chatting
What is chatting?
While the term chatting or chitchat refers in general to communication between two or more parties that can occur in person, in today's modern age, it can also occur over the internet via Short Message Service (SMS) text message and Multimedia Messaging Service (MMS) or, for example, through tools like Slack and Microsoft Teams and social media platforms like Facebook and Twitter.
On the internet, the definition of chat refers to talking to other people who are using the internet at the same time you are.
Usually, this talking is the exchange of typed-in messages requiring one site as the repository for the messages -- or chat site -- and a group of users who take part from anywhere on the internet.

Different types of chatting
As explained above, modern chatting can occur in a variety of ways aside from direct, in-person contact. Let's explore those now.
Chat rooms
Chat rooms have been around since the early days of the internet. Back then, chat rooms were held on online services like AOL, which also offered instant messaging, a form of one-to-one private messaging between two users.
Users would connect to the service, choose a chat room from a list of available rooms, and then type in a screen name that would identify you to other users in the room.
These days, there are many different chat rooms available on the internet, including those focused on specific topics, interests or even just for chatting with friends.
Group chat situations like this can also be hosted by bulletin board forum services and by websites. Several websites exist solely for the purpose of conducting chats.
Communication/collaboration software
Additionally, communication platforms like Slack and Google Chat provide a chat session for remote or dispersed companies to facilitate team communication and collaboration in a work setting.
These tools enable real-time online chatting, as well as video and audio chatting, and share features like group chat rooms, file sharing and searchable history.
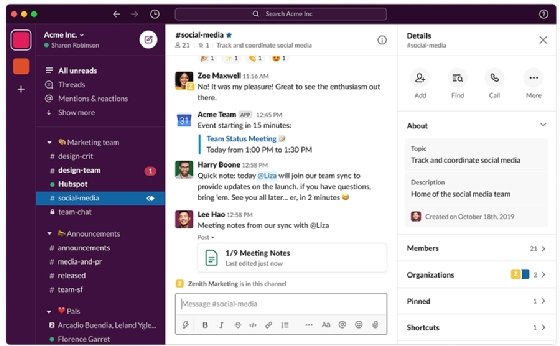
Chats can be ongoing or scheduled for a particular time and duration. Most chats are focused on a particular topic of interest or project, and some involve guest experts or famous people who talk to anyone joining the chat.
There are other platforms, such as Zoom, that facilitate voice chatting between two or more parties and offer the option to be on video during the call. This type of software is used mostly by businesses to replace in-person meetings.

Smartphone chat apps
Of course, chatting doesn't just happen on computers. With the advent of smartphones, there are now dozens of apps that enable users to chat with one another.
While chat software like Slack has mobile apps that can be installed on smartphones and mobile devices, these smart devices also typically come with chat software specifically for these mobile devices.
For example, WhatsApp is a chatting app that is available for both iPhone and Android devices. This app uses the internet to send text messages, images, video, user location and audio media messages from one smartphone to another.
It also enables voice and video calls between users. Another similar smartphone app is Facebook Messenger, which is used to chat with friends on the platform. Chatting can occur in a private window or within the Messenger app, but it also enables face-to-face conversions.
FaceTime is another chatting option that is available on Apple iOS devices. This app uses the device's front-facing camera to enable video chat between two people.
While it doesn't offer group chatting or other features, it's a quick and easy way to have a conversation with someone using an iPhone, iPad, iPod touch or Mac.

What are chatbots?
Chatbots are a little different from traditional chat rooms and chat software. These are computer programs with artificial intelligence (AI) that mimic human conversation. Users may even interact with a chatbot without even realizing it.
For example, when people visit a website and are asked by what appears to be a person on the other end of a chat window to provide their name, email address and other information in order to receive a newsletter or access to certain content, that's a chatbot in action.
Additionally, some companies use chatbots as customer service representatives. For example, users may chat with a chatbot on Facebook Messenger when inquiring about a product or service.
Typically, a chatbot starts as an AI-enabled interaction but eventually leads to transferring the human on the other end to the appropriate representative for further help.
Chatting can take many different forms in the modern age. It's a great way to communicate with others, whether they're right next to you or on the other side of the world, and has applications in both personal and professional environments.
For terms frequently used in online keyboard chatting, see chat acronyms IRC (Internet Relay Chat) and BBS (bulletin board system).
