green computing
What is green computing?
Green computing, also known as green technology, is the use of computers and other computing devices and equipment in energy-efficient and eco-friendly ways. Organizations that use green computing methods often deploy energy-efficient central processing units (CPUs), servers, peripherals, power systems and other IT equipment. They also focus on reducing resource use and properly disposing of electronic waste.
In many organizations, green computing is a key part of environmental, social and governance (ESG) initiatives that focus on the adoption of sustainable and ethical business practices. It also contributes to broader business sustainability efforts, which aim to position companies for ongoing success based on responsible corporate management and strategies.
What is included in a green computing strategy?
Saving money on energy and IT costs is one driving factor for green computing approaches. Government regulations related to energy conservation also drive green efforts. Concern about climate change, combined with internal and external pressure to be environmentally responsible, is a third factor behind the green computing movement.
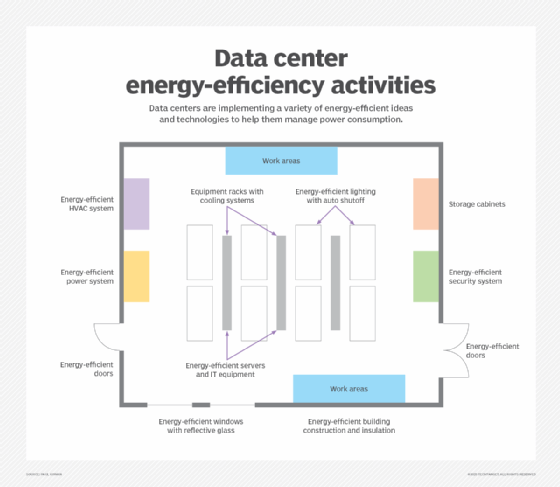
IT managers typically focus energy efficiency efforts on data centers, as well as separate equipment rooms and data storage areas that use significant amounts of energy or are affected by its use. For example, upgrading IT systems can help by replacing older equipment that often uses more energy and puts out more heat than newer technologies. In addition, hot and cold aisle setups group together data center assets based on energy consumption and temperature output, optimizing the efficiency of heating, ventilation and air conditioning (HVAC) systems.
The green computing strategies of companies can also include the following actions, both in and beyond the data center:
- Deployment of smart technology. Organizations can use internet of things sensors and artificial intelligence (AI) monitoring tools to collect and analyze information about data centers and create a power usage model. AI-powered tools can also autonomously manage heating, cooling and power in the data center.
- Powering down IT equipment when it isn't in use. Servers, CPUs and other devices can be turned off during extended periods of inactivity. In particular, energy-intensive peripherals, such as laser printers, should only be powered up when needed.
- Strategic scheduling of computer use. Do computer-related tasks in dedicated blocks of time, leaving hardware off at other times.
- Energy-efficient computer and display selection. Laptops use significantly less energy than desktop computers, and liquid-crystal display monitors use less energy and give off less heat than cathode-ray tube monitors.
- Automated power management. These features can be set to automatically power down hard drives and monitors after several minutes of inactivity.
- Temperature check for less cooling. Newer IT devices can safely run at higher temperatures than older ones, so the data center may not need to be as cool as in the past.
- Electronic waste disposal. Dispose of e-waste according to federal, state and local regulations.
- Alternative energy and cooling opportunities. Investigate alternative energy sources, such as wind and hydroelectric power, as well as geothermal cooling and other new methods of cooling data centers.
- Support for remote work. The COVID-19 pandemic has spurred many changes in the workplace, including an increase in remote and hybrid work that has led to reduced energy consumption. Besides decreasing the number of people commuting to and from work, it has also cut the number of employees typically present in an organization's facilities, reducing the demand for power and other resources needed to run computers there.
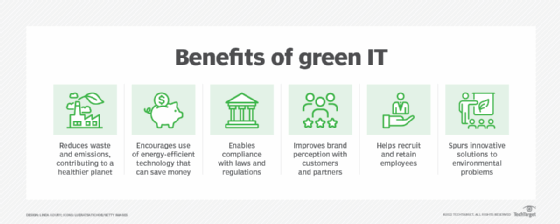
The importance of green computing
The key mission of green computing is to reduce energy consumption. This not only cuts energy costs for organizations, but it also reduces carbon footprints, particularly of IT assets. In addition to the cost savings, green approaches to computing can help organizations on regulatory compliance and potentially give them a marketing edge over competitors with both customers and investors.
The environmental impact of IT components is important to consider in the data center design process. Advances in energy management and energy conservation have made IT systems and other computing resources highly energy-efficient. Green design of data centers, office space and other facilities that consume high amounts of energy has become a key part of new construction and building upgrades to make them more environmentally sustainable.
That includes the use of energy-efficient HVAC, power and lighting systems, and a variety of ancillary equipment. For example, many data center components have a sleep mode that reduces power use or completely shuts down a system during times of low or no use. Also, most IT equipment vendors support green manufacturing practices. The U.S. government's Energy Star logo is an important metric when selecting IT equipment and data center elements.
Another important consideration with green computing and the related concept of green IT is their potential to reduce an organization's use of fossil fuels. This helps lower the amount of pollution released into the atmosphere and water sources -- such reduced emissions have been shown to have positive effects on weather, air pollution and water quality.
