colocation (colo)
What is colocation (colo)?
A colocation facility (colo) is a data center or telecommunications facility in which a business can rent space for servers, storage devices and other computing and networking hardware.
Typically, a colo provides the building, cooling, power supply, voice and data network bandwidth, internet access and physical security, while the customer provides servers, storage and network devices. It can support all or part of an IT infrastructure, ensuring that customer business needs are addressed.
Space in a colo facility is typically leased by the rack, cabinet, cage or room. Many colos have extended their offerings to include managed services that support their customers' business initiatives. These include internet access, wide area network services, metropolitan area network services, change management, security management and disaster recovery (DR).
Who needs a colocation facility?
Organizations of virtually any size can use a colo facility to provide primary IT operations and carrier-neutral network services. They also use them to augment an existing IT infrastructure on a temporary basis or for a longer term as business needs dictate.
There are several reasons a business might choose a data center colocation over building its own on-premises data center. One key driver is the capital expenditure associated with building, maintaining and updating a large computing and networking facility. In the past, colos were often used by private enterprises for DR. Today, colos are especially popular with cloud service providers to quickly expand their resources without major capital outlays.
For some organizations, colocation might be an ideal solution, but there can be downsides to this approach. Distance can translate into increased travel costs when equipment must be manually handled, and colo customers can find themselves locked into long-term contracts that prevent them from renegotiating rates when prices fall.
Colocation features
Colocation providers typically have their own rules and procedures, so features and support capabilities may vary from one company to another. Due diligence by prospective customers is essential before contracting with a colo.
Features that colocation data centers commonly provide include the following:
- Physical building.
- Physical security, such as biometric scanners.
- Heating ventilation and air conditioning resources, such as a dedicated cooling system.
- Guaranteed reliability.
- Cross-connectivity.
- Redundant internet connectivity.
- Redundant local telephone company access.
- Inventory of networking equipment.
- Redundant power from contracting with multiple power suppliers and having backup generators.
- Compliance with various regulations.
- On-site technical support.
Colocation facilities are often multifloor buildings. The various floors provide flexible space with a variety of configurable enclosures and equipment racks for customers to house their servers and other devices. These facilities also might have food service canteens, workspace for customers and conference rooms.
The location of a colocation building is an important consideration. If the building is in a neighborhood that has a history of crime, there may be increased security risks. Buildings located near busy highways or within airport flight paths might be at risk for vehicular or aircraft damage. Buildings located near bodies of water that have a history of flooding could also be at risk.
Advantages of colocation
Businesses taking advantage of colocation services can benefit in the following ways:
- Leasing space in a colocation facility is less expensive than building or expanding a data center.
- Colocation facilities allow tenants to use computing hardware of their own choosing.
- A colocation data center facility adheres to strict physical security protocols and might also offer protection against cyberattacks.
- Colocation facilities almost always provide on-site technical support services.
- Additional data center space is usually available if needed, which means that a colocation data center can provide the scalability needed to accommodate growth.
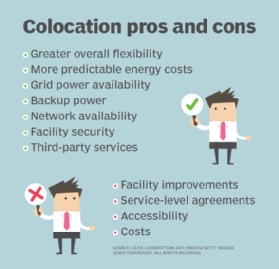
Disadvantages of colocation
Colocation facilities must be carefully evaluated before executing any contracts or making a move. Some potential issues to be aware of are the following:
- Fee structures that have leeway for unexpected changes.
- Restrictions on customer access to their equipment.
- Questionable service-level agreement (SLA) policies.
- Security issues that could lead to building breaches or unauthorized access to customer space and equipment.
- Inability to quickly accommodate floor space and equipment expansion requirements.
- Poor technical support and assistance.
Colocation buildings and facilities
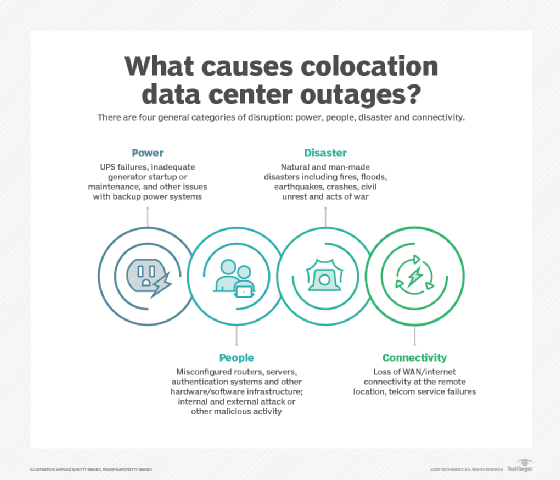
Just as there are differences between office buildings, there are also differences between data centers. Some of these differences are related to the way that the data center was constructed, while others have more to do with the data center's operational efficiency.
