source code
What is source code?
Source code is the fundamental component of a computer program that is created by a programmer, often written in the form of functions, descriptions, definitions, calls, methods and other operational statements. It is designed to be human-readable and formatted in a way that developers and other users can understand.
As an example, when a programmer types a sequence of C programming language statements into Windows Notepad and saves the sequence as a text file, the text file now contains source code.
Source code and object code are sometimes referred to as the before and after versions of a compiled computer program. However, source code and object code do not apply to script (noncompiled or interpreted) program languages, like JavaScript, since there is only one form of the code.
Programmers can use a text editor, a visual programming tool or an integrated development environment (IDE) such as a software development kit (SDK) to create source code. In large program development environments, there are often management systems that help programmers separate and keep track of different states and levels of source code files.
Licensing of source code
Source code can be proprietary or open, and licensing agreements often reflect this distinction.
When a user installs a software suite like Microsoft Office, for example, the source code is proprietary. Microsoft only gives the customer access to the software's compiled executables and the associated library files that various executable files require to call program functions.
By comparison, when a user installs Apache OpenOffice, its Open Source software code can be downloaded and modified.
Typically, proprietary software vendors like Microsoft don't share source code with customers for two reasons: to protect intellectual property and to prevent the customer from making changes to source code in a way that might break the program or make it more vulnerable to attack. Proprietary software licenses often prohibit any attempt to discover or modify the source code.
Open source software, on the other hand, is purposely designed with the idea that source code should be made available since collaborative effort of developers working to enhance the software can help make it more robust and secure. Users can freely take open source code under public licenses, such as the GNU General Public License.
Purposes of source code
Beyond providing the foundation for software creation, source code has other important purposes. For example, skilled users who have access to source code can more easily customize software installations.
Meanwhile, other developers can use source code to create similar programs for other operating platforms -- a task that would be trickier without the coding instructions.
Access to source code also allows programmers to contribute to their community, either through sharing code for learning purposes or by recycling portions of it for other applications.
Organization of source code
Many different programs exist to create source code. Following is an example of the source code for a Hello World program in C language:
/* Hello World program */
#include<stdio.h>
main()
{
printf("Hello World");
}
A person with no background in programming can read the C programming source code above and understand that the goal of the program is to print the words "Hello World." However, in order to carry out the instructions, this source code must first be translated into a machine language that the computer's processor can understand; which is the job of a special interpreter program called a compiler. In this case, a C compiler is used.
After programmers compile source code, the file that contains the resulting output is referred to as object code.
Object code consists mainly of the numbers one and zero, or binary code, and cannot be easily read or understood by humans. Object code can then be linked to create an executable file that runs to perform the specific program functions.
Source code management systems can help programmers better collaborate on source code development -- like preventing one coder from inadvertently overwriting the work of another.
History of source code
Determining the historical start of source code is a subjective and elusive exercise. The first software was written in binary code in the 1940s. So, depending on one's viewpoint, such programs may be the initial samples of source code.
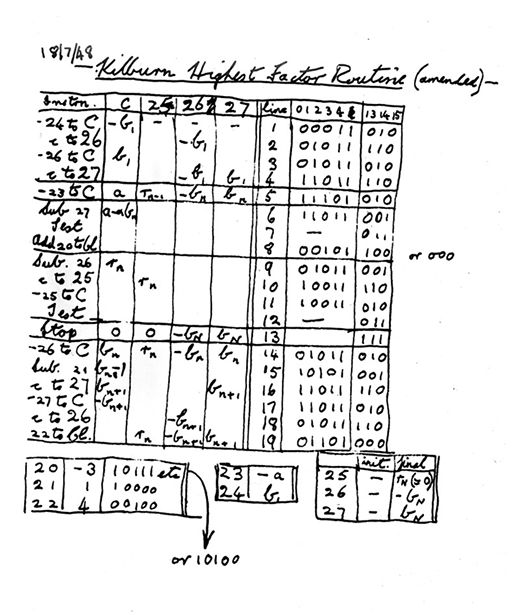
One of the earliest examples of source code as we recognize it today was written by Tom Kilburn, an early pioneer in computer science. Kilburn created the first successful digital program held electronically in a computer's memory in 1948. The software solved a mathematical equation.
In the 1950s and '60s, source code was often provided for free with software by the companies that created the programs. As growing computer companies expanded software's use, source code became more prolific and sought after. Computing magazines prior to the internet age would often print source code in their pages, with readers needing to retype the code character for character for their own use. Later, floppy disks decreased the price for electronically sharing source code, and then the internet further removed these obstacles.







