business sustainability
What is business sustainability?
Business sustainability, also known as corporate sustainability, is the management of environmental, social and financial concerns by a company to ensure responsible, ethical and ongoing success.
In traditional corporate culture, social and environmental concerns are often considered to be in conflict with financial goals. For example, depletion of nonrenewable natural resources isn't a sustainable practice. However, because greener alternatives typically require new investments in infrastructure, continued reliance on fossil fuels is the least expensive short-term option for energy usage.
In the long run, though, going green can increase a company's sustainability by reducing its energy costs, carbon footprint and climate-related business risks. Similarly, investments in socially responsible and ethical practices might initially cost more money, but lead to enhanced recruitment, branding and public relations -- and, ultimately, increased profitability.
Why is business sustainability important?
Business sustainability helps resolve or mitigate environmental, social and economic challenges through the strategic management of corporate resources. It seeks to improve the effects a company has on the external world. In return, the business generates goodwill with customers, employees, community members, investors and other stakeholders.
In addition, a business sustainability program can lower costs and promote the long-term financial health of the organization. If a company spends less on electricity, water and other resources, it can increase profits. Similarly, a company's sustainability initiatives might help improve business results by elevating its standing in the community and with employees.

Companies are advised to regularly publish sustainability goals and report on their progress toward reaching them. This transparency helps employees and outsiders understand how the business is contributing to a sustainable global economy. In addition, these progress reports help maintain trust with stakeholders.
Furthermore, business sustainability objectives and goals help organizations stay true to commitments to core business interests such as operational efficiency and shareholder value. Business sustainability has been incorporated into other business movements such as kaizen, a philosophy of continuous improvement that aims to reduce waste in manufacturing and business processes through a focus on increased quality control and productivity. Sustainability efforts also help to build more resilient supply chains by increasing efficiency and better managing costs.
What are the 3 types of sustainability?
Environmental, social and economic demands are considered the three pillars of business sustainability. In the corporate world, they're sometimes referred to as the triple bottom line, a sustainability-focused framework for assessing a company's social and environmental impact and the overall economic value it creates. This is a departure from the traditional concept of the bottom line, which evaluates all efforts in terms of their short-term effect on profits.
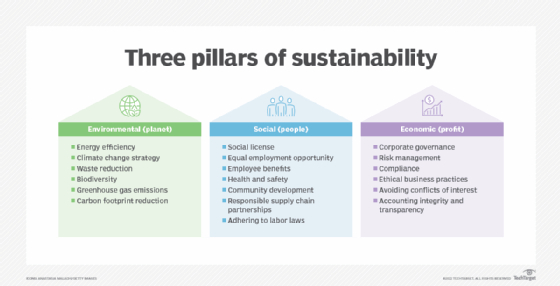
The three main pillars of sustainability are the following:
- Environmental sustainability garners the most attention from businesses. It requires companies to focus on improving energy efficiency in data centers and other facilities and on reducing their carbon footprint, packaging waste and water usage, among other environmental issues.
- Social sustainability focuses on corporate social responsibility and being a business that customers, the surrounding community, employees and investors want to support. Companies practicing social sustainability are advised to adopt fair labor practices and invest in long-term community relationships by giving back to the local community, among other steps.
- Economic sustainability focuses on long-term business profitability and includes activities such as corporate governance, risk management, regulatory compliance, ethical business practices and accounting transparency.
These three categories are commonly referred to by the acronym ESG -- or environmental, social and governance. ESG is another framework that helps companies document their business practices, progress, and related risks and opportunities as part of business sustainability efforts. Businesses can then measure their success in these areas using various ESG metrics and report the results publicly. ESG rating agencies use the disclosures and other data to give companies ESG scores, which investors and other stakeholders can consider in evaluating organizations.
How to create a sustainable business strategy
While there's no one right way to practice sustainable business development, organizations can implement the following best practices:
- Address compliance. Companies need to pay attention to and meet compliance requirements regarding waste management, pollution and energy efficiency, as well as regulations related to corporate governance such as the Sarbanes-Oxley Act in the U.S. and the European Union's General Data Protection Regulation. Failing to adhere to these regulations can result in financial fines and reputational damage, which can make it difficult to sustain a business.
- Align overall business strategy with sustainability. Businesses should realize that contrary to traditional ways of thinking, sustainability isn't at odds with higher profits or a competitive edge over business rivals. Sustainability -- social, environmental and corporate -- is essential for long-term success. Businesses should strive to exceed compliance and use sustainability to their competitive advantage.
- Quantify results and return on investment. Businesses should quantify the return on sustainability investments to make progress easier to track. For example, on compliance-based sustainability initiatives, regulations typically outline a preset framework to help businesses measure their progress. Various ESG reporting frameworks and standards are also available to use. It's generally more difficult for businesses to independently define a framework that measures sustainability, with the goal of achieving competitive advantage once base-level compliance requirements are met.
- Be proactive. Anticipate potential areas of improvement and build them into the sustainability strategy before they become a visible problem. While most corporations understand the importance of sustainability, not all are proactive.
- Be transparent. Disclosures about a company's sustainability strategy must be shared with the board of directors, shareholders, customers, employees and the surrounding community. Businesses should also be forthcoming about where improvements are required and their plans to address that.
- Collaborate. Work with other organizations -- suppliers and business partners, for example -- to jointly develop plans to address larger economic, environmental and social problems.
For more on ESG strategy and management, read the following articles:
8 green computing best practices
ESG audit checklist: 6 steps for success
ESG materiality assessments: What CIOs, others need to know
Examples of business sustainability
Long-term business sustainability goals require an extended timeline for return on investment -- but once initial investments are made, they can lead to increased profitability. For example, so-called free cooling for data centers takes advantage of natural cooling methods to control temperatures in IT facilities. While investing in such approaches can require an initial cash outlay, free cooling relies on renewable resources that are freely available and reliable, which can eventually pay off for the business.
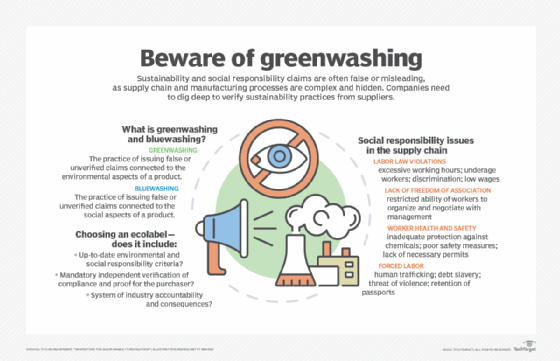
Another business sustainability practice is carbon offsetting. Businesses use carbon offsets to register their emissions and offset them by reducing emissions elsewhere in the world. For example, an airline might generate a certain amount of greenhouse gas emissions, which are recorded and then offset in other parts of the world via forestry, landfill gas capture, or solar and wind projects. Businesses can receive credits for offsetting carbon emissions to validate their efforts. However, such initiatives can be considered Greenwashing if the company overstates its environmental contributions.
Another way to achieve environmental sustainability in the enterprise is to embrace net-zero emissions both internally and across supply chains by using electronic vehicles or transitioning to environmentally friendly, low-impact refrigerants. Many companies, including H&M Group, Ikea, Nestle, Unilever and Walmart, have pledged to achieve net-zero carbon emissions in the coming decades.
Learn more about the potential business benefits of sustainability and ESG initiatives for companies.