semiconductor
What is a semiconductor?
A semiconductor is a substance that has specific electrical properties that enable it to serve as a foundation for computers and other electronic devices. It is typically a solid chemical element or compound that conducts electricity under certain conditions but not others. This makes it an ideal medium to control electrical current and everyday electrical appliances.
A substance that can conduct electricity is called the conductor and a substance that cannot conduct electricity is known as the insulator. Semiconductors have properties that sit between the conductor and insulator. A diode, integrated circuit (IC) and transistor are all made from semiconductors.
The conductance can vary depending on the current or voltage applied to a control electrode or on the intensity of irradiation by infrared (IR), visible light, ultraviolet or X-rays. The specific properties of a semiconductor depend on the impurities -- known as dopants -- added to it.
How do semiconductors work?
Most semiconductors are composed of crystals made of several materials. To better understand how semiconductors work, users must understand atoms and how electrons organize themselves within the atom. Electrons arrange themselves in layers called shells inside an atom. The outermost shell in the atom is known as a valence shell.
The electrons in this valence shell are the ones that form bonds with neighboring atoms. Such bonds are called covalent bonds. Most conductors have just one electron in the valence shell. Semiconductors, on the other hand, typically have four electrons in their valence shell.
However, if atoms nearby are made of the same valence, electrons may bind with the valence electrons of other atoms. Whenever that happens, atoms organize themselves into crystal structures. We make most semiconductors with such crystals, mainly with silicon crystals.
What is the difference between N-type and P-type semiconductors?
An N-type semiconductor carries current mainly in the form of negatively charged electrons similar to the conduction of current in a wire. A P-type semiconductor carries current predominantly as electron deficiencies called holes. A hole has a positive electric charge, equal and opposite to the charge on an electron. In a semiconductor material, the flow of holes occurs in a direction opposite to the flow of electrons.
Elemental semiconductors include antimony, arsenic, boron, carbon, germanium, selenium, silicon, sulfur and tellurium. Silicon is the best known of these, forming the basis of most ICs.
Common semiconductor compounds include gallium arsenide, indium antimonide and the oxides of most metals. We also widely use gallium arsenide (GaAs) in low-noise, high-gain, weak-signal amplifying devices.
A semiconductor device can perform the function of the original vacuum tube, but with hundreds of times its volume. Like a microprocessor chip, a single IC can do the work of a set of vacuum tubes that would fill a large building and require its own electricity generating plant.
What is a semiconductor chip?
A semiconductor substance lies between the conductor and insulator. It controls and manages the flow of electric current in electronic equipment and devices. As a result, it is a popular component of electronic chips made for computing components and a variety of electronic devices, including solid-state storage.
What is an RF semiconductor?
A radio frequency (RF) semiconductor is a device used to switch on or rectify power in electronic devices. RF semiconductors work in a radio frequency spectrum of about 3KHz up to 300GHz.
What is a semiconductor optical amplifier?
A semiconductor optical amplifier (SOA) is an element found in semiconductors that amplifies light. Users can find SOAs in optical transceiver modules used to enable communication between data centers.
In this scenario, the SOA amplifies the optical signal used for Ethernet communication. This approach helps compensate for transmission loss.
What is the difference between an intrinsic and extrinsic semiconductor?
The primary difference between intrinsic and extrinsic semiconductors is their form. For example, intrinsic semiconductors are pure in form and composed of only one kind of material. They do not have any form of impurity added to them.
In contrast, extrinsic semiconductors are impure. Extrinsic semiconductors comprise multiple intrinsic semiconductors with other substances added to change their properties. These substances are typically doping trivalent or pentavalent impurities.
What is a fable semiconductor?
The term fable -- not to be confused with semiconductor fab -- describes companies that design, manufacture and sell hardware and semiconductor chips but don't build their own silicon wafers or chips. Instead, they outsource the fabrication to a foundry or another manufacturing plant.
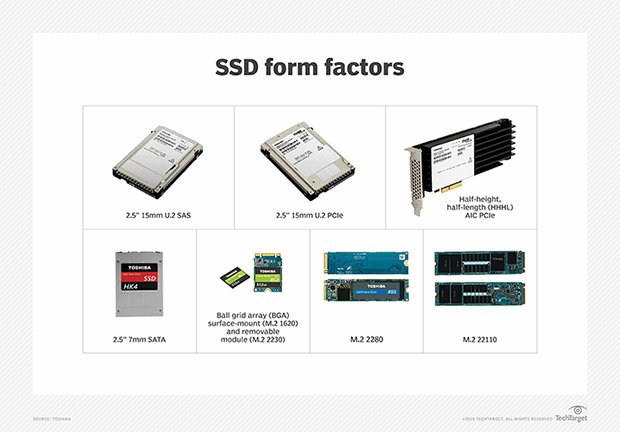
Two common types of solid-state memory (built on semiconductor materials) are NOR and NAND flash, as shown in the video above.
See also bipolar transistor and field-effect transistor. Explore this guide on flash memory architecture, types and products.
