key components of a business case
The key components of a business case can vary depending on the specific context and organization. However, standard components of a business case generally include the following:
- Executive summary. This is a high-level view that explains the problem that the proposed project is intended to solve in condensed form and plain language. An executive summary also highlights possible options, the desired outcome, resources required to achieve the desired outcome and the anticipated return on investment.
- The problem statement. The problem statement clearly identifies what issues the business needs to address. This guarantees that all parties involved have a common grasp of the main problem at hand.
- Analysis of the situation. This section provides more context, explaining how the problem came about and what the repercussions would be if no action was taken. The conclusion of the analysis should lead naturally to the next section.
- Options. In this section, the writer identifies potential options to solve the problem and provides sufficient detail for the readers.
- Cost-benefit analysis. This section evaluates the costs and benefits for each potential option, including the proposed approach to the problem and any alternatives -- which include, of course, taking no action at all.
- Recommendation. In this section, the business case writer makes a recommendation for how to address the issue described in the problem statement. It outlines the suggested plan of action in detail, taking into account the study and evaluation that were conducted.
- Project proposal. This provides the reader with details about how the recommended option will be carried out. It includes information about the project's scope as well as possible constraints and estimates for required resources, including personnel, time and budget.
How to create and execute a business case
Creating a business case is an essential step in project management. It offers a convincing case for moving forward with a project, highlights its benefits and helps justify its necessity. Although business cases are normally prepared during the project initiation phase, they're referenced throughout the project lifecycle.

The following are six steps to follow when writing a business case.
Step 1: Create an executive summary
Depending on the length of the business case, project members might consider including a high-level summary of the project. The executive summary serves as the first section of the business case and is typically written last. It provides a brief overview of the entire business case, succinctly conveying essential information about the project and communicating the complete story to the reader.
Step 2: Define the purpose
Before creating the business case, it's important to clearly state the purpose of the business case and the problem or opportunity it's going to address.
At this stage, the project team should answer the following questions:
- What problems or issues is the business case going to solve?
- What is required to tackle those issues?
- Will the project support the business strategy and how?
While this statement should be straightforward, it's best conveyed when backed up by data on the state of the economy and the level of market competitiveness.
Step 3: Evaluate alternate options
This step requires thorough research to gather the necessary information for the business case. It typically requires identifying all viable options available and researching their potential benefits.
To ensure that the project undertakes the most viable option, the following points should be addressed in the business case:
- All potential alternatives or options.
- The benefits of each potential option.
- The estimated costs associated with each option.
- The potential risks involved with each option.
Step 4: Recommend a preferred course of action
Now it's time to rank the preferred options by establishing criteria and using a scoring mechanism such as a decision matrix.
The following points can be used to create a recommendation:
- Assign a score between 1-10 to each shortlisted option based on its cost and benefit.
- Consider the priorities of the business while scoring.
- Introduce complexity to the ranking to ensure comprehensive coverage of key elements.
Regardless of the approach, once the numbers are added up, the most effective option for the business case will become evident. This process must be documented in the business case.
Step 5: Develop the execution strategy
Using the selected option, the project team should create an execution plan that outlines the required steps for accomplishing the project goals.
The execution plan should address the following points:
- The people who should be included in the project team.
- The resources required to execute the plan.
- The people who will be responsible for each milestone.
- How to reduce the project risks.
- A solid business case plan for monitoring and evaluating progress.
Step 6: Get approval from the stakeholders and decision-makers
This step entails getting approval from the board, the executive team and any outside stakeholders. This can be achieved by verifying the suggested course of action, creating the necessary documentation and submitting it for approval to the board.
This final piece of the document should answer the following questions so that the decision-makers can easily carry out the investment decisions:
- What are the benefits and drawbacks of the business case?
- How much does inaction cost?
- How much will it cost to invest in this business case?
The team members presenting the business case to the stakeholders should be strategic and persuasive and adhere to specified standards. Large organizations frequently specify standards for business case writers to assist them with creating what is known as an investment appraisal for their business case.
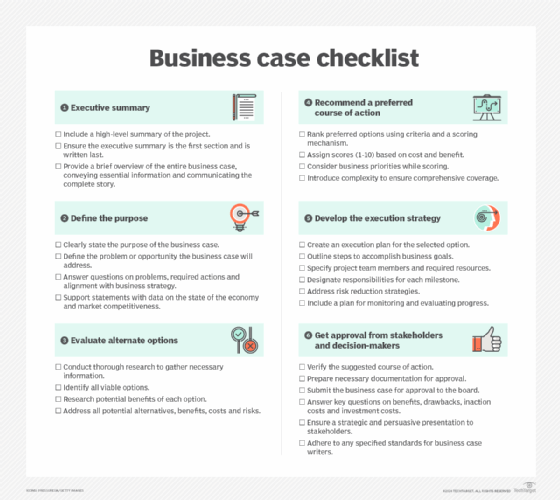
Business case checklist
A business case template or checklist can help business case writers to systematically develop a thorough and persuasive business case, covering key aspects from defining the purpose to obtaining approval from stakeholders.
Business case vs. business plan
The terms business case and business plan are sometimes used interchangeably, but they serve different purposes and scopes.
The following is a breakdown of the key differences between a business case and a business plan:
Business case
- A business case is an analysis of a potential market opportunity at the product level.
- It evaluates whether a business should try to create a product that will compete with others to remedy an issue in the market.
- It culminates in a go or no-go decision on pursuing the opportunity.
- Within an established business, a business case is commonly used for internal budget approvals and strategy prioritization.
- It can contain similar but condensed information as a business plan.
- The main areas of analysis in a business case include market opportunity, competition and possible risk factors.
Business plan
- A business plan is a detailed proposal for a new business or for making significant changes to an existing one.
- Stakeholders and investors are typically the intended audience of a business plan.
- A business plan includes a thorough description of the business, the people involved, supporting documentation, financial projections, market analysis, competitive analysis and other pertinent information.
- It provides an overview of the organization's objectives, plans of action and strategies for a given time frame -- typically one to three years.
- A business plan offers a road map for launching and expanding the business.
- It contains details about the business's cost structure, projected income and execution schedules.
Developing an effective business case for software initiatives is vital for securing support, justifying resource allocation and mitigating risk factors. Learn how to create a compelling business case for software projects.
