
chief data officer (CDO)
What is a chief data officer (CDO)?
A chief data officer (CDO) in many organizations is a C-level executive whose position has evolved into a range of strategic data management responsibilities related to the business, including data governance, data quality and data strategy, to derive maximum value from the data available to the enterprise.
One of the relatively newer positions within an organization's leadership ranks, the CDO's responsibilities have expanded beyond liberating data silos and complying with various data protection and privacy regulations. In today's business climate encompassing digital transformation, advanced technologies and the pressures to gain valuable insights and monetize data collected from multiple sources, the CDO's role can entail data science, analytics, business processes, marketing initiatives, product development, supply chains, and customer and employee engagements.
Depending on the organization, the definition and responsibilities of a CDO, chief digital officer and chief analytics officer (CAO) can overlap, with boundary lines blurred among the three. The CDO often reports to the chief executive officer (CEO) but also frequently reports to chief operating officer (COO) or chief financial officer (CFO). Less frequently, the CDO reports to the chief technology officer (CTO) or chief information officer (CIO).
In many organizations, the chief data officer also works closely with the chief marketing officer (CMO) to use data to improve customer interactions, support customer experience and ultimately drive sales.
This article is part of
The evolving CIO role: From IT operator to business strategist
The CDO position is related to, but separate from, the job of the CIO. The CIO generally provides and supports the technology needed to collect, store and access the data, with the CDO working collaboratively with the CIO on the technologies to ensure support of the enterprise's objectives around data use, governance and monetization.
Researchers and management consultants believe that the most effective organizations assign clearly defined responsibilities for the CDO, CIO and other executive leadership positions that interact with and support the organization's data management programs.
History and evolution of the CDO position
Organizations have been gathering and compiling data as long as they've existed. But the volume of data started to grow exponentially with the rise of computer systems in the second half of the 20th century, as did the opportunities to analyze and monetize that growing body of data.
Initially, data processing managers and others within the IT department managed the data and data analysis, with the CIOs often having responsibility and oversight for the data programs within their enterprise.
However, the chief data officer position arose in the early years of the 21st century to take on the data management and oversight function. For example, Capital One appointed Cathryne Clay Doss as CDO, as well as senior vice president, in 2002, making her one of the first CDOs and widely recognized as an early leader in data executive ranks.
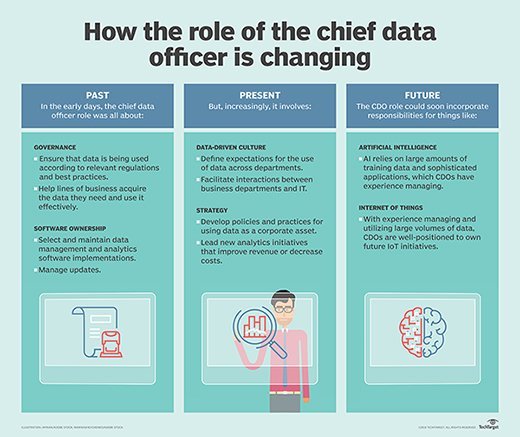
The CDO role has further evolved in response to increased compliance regulations after the great recession of 2007. At that time, a large part of the CDO's job typically entailed helping an enterprise create data governance policies that would ultimately reduce the organization's compliance burden. The focus of the position has since shifted to helping organizations understand that big data is a business asset that can be used strategically to identify new revenue opportunities and reduce operating costs.
As more organizations digitally transform and move to a data-driven decision management (DDDM) strategy, the CDO must ensure that business users have easy access to relevant data and reporting tools and can trust the data's quality. To that end, the International Society of Chief Data Officers (isCDO), a vendor-neutral peer-advisory resource affiliated with the Massachusetts Institute of Technology, helps members "strive to enable their enterprises to derive the maximum value from its information and data assets, to realize the value of data-driven decision-making and to gain competitive advantage through high-quality information."
