codebase (code base)
What is a codebase (code base)?
A codebase, or code base, is the complete body of source code for a software program, component or system. It includes all the source files needed to compile the software into machine code, including configuration files. The source code is typically written in a human-readable language such as Java, C#, Python, JavaScript, Extensible Markup Language or plain text. The codebase also often includes files to help understand, deploy or use the application. For example, the codebase might contain readme files, example scripts, licensing details or other explanatory information.
How is the final software product compiled?
The final software product is compiled from the source code in the codebase and, if needed, the accompanying configuration files. The process starts with developers writing code and saving it to files, which are organized into folders and subfolders based on the project's requirements. After the code has been created, it is compiled for a specific operating system and computer architecture, such as Windows on Arm architecture or Linux on x86 architecture.
When it's time to build the application, developers feed the source code into a compiler. The compiler interprets that source code and outputs assembly code. The assembly code is submitted to an assembler, where it is transformed into object code. A linker uses the object code, along with other files, to create an executable that a processor can understand -- but a human cannot, without a great deal of difficulty.
After the source code has been compiled, the development team retains the code, either as a collection of files or in a source control repository. If the software needs to be updated, the source code is modified and recompiled -- a process that continues throughout the software's supported lifecycle.
The screenshot below shows part of the codebase for Pytest, an Open Source testing framework for running functional tests against applications and libraries. Developers have uploaded the codebase to a public GitHub repository, which includes the program's source code, written in Python, and supporting files. The main branch is active, but a developer can access the files from any of the other available branches.
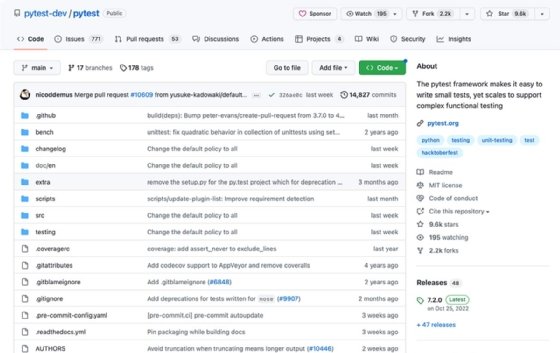
The Pytest repository currently includes 618 files, spread out across multiple folders and their subfolders. This is relatively small compared with many development projects. For example, Google's primary codebase is said to include around 1 billion files.
How are codebases categorized?
Codebases are generally categorized as one of two types:
- Monolithic. The entire codebase is maintained in a single repository that contains all software components and is shared by all developers working on the project. A monolithic codebase ensures one source of truth, minimizes dependency issues, supports atomic changes and simplifies large-scale refactoring. However, a monolithic codebase can grow quite large and become unwieldy as it evolves, making it more difficult to work with and maintain.
- Distributed. A distributed codebase is divided into smaller repositories based on the individual components that comprise the software. The repositories are easier to maintain than a single monolithic codebase, and code changes are easier to deploy, but this also makes it more difficult to manage dependencies and implement changes across multiple components.
How is a codebase managed?
A codebase must be carefully managed when building the program to ensure the software will successfully compile. Developers, especially those new to a project, should be able to easily understand and work with the source code and its supporting files. The quality of the programming, adherence to best practices and adequate commenting can make the codebase much easier to understand and maintain. Many development teams include code reviews to monitor adherence to coding best practices.
Whether codebases are monolithic or distributed, most development teams maintain their source code in a version control system. Such a system lets developers save and retrieve different versions of source code, as well as share control of different versions. The system maintains a single copy of the codebase and a record of any changes. When a specific version is requested, the system reconstructs it from that information.
A version control system also enables development teams to branch and merge source code, making it easier to work concurrently on a large development project, including those that span multiple live product versions. In addition, version control systems can play a key role in continuous integration/continuous delivery (CI/CD).
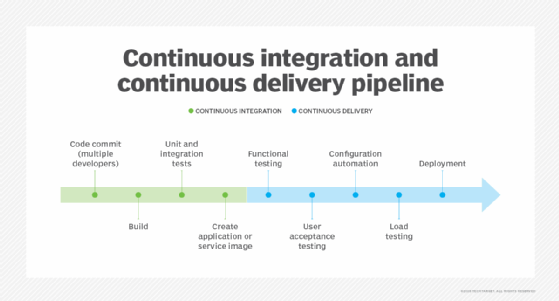
When a developer checks code into the repository, the CI engine automatically launches a build and testing process that verifies code changes. If the code does not pass the tests, the changes can be rolled back; otherwise, the changes are integrated into the product.
Get to know the version control process, see how to build a CI/CD pipeline with Azure and GitHub and check out coding books to read this year.
