hard disk drive (HDD)
What is a hard disk drive?
A computer hard disk drive (HDD) is a non-volatile data storage device. Non-volatile refers to storage devices that maintain stored data when turned off. All computers need a storage device, and HDDs are just one example of a type of storage device.
HDDs are usually installed inside desktop computers, mobile devices, consumer electronics and enterprise storage arrays in data centers. They can store operating systems, software programs and other files using magnetic disks.
More specifically, hard disk drives control the reading and writing of the hard disk that provides data storage. HDDs are used either as the primary or secondary storage device in a computer. They are commonly found in the drive bay and are connected to the motherboard via an Advanced Technology Attachment (ATA), Serial ATA, parallel ATA or Small Computer System Interface (SCSI) cable, among other formats. The HDD is also connected to a power supply unit and can keep stored data while powered down.
A hard disk drive -- often shortened to hard drive -- and hard disk are not the same things, but they are packaged as a unit and either term can refer to the whole unit.
Why do computers need hard disks?
Storage devices like hard disks are needed to install operating systems, programs and additional storage devices, and to save documents. Without devices like HDDs that can retain data after they have been turned off, computer users would not be able to store programs or save files or documents to their computers. This is why every computer needs at least one storage device to permanently hold data as long as it is needed.
How do hard disk drives work?
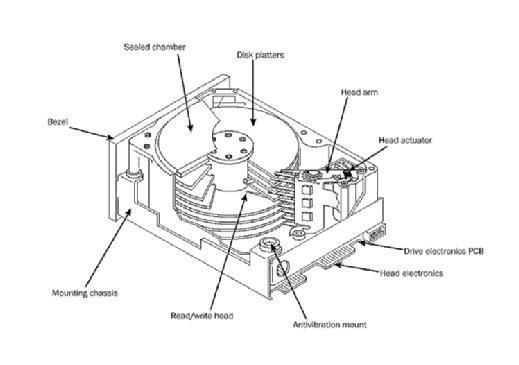
Most basic hard drives consist of several disk platters -- a circular disk made of either aluminum, glass or ceramic -- that are positioned around a spindle inside a sealed chamber. The platter spins with a motor that is connected to the spindle. The chamber also includes the read/write heads that magnetically record information to and from tracks on the platters using a magnetic head. The disks also have a thin magnetic coating on them.
The motor spins the platters at up to 15,000 rotations per minute. As the platters spin, a second motor controls the position of the read and write heads that magnetically record and read information on each platter.
Hard disk drive storage capacity
Some of the most common storage drive capacities include the following:
- 16 GB, 32 GB and 64 GB. This range is among the lowest for HDD storage space and is typically found in older and smaller devices.
- 120 GB and 256 GB. This range is generally considered an entry point for HDD devices such as laptops or computers.
- 500 GB, 1 TB and 2 TB. Around 500 GB and above of HDD storage is typically considered decent for an average user. Users can most likely store all their music, photos, videos and other files with this much space. Individuals with games that take up a lot of space should find 1 TB to 2 TB of HDD space suitable.
- More than 2 TB. Anything over 2 TB of HDD space is suitable for users who work with high-resolution files, who need to store or house a large amount of data, or who want to use that space for backup and redundancy.
Currently, the highest capacity HDD is 20 TB. However, an HDD actually has less space than advertised, as the operating system, file system structures and some data redundancy procedures use a portion of that space.
Hard drive components and form factors
Hard disk drive components include the spindle, disk platter, actuator, actuator arm and read/write head. Even though the term can refer to the unit as a whole, the term hard disk is the set of stacked disks -- in other words, the part of the HDD that stores and provides access to data on an electromagnetically charged surface.
The HDD form factor refers to the physical size or geometry of the data storage device. HDD form factors follow a set of industry standards that govern their length, width and height, as well as the position and orientation of the host interface connector. Having an industry-standard form factor helps determine a common compatibility with different computing devices.
The most common form factors for HDDs in enterprise systems are 2.5-inch and 3.5-inch -- also known as small form factor (SFF) and large form factor (LFF). The 2.5-inch and 3.5-inch measurements represent the approximate diameter of the platter within the drive enclosures.
While there are other form factors, by 2009, manufacturers discontinued the development of products with 1.3-inch, 1-inch and 0.85-inch form factors. The falling price of flash made these other form factors almost obsolete. It is also important to note that while nominal sizes are in inches, actual dimensions are specified in millimeters.
Many solid-state drives (SSDs) are also designed for the HDD form factor. SSDs that fit into the same slots as HDDs generally use the SATA or serial-attached SCSI (SAS) interface to transfer data to and from the host computing system.
What are external HDDs?
Most HDDs are found internally in a computer and work as stated above. However, individuals can also purchase external hard drives. External hard drives can be used to expand the storage capacity of a computer or to act as a portable device to back up data. External drives connect to a computer or device through interfaces like USB 2.0, USB-C or with External SATA (eSATA). External hard drives may also have slower data transfer rates compared to internal HDDs.