Role of the chief data officer
The CDO has senior-most responsibility for the organization's strategic use of data, so the enterprise can perform more efficiently, boost productivity, better engage with customers, employees and other stakeholders, improve existing revenue streams and create new ones, and develop new business opportunities.
The CDO is expected to perform these tasks by using various tools and technologies, including AI, machine learning, the cloud, IoT, advanced analytics and business intelligence software. An equally important aspect of the CDO role is building a team of data professionals who understand the organization's culture, objectives and industry, so that they can apply data analysis to address concerns, challenges, risks and opportunities.
Additionally, the CDO is responsible for establishing and maintaining the organization's data governance policy and procedures, ensuring lifecycle data quality and management. These tasks require the CDO to work cooperatively with C-suite executives. The CDO is also expected to work closely with executive colleagues whose responsibilities also involve data -- for example, working with the chief information security officer (CISO) charged with ensuring data security within the organization or collaborating with the legal, compliance and risk leaders to ensure the organization's data policies comply with applicable rules and regulations.
Key CDO areas of responsibility within an organization
The chief data officer's responsibilities have expanded significantly as data management takes on greater importance for organizations that are in the throes of digital transformation and rely on business intelligence to continue competing at a high level. Following are some of the data-related areas that can come under the purview of today's CDO and affect virtually every aspect of an enterprise, including customers, employees and third-party stakeholders.
- overseeing the management and flow of data throughout its lifecycle;
- managing data governance strategies, practices and requirements;
- organizing, storing and analyzing strategic, operational and production data;
- establishing corporate practices that comply with data protection and privacy regulations;
- designing, developing and maintaining data warehouses and other repositories;
- ensuring business intelligence systems meet organizational requirements;
- implementing data analytics effectively into business processes;
- prioritizing data quality initiatives that ensure accurate business outcomes;
- establishing mechanisms that ensure the trustworthiness of data;
- improving user access to data while ensuring data protection and privacy;
- promoting data democratization, data literacy and a DataOps culture companywide;
- liberating siloed data that hinders intradepartmental business initiatives;
- monetizing data collected from multiple sources by using advanced technologies; and
- supporting the development and marketing of new products and services.
Why do organizations need a chief data officer?
Gartner defines today's CDO as a "senior executive who bears responsibility for the firm's enterprise-wide data and information strategy, governance, control, policy development and effective exploitation … to create business value."
The daily amount of data generated by society is estimated at about 2.5 quintillion (million trillion) bytes worldwide and growing. Organizations of all kinds realize they can use business intelligence and analytics tools to mine structured and unstructured data for insights into their business, industry and customers as well as market dynamics and consumer buying patterns.
Leading executives understand that data-driven insights can be monetized to improve their organization's performance by streamlining business operations, increasing productivity, managing the new reality of remote and hybrid workforces, improving customer experiences and developing new products and services.
More recently, enterprise leaders have come to see data and the ability to mine it for insights and intelligence as critical to driving digital transformation and competing in the digital marketplace.
Digitally savvy enterprises see data as an indispensable asset that requires the management and expertise of a senior-level executive who's responsible for setting data strategy companywide.
Chief data officer vs. chief analytics officer
Like the CDO and chief digital officer roles, there often is a blurring of lines between the responsibilities of the CDO and chief analytics officer. In fact, some research firms will often provide statistics related to the chief data/analytics officer.
Basically, the CDO's core responsibilities are the management, flow and strategy of data throughout its lifecycle to meet the company's business and financial objectives, while the CAO's core responsibilities focus on the analysis of that data to meet the business, operational and customer analytics needs of the organization. Depending on the company's size and industry, those roles can command separate titles or be combined into one title.
The CDO is expected to collaborate with other executives on data-driven initiatives and the analysis of data. In some organizations, data analysis is the responsibility of the chief analytics officer, along with other tasks similar to the CDO, including data strategy, treating data as an asset and deriving value from data. The CAO often reports to the CEO, but the position sometimes reports to the CDO. However, many organizations may not have a CAO or lack both a CDO and CAO.