Typically, a colocation data center provides its tenants with an SLA guaranteeing a specific amount of availability. It's essential for organizations to scrutinize the colo's SLA so they aren't surprised by hidden charges. SLAs are especially important when responding to a disruptive event affecting the colo center, such as a commercial power outage or a physical security breach. Customers must ensure the colo can support their recovery time objectives if an outage or other issue occurs.
As part of the SLA, a data center might guarantee a specific amount of uptime, such as five nines of uptime. However, data center uptime is more commonly expressed in terms of the following four tiers:
- Tier 1. Nonredundant power, cooling and network connectivity.
- Tier 2. At least some redundancy for power and cooling.
- Tier 3. Able to withstand a 72-hour power outage.
- Tier 4. Able to withstand a 96-hour power outage.
Data centers commonly express their efficiency through a score known as their power usage effectiveness (PUE). This score reflects how efficiently the data center uses power. Data centers with good PUE scores are friendlier to the environment and, generally, charge their tenants lower rates for power consumption.
It's also important to consider how a data center was constructed. Every location in the world is susceptible to at least one type of natural disaster, so it's necessary to make sure that a colocation provider's data center was constructed in a way that helps it survive such a disaster. For example, data centers in hurricane-prone areas are often rated to withstand 150 mph winds.
Colocation security
Just as security is of paramount importance to cloud providers, good security is also essential to colocation providers. Colocation providers go to great lengths to ensure the physical security of their data centers.
Some colocation providers erect fences or cages in the data center as a way of isolating each tenant's hardware. These fences have locking gates, so tenants are only able to access their own data center hardware. Colo facilities also usually require tenants to pass through multiple security checkpoints prior to being able to access data center hardware.
Some colocation providers might limit or restrict tenant access to the facility. In that case, hardware maintenance and installation are typically performed by the colo center staff through a process known as remote hands.
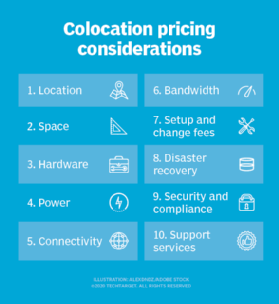
Colocation pricing
Each colocation provider has its own pricing model. For instance, some bill their tenants based on the amount of rack space that they consume. Other providers lease data center floor space by the square foot.
The pricing model isn't the only factor that determines the overall cost of leasing space in a colocation facility. Some of the other factors that can influence the total cost are bandwidth use, power consumption, power distribution units required, geographic location, technical support incidents and the support contract.
Colocation vs. public cloud
There are major differences between a colocation data center and a public cloud provider, even though both enable businesses to run workloads in a remote data center.
Colocation data centers
These facilities provide businesses with physical data center space. They provide power, cooling and network connectivity, but the tenants provide their own hardware, such as servers, storage and supporting infrastructure. Colocation facilities are geared toward organizations that want to run workloads on their own servers and other hardware but in a remote data center.
Cloud providers
Cloud platform providers use their own hardware and typically support public cloud, multi-cloud and hybrid cloud computing configurations. Tenants run workloads on the cloud provider's hardware, which is in a cloud data center that can be physically located anywhere. The cloud provider then bills the tenant for the compute, storage, network and other resources that their workloads have consumed.
Public clouds are the preferred option for organizations that want consumption-based pricing and prefer not to have to buy or maintain server hardware in-house.
Colocation vendors
There are numerous colocation hosting providers in the United States and around the world. Some of these vendors are small boutique vendors that operate only one or two data centers. Others are massive, multinational providers with dozens -- or even hundreds -- of data centers and tens of millions of square feet of leasable data center space.
Five of the largest and most well-known colocation vendors are CoreSite, Cyxtera Technologies, Digital Realty Trust, Equinix and NTT.
Colocation contracts can be complex. Learn more about where to look for hidden colocation costs and fees.