command prompt
What is a command prompt?
A command prompt is the input field in a text-based user interface screen for an operating system (OS) or program. The prompt is designed to elicit an action. The command prompt consists of a brief text string followed by a blinking cursor, which is where the user types command prompt commands.
Command-line interfaces (CLI) and prompts were the standard interface for computers from the early days of computing into the 1980s. Microsoft MS-DOS systems and other early consumer-based computers used CLIs. Current Windows systems offer the CLI for administrative tasks. The CLI is still an essential part of the Linux OS.
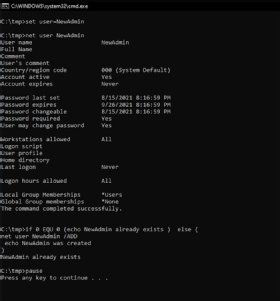
The command prompt is an executable CLI program, cmd.exe. At the command prompt, the user types a statement including a base batch file or a command name and any arguments to specify running conditions, logging and so on for the program. In Windows systems, such as Windows 10 and many previous versions of Windows, the command interpreter and executioner are referred to as the Windows Command Processor.
Command prompt interfaces can be powerful and succinct. Some tools that aren't available through the graphical user interface (GUI) can be accessed through the command prompt. It also offers superior automation through scripting, but mastering the commands can be challenging.
How to use the command prompt
Many Windows users regularly use the GUI. However, it is helpful to know how to execute system functions in the command prompt window. For example, basic functions such changing a directory or performing an examination of the system disk are easy to execute at the command level.
There are various ways to open command prompt. A common one in Windows is to use the command prompt shortcut located in the Start menu or on the Apps screen.
The basic command level might look like this:
C:\Windows\system32\>cmd.exe and <enter>
This results in the following:
C:\>
The OS is now ready for a command. Each command launches a batch file that initiates a specific function. The change directory function looks like this:
C:\>dir and <enter>
This presents a list of available directories linked to the root directory -- for example, the C drive -- in the system. To change to a different directory, the following is performed, using the example of changing to a directory called applications:
C:\>cd applications\ and <enter>
This changes the directory to:
C:\applications\>
Now the system needs a command to execute something in the applications directory. To check on the status of the elements associated with a specific directory, the user enters the following at the command prompt:
C:\applications\>chkdsk and <enter>
The OS executes the chkdsk utility for the applications directory and presents a summary of the components in that directory, such as the number of files and subdirectories, and number of bytes in use and the number available.
The syntax of the wording entered on the command-line is important. The system will not execute a function if a letter or number is in the wrong sequence.
Examples of commands
Commonly used commands include the following:
- Cls to clear the command prompt screen;
- Copy to create a copy of something such as a file;
- Del to delete a file;
- Format to formats a disk according to specific requirements;
- Ipconfig to list the network data such as IP address and subnet mask;
- Ping to send a packet to an IP address and display the information returned from the other device;
- Sfc to detect and fix corrupt system files; and
- Shutdown to execute a system shutdown or restart.
PowerShell is an advanced version of the Windows command prompt. It provides additional functionality to the command prompt.
The Windows command prompt and PowerShell can do similar things. Find out when to use command prompt and PowerShell with these examples.
