clock speed
What is clock speed?
Clock speed is the number of times a second that a circuit operates and is most associated with the central processing unit (CPU). It is measured in hertz, or cycles per second. The higher the clock speed, the more processing power -- all other things being equal. Clock speed is also known as clock rate, core clock or clock frequency.
Complex circuits require careful timing to operate properly. The clock is a regular pulse to keep the whole circuit working in sync. The clock is like the caller in a team rowboat yelling out when to pull. The faster the caller instructs the rowers to pull, the more work gets done.
The clock is a regular on-off electrical pulse. Each time the pulse goes from on to off then back to on again is one cycle. Every cycle, the circuit can perform one operation. Although clock speed is measured in hertz, modern processors operate in the gigahertz range, or billions of operations per second.
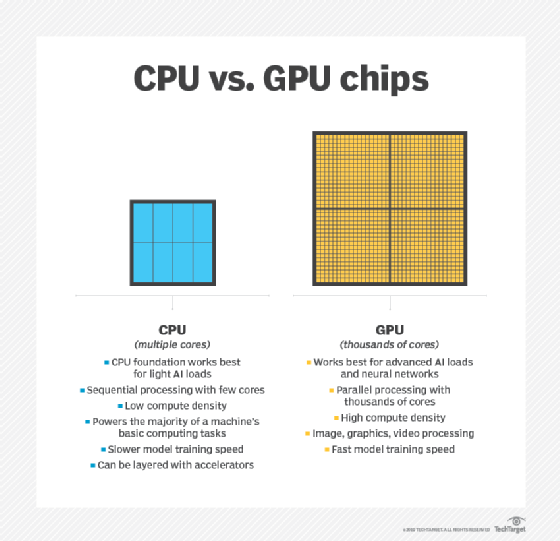
While clock speed is commonly referred to with computer CPUs, other components that use integrated circuits (ICs) also have a clock to synchronize operations. A discrete graphics processing unit may have its own clock speed that it generates and uses, and a computer's RAM may be synchronized to the system CPU clock.
There are different ways that circuit manufacturers can generate the clock pulse. Historically, oscillating quartz crystals have been used to generate accurately timed clock pulses, and other circuitry could then multiply that frequency to the needed speed. In modern high-speed CPUs, a reference pulse is generated by an oscillating circuit. This can be used to set a front-side bus speed. An additional multiplier is then applied to the bus clock to generate the CPU core clock.
There are many variables besides clock speed that can affect the performance of a CPU. Therefore, the clock speed can only be directly compared in the same generation and family of processors.
Dynamic frequency scaling
Modern ICs can dynamically change their clock speed to match processing demands. Instead of always running at the processor's maximum speed, they instead drop down to a lower frequency. Running at a lower speed uses less power and produces less heat. This is desirable in mobile devices to increase the battery life. It also benefits desktop processors as they can potentially overheat when running at full speed for extended periods of time. Intel SpeedStep is an example technology.
Newer processors can also selectively increase their clock speed for high-performance or small-burst workloads. This enables the processor to work at a higher frequency for a short time until it generates too much heat and then needs to slow down again. In older systems, all the CPU cores would need to run at the same boost speed. In new multicore processors, the speed of each core can be controlled individually, enabling greater granularity in boost performance. Intel Turbo Boost is an example technology.
What is overclocking?
Overclocking is running an IC at a higher clock speed than the manufacturer-specified speed. Overclocking causes the processor to produce extra heat and requires more power. The extra heat may require water cooling components. If pushed too far, an overclocked system becomes unstable and may crash, causing blue screens or system hangs. Some processors can sustain higher overclock speeds than others, even within the same processor model. This is known as binning or the silicon lottery.
Most AMD processors can be lightly overclocked by the end user. Only Enthusiast model (K series) Intel CPUs can be overclocked. Intel Extreme Tuning Utility can be used to overclock these chips.
Illustrating clock speed
If a computer is like a car, then the CPU is the engine of the car; it's where the work gets done. The CPU clock speed is like the engine's revolutions per minute (RPM). Generally, you wouldn't say that, just because an engine has a higher maximum RPM, it makes more power; similarly, you need to consider more factors than just clock speed to determine how much performance you can get from a CPU.
The engine's RPM goes up and down depending on how much power is needed. This saves on gas and makes less heat than running at full throttle all the time. This is like the CPU varying its clock speed to use less power and produce less heat.
Some enthusiasts modify their engine or use premium fuel or additives to run it at an extremely high RPM, past the red zone. This risks damaging the engine. This is like overclocking a CPU.
Learn how CPU, GPU and data processing units differ from one another, and see features to keep in mind when buying server hardware.
