logic gate (AND, OR, XOR, NOT, NAND, NOR and XNOR)
What is a logic gate?
A logic gate is a device that acts as a building block for digital circuits. They perform basic logical functions that are fundamental to digital circuits. Most electronic devices we use today will have some form of logic gates in them. For example, logic gates can be used in digital electronics such as smartphones and tablets or in memory devices.
In a circuit, logic gates work based on a combination of digital signals coming from its inputs. Most logic gates have two inputs and one output, and they are based on Boolean algebra. At any given moment, every terminal is in one of the two binary conditions: true or false. False represents 0, and true represents 1.
Depending on the type of logic gate being used and the combination of inputs, the binary output will differ. A logic gate can be thought of like a light switch, where in one position the output is off (0), and in another, it is on (1). Logic gates are commonly used in integrated circuits (IC).
Basic logic gates
There are seven basic logic gates: AND, OR, XOR, NOT, NAND, NOR and XNOR.
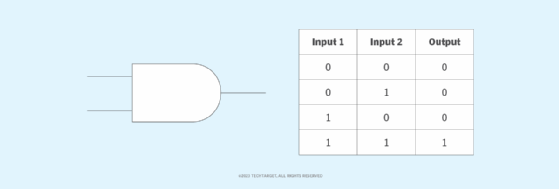
The AND gate is named so because, if 0 is false and 1 is true, the gate acts in the same way as the logical "and" operator. The following illustration and table show the circuit symbol and logic combinations for an AND gate. (In the symbol, the input terminals are on the left, and the output terminal is on the right.) The output is "true" when both inputs are "true." Otherwise, the output is "false." In other words, the output is 1 only when both inputs are 1.
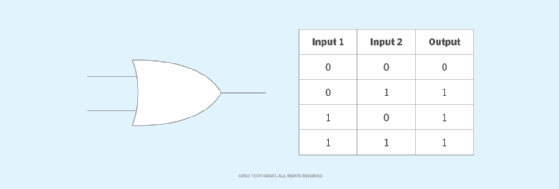
The OR gate gets its name from behaving like the logical inclusive "or." The output is true if one or both of the inputs are true. If both inputs are false, then the output is false. In other words, for the output to be 1, at least one input must be 1.
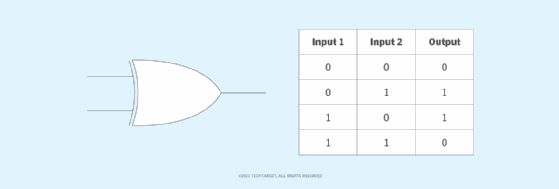
The XOR (exclusive-OR) gate acts in the same way as the logical "either/or." The output is true if either, but not both, of the inputs are true. The output is false if both inputs are "false" or if both inputs are true. Similarly, the output is 1 if the inputs are different but 0 if the inputs are the same.
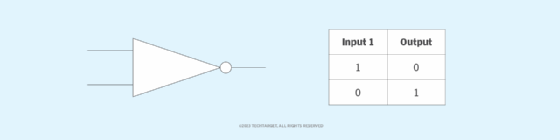
A logical inverter, sometimes called a NOT gate to differentiate it from other types of electronic inverter devices, has only one input. A NOT gate reverses the logic state. If the input is 1, then the output is 0. If the input is 0, then the output is 1.
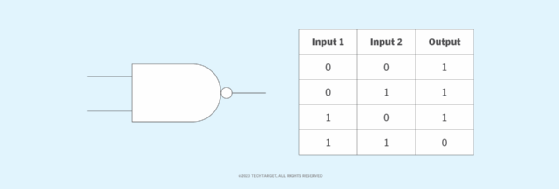
The NAND (Negated AND) gate operates as an AND gate followed by a NOT gate. It acts in the manner of the logical operation "and" followed by negation. The output is false if both inputs are true. Otherwise, the output is true. Another way to visualize it is that a NAND gate inverts the output of an AND gate. The NAND gate symbol is an AND gate with the circle of a NOT gate at the output.
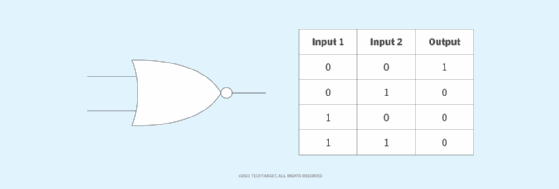
The NOR (NOT OR) gate is a combination OR gate followed by an inverter. Its output is true if both inputs are false. Otherwise, the output is false.
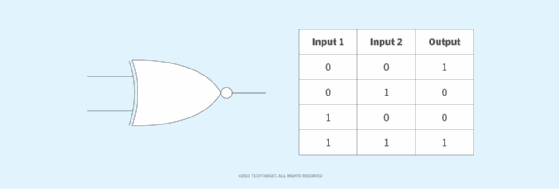
The XNOR (exclusive-NOR) gate is a combination of an XOR gate followed by an inverter. Its output is true if the inputs are the same and false if the inputs are different.
Complex operations can be performed using combinations of these logic gates. In theory, there is no limit to the number of gates that can be arrayed together in a single device. But in practice, there is a limit to the number of gates that can be packed into a given physical space.
Arrays of logic gates are found in digital ICs. As IC technology advances, the required physical volume for each individual logic gate decreases, and digital devices become capable of performing more complicated operations at increasing speeds.
Quantum computers also have their own version of logic gates, called quantum logic gates, or qutrit quantum gates, which is a quantum circuit that operates using a small number of qutrits, which are qubits that have one added dimension. Similar to how logic gates are the building blocks of digital circuits, qutrit quantum gates are the building blocks of quantum circuits.
Composition of logic gates
High or low binary conditions are represented by different voltage levels. The logic state of a terminal can, and generally does, change as the circuit processes data. In most logic gates, the low state is approximately zero volts (0 V), while the high state is approximately five volts positive (+5 V).
Logic gates can be made of resistors, transistors or diodes. These components are wired together in specific configurations to ensure they transform the inputs in expected ways. Resistors, for example, can commonly be used as a pull-up or pull-down resistor. Pull-up and pull-down resistors are used when there are any unused logic gate inputs to connect to a logic level 1 or 0. This prevents any false switching of the gate. Pull-up resistors are connected to Vcc (+5 V), and pull-down resistors are connected to ground (0 V).
Likewise, transistors provide switching -- turning on or off in response to input signals -- while diodes ensure current flows in only one direction to stabilize the circuit.
Commonly used logic gates are transistor-transistor logic (TTL) and complementary metal-oxide-silicon (CMOS). TTL ICs use negative-positive-negative and positive-negative-positive bipolar junction transistors. CMOS ICs are constructed from metal-oxide-semiconductor or junction-gate field effect transistors. TTL ICs might commonly be labeled as the 7400 series of chips, while CMOS ICs may often be marked as a 4000 series of chips.
Learn about fan-out in digital circuitry, which is a measure of the maximum number of digital inputs the output of a single logic gate can feed without disrupting circuitry operation.