Salary of the CDO
The average compensation of a chief data officer in the U.S. can vary widely, depending on the responsibilities associated with the CDO's diverse, expanding and evolving role. ZipRecruiter lists a CDO's average annual salary in the U.S. at about $177,000, with a range between $93,500 and $256,000, while salary.com pegs the average annual salary higher at $233,000, with a tighter range between $204,000 and $282,000, and Glassdoor reports the average annual base salary lower at $146,000, but with an additional $25,000 in bonuses, commissions or other compensation.
Career path and tenure info
Research shows that CDOs come from a variety of prior positions within the enterprise, many with data-centric roles that involve business intelligence and analytics. Many have also been promoted to chief data officer after working in IT-related jobs, marketing positions and even finance posts. Today's CDO in data-driven companies typically possesses a master's degree in technology or MBA, managerial or supervisory experience, and expertise in data collection, management, analysis and perhaps data science.
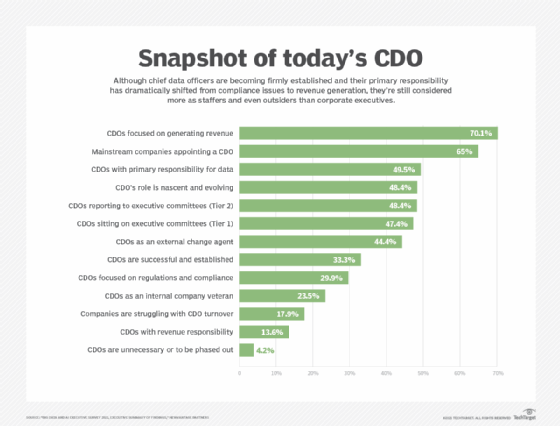
NewVantage Partners' "Big Data and AI Executive Survey 2021" that included primarily CDOs, as well as CAOs and CIOs, at Fortune 1000 companies and other leading firms provides insight into the evolving role of CDOs in driving digital transformation and the challenges confronting enterprises. Over the past decade, the percentage of mainstream companies adopting the CDO role has increased more than five-fold, from just 12% to 65%. However, the CDO's role doesn't necessarily dictate internal C-level status. About 44% of companies appoint an external change agent to handle CDO responsibilities compared to 23% that rely on company insiders, and only one-third of companies acknowledge that the CDO role is successful and established. While nearly half of respondents consider the CDO role "nascent and evolving," 18% of companies struggle with CDO turnover, although that number decreased from the previous year.
The average tenure for CDOs is considered less than three years. A combination of unclear corporate priorities, unrealistic corporate expectations and organizational resistance to newer technologies, plus a CDO's lack of executive experience, difficulty undertaking cultural change, and struggle to demonstrate value and achievements to business audiences, are said to contribute to high CDO turnover.
"Expectations of the chief data officer continue to evolve," the NewVantage survey noted, "with the pendulum shifting between the desire for an external change agent who will bring an outside perspective to the company and drive business change, in contrast with the internal company veteran who knows the organization well, understands the business culture and knows how to get things done."
Future of the chief data officer role
While considered a relatively new position and still evolving in corporations and government, CDOs are increasingly being recognized as integral to data-driven companies that are monetizing their collected data to improve business operations, product development, manufacturing, marketing campaigns, employee engagements and customer experiences. But there's a long way to go.
Many companies are in various stages of digitally transforming or have yet to embark on the journey. One-fourth of organizations reported being at the maturity level of implementing and optimizing several digital transformation initiatives, while nearly three-fourths are in process, just beginning or only planning to digitally transform, according to Enterprise Strategy Group (ESG), a division of TechTarget.
As more organizations accelerate their digital transformation initiatives to continue competing at a high level, the evolving role and title of the CDO should achieve greater clarity, importance and C-level acceptance beyond the core responsibilities of creating a data usage strategy, managing the flow of data, liberating data silos and ensuring compliance with regulations. Future CDOs will ideally possess a combination of data management, AI and analytics skills, executive experience and the ability to measure value in business terms.