The main advantage of an external hard drive, aside from being able to expand a device's storage space, includes being portable. Users can store data from multiple devices and physically bring that data with them wherever they go.
Common hard disk errors
Hard disks can fail for all sorts of reasons. However, failures generally fall into the following six broad categories.
- Electrical failure occurs when, for example, a power surge damages a hard disk's electronic circuitry, causing the read/write head or circuit board to fail. If a hard disk powers on but cannot read and write data or boot, it is likely that one or more of its components has suffered an electrical failure.
- Mechanical failure can be caused by wear and tear, as well as by a hard impact, like a hard drop. This may cause, among other things, the read/write drive head to hit a rotating platter, causing irreversible physical damage.
- Logical failure results when the hard disk's software is compromised or ceases to run properly. All sorts of data corruption can lead to a logical failure. This includes corrupted files, malware and viruses, improperly closing an application or shutting down a computer, human error or accidentally deleting files that are critical to hard disk functionality.
- Bad sector failure can occur when the magnetic media on a hard disk's rotating platter is misaligned, resulting in a specific area on the platter becoming inaccessible. Bad sectors are common and often limited when they occur. Over time, however, the number of bad sectors can increase, eventually leading to a system crash, inaccessible files or the hanging or lagging of the operation of a hard disk.
- Firmware failure happens when the software that performs the maintenance tasks on a drive and enables the hard disk to communicate with a computer becomes corrupted or stops working properly. This type of failure can lead to the disk freezing during bootup or the computer a hard disk is connected to not recognizing or misidentifying it.
- Multiple unknown failures that accumulate over time can also occur. For example, an electrical problem could lead to a mechanical failure, such as a read/write head crash. It might also lead to a logical failure, resulting in several bad sectors developing on the hard disk platters.
History of hard disk drives
The hard disk was created in 1953 by engineers at IBM who wanted to find a way to provide random access to high capacities of data at a low cost. The disk drives developed were the size of refrigerators, could store 3.75 MB of data and began shipping in 1956. Memorex, Seagate Technology and Western Digital were other early vendors of hard disk drive technology.
Hard disk drive form-factor size has continued to decrease as the technology evolves. By the mid-1980s, 3.5-inch and 2.5-inch form factors were introduced and became a standard in personal computers.
Hard disk drive density has increased since the technology was first developed. The first hard disk drives could store megabytes of data, while today their storage capacity is in the terabyte range. Hitachi Global Storage Technologies (HGST) -- now a Western Digital brand -- released the first 1 TB hard drives in 2007. In 2015, HGST announced the first 10 TB hard drive. And in 2021, Western Digital unveiled two 20 TB HDDs.
HDD evolution and technology developments
In 2013, Seagate Technology announced hard disk drives that use shingled magnetic recording (SMR) technology. SMR increases storage density in hard disk drives by layering the magnetic tracks on each disk, rather than placing them parallel to each other. It is referred to as shingled because the tracks overlap similar to shingles on a roof.
HGST announced the first helium-filled hard disk drive in 2012. Helium is less dense, cooler and lighter than air, consumes less power, increases drive density and improves performance compared to traditional hard disk drives. In 2016, Seagate announced its own 10 TB helium hard drive.
In 2021, drive manufacturer Western Digital unveiled two 20 TB HDDs -- the Ultrastar DC HC560 and WD Gold HDD Enterprise Class SATA HDD. Currently, 20 TB is the largest available HDD size. Both hard disk drives come in the standard 3.5-inch form factor but have different use cases. The Ultrastar DC HC560 is meant for cloud storage providers and for business servers, security systems and network-attached storage devices. The WD Gold HDD is designed for enterprise businesses that run heavy application workloads.
HDDs vs. SSDs
The main alternative to hard disk drives are solid-state drives.
Unlike hard disks, SSDs contain no moving parts. SSDs also have lower latency than HDDs, and therefore are often favored to store critical data that needs to be accessed quickly and for applications with a high input/output demand. SSDs are configured to deliver high read/write speeds for sequential and random data requests. Additionally, SSDs do not store data magnetically, so the read performance remains steady, regardless of where the data is stored on the drive. SSDs also have faster boot times.
It is because of these benefits, and that HDDs are more vulnerable to breakdowns, that HDDs are now starting to be replaced by SSDs.
However, even though most PC users have started to favor SSDs, HDDs -- along with magnetic tape -- are still used frequently to store large amounts of data. In part, this is because SSDs are more expensive than HDDs from a price-per-gigabyte standpoint. Many enterprise storage arrays ship with a mix of HDDs and SSDs to reduce costs while providing better performance. SSDs also have a set life expectancy, with a finite number of write cycles before performance slows. Compared to an HDD, SSDs fail faster.
Learn more about how SSDs compare to HDDs in this article.