Green computing challenges
While green computing has many benefits, not every organization will embrace the changes needed to become truly green. Challenges that organizations can face on green computing initiatives include the following:
- Equipment replacement costs. Perhaps the biggest challenge is the cost of replacing existing technology assets with energy-efficient devices, such as ones that have the Energy Star certification. This can also extend to replacements of HVAC, power and lighting systems, as well as physical security systems. Upgrading IT assets, such as servers, networking equipment, storage devices, and primary and backup power systems, should be easy enough to do, but the cost must be examined carefully.
- Upgrades to leased space. Organizations that lease space in buildings where data centers are located can ask the building owner about plans to make it more energy-efficient -- for example, by adopting the U.S. Green Building Council's Leadership in Energy and Environmental Design (LEED) standards. But owners of older buildings are less likely to make such an upgrade, whereas newer buildings can more easily be designed or retrofitted to achieve LEED certification.
Even then, though, the cost to make such changes might be prohibitive -- or, if the changes are implemented, they could result in a rent increase. A company can also ask building management for permission to upgrade physical systems itself, but there might be a limit on how much upgrading is possible, as spelled out in the lease agreement. - Lack of green computing expertise. Another potential challenge is finding experts in green computing who can assist in the data center design process and upgrades of IT assets. For example, they could help plan a structured sequence of actions -- over, say, a one- or two-year period -- to replace existing devices with energy-efficient units. But such experts can be hard to find, despite an increase in the availability of consulting services for sustainability efforts.
For more on ESG strategy and management, read the following articles:
5 ways organizations can address the social factors of ESG
A timeline and history of ESG investing, rules and practices
ESG audit checklist: 6 steps for success
ESG materiality assessments: What CIOs, others need to know
ESG metrics: Tips and examples for measuring ESG performance
18 sustainability management software providers to consider
How to achieve green computing
The following is a list of ways to increase green computing and energy efficiency in data centers and other IT facilities:
- Install building environment systems that are energy-efficient.
- Install overhead lighting with low energy consumption, and include timers or motion detectors to control light switches and reduce the time lights are in use.
- Buy energy-efficient servers, switches, laptops, desktop systems, printers, scanners and other IT equipment.
- Install energy-efficient windows and doors that have reflective glass to reduce heat.
- Install fans throughout equipment racks to reduce heat.
- Turn off systems that aren't performing scheduled work.
- Use refillable printer cartridges.
IT leaders should also explain the importance of green data centers and other green computing measures to senior management and make sure to get their support for an initiative. Corporate policies that stress energy conservation and the use of energy-efficient equipment can then be established to formalize the efforts.
History of green computing
Data centers came into their own as major consumers of electricity in the late 1960s and early 1970s. With the advent of large processing systems, such as mainframes, as well as the many different peripheral devices associated with them, data centers grew in both size and energy usage.
At that time, data center managers thought little, if at all, about environmental concerns. Printers generated mountains of paper, much of which was discarded in dumpsters -- creating large amounts of trash and the potential for data security issues due to dumpster diving by attackers. Water was used to cool large mainframes, especially those made by IBM, which increased water usage by companies.
As the computing industry grew, IT vendors designed smaller and faster systems, but the notion of green technology didn't arise until 1992 when the U.S. Environmental Protection Agency (EPA) launched the Energy Star program to promote energy efficiency in computing hardware and various other types of products. Buying IT equipment with the Energy Star label meant that it would save electricity and have less of an environmental impact overall.
Now run jointly by the EPA and the U.S. Department of Energy, the voluntary program has been widely implemented by computer manufacturers and other device makers. The Energy Star label is common on IT equipment, especially for laptop computers and displays. Many European and Asian countries have also implemented similar programs.
The EPA later also funded the development of an environmental standard for computers and other electronic products, plus a tool for assessing compliance with the standard. In 2006, the agency issued a grant to what's now known as the Global Electronics Council (GEC) to create a registry of products that meet the criteria of the Electronic Product Environmental Assessment Tool (EPEAT) standard. The GEC continues to manage the EPEAT registry and "ecolabel," which now covers end-user computers and displays, mobile phones, servers, networking equipment, imaging devices and other non-IT products.
Organizations can use EPEAT to identify "environmentally preferable" technologies for purchases, according to the EPA. For example, the Federal Acquisition Regulation, which applies to all U.S. government agencies, mandates that 95% of the electronic products procured by them are listed on the EPEAT registry.
As the use of cloud services grew, cloud platform vendors built new data centers with more of an emphasis on energy efficiency, reduction of emissions and overall sustainability. The environmentally friendly capabilities of a green cloud approach can be another advantage of moving to the cloud, in addition to savings on equipment costs and data center space.
In recent years, additional standards have been developed that provide specifications and benchmarking metrics applicable to green computing. For example, the International Organization for Standardization, a global standards organization commonly known as ISO, has several families of standards that can be used in planning and managing green computing initiatives. That includes ISO 14000 for environmental management systems, ISO 50001 for energy management systems, the companion ISO 50002 for energy audits and ISO/IEC 33000, an IT process assessment standard developed by a joint technical committee set up by ISO and the International Electrotechnical Commission.
The potential benefits of green computing are well documented overall, and the current trend is for IT teams to continue deploying green computing technology wherever possible.
Find out more about green computing best practices and how to put them into practice.






