
crisis management
What is crisis management?
Crisis management is the application of strategies designed to help an organization deal with a sudden and significant negative event, while maintaining business continuity. Crisis management involves implementing policies and procedures to defend, mitigate and prevent a crisis.
A crisis can occur as a result of an unpredictable event or an unforeseeable consequence of some event that had been considered as a potential risk. In either case, crises almost invariably require that decisions be made quickly to limit damage to the organization. Crises can include natural disasters, financial problems and cybersecurity attacks.
The nature of the potential damage varies based on the nature of the crisis. In most cases, though, a crisis can affect health, safety, the organization's finances, the organization's reputation, customer and brand loyalty, or some combination of these. A devastating fire could be a crisis that puts the organization's finances in jeopardy. However, if the fire occurs during business hours, then the fire might also jeopardize health and safety since employees may find themselves in harm's way.
Importance of crisis management
Crisis management involves strategic planning and responses to unexpected events and threats and is one of best methods of preventing, mitigating and responding to a crisis. Crisis management's most important features include the following.
This article is part of
Complete crisis management guide and free template
Protecting reputation and stakeholders
Crises can tarnish the image and credibility of a business, leading to a loss of trust from customers, investors and other stakeholders, such as employees. By implementing effective crisis management strategies, organizations can instill confidence in their customers and mitigate the negative reputational consequences of a crisis.
Minimizing financial losses
Some crises can lead to significant financial losses for businesses. From operational disruptions to legal liabilities, the financial impact of a crisis can do significant damage to organizations. Well-designed crisis management plans (CMPs) can minimize damaging financial losses, such as those caused by data breaches, which have cost, on average, $4.45 million each globally in 2023.
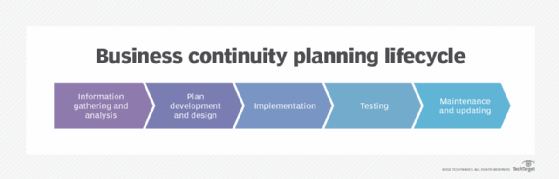
Ensuring business continuity
Another key aspect of crisis management is ensuring that essential operations and business can continue despite a disruptive crisis with business continuity plans. These plans implement contingency plans, emergency response protocols, backup protocols and other procedures to safeguard critical business functions. Business continuity plans can help deliver key services to employees and customers during a crisis.
Maintaining public trust
Crisis management also helps organizations handle crises and communicate their handling in a transparent and trustworthy way. Organizations can maintain public trust by transparently conveying their messages through empathetic public relations, addressing stakeholder concerns, and providing timely or real-time updates.
Types of crises
Different kinds of crises are more relevant than others to specific industries. It is important for organizations to understand all the different types of crises they may face in order to develop appropriate crisis management strategies. The most common crises include the following.
Natural disasters
Natural disasters, such as earthquakes, hurricanes, floods and wildfires, can cause widespread damage and disruption to businesses. These crises often require immediate response and disaster recovery efforts to ensure the safety of employees, protect assets and restore operations.
Cybersecurity breaches
Cyber attacks pose a significant threat to organizations of all sizes. Data breaches, ransomware attacks and other cyber threats can result in the loss of sensitive information, financial damages and harm to reputations. Effective crisis management in the realm of cybersecurity involves implementing comprehensive security measures, incident response processes, and communication strategies to address and mitigate the impact of such breaches.
Public health crises
Public health crises, such as pandemics and disease outbreaks, can have far-reaching consequences for businesses. These crises often require organizations to implement measures such as pandemic plans, remote work policies, employee safety protocols and communication plans to ensure the health and well-being of their workforce, while maintaining essential operations.
Reputation crises
Reputation crises occur for various reasons, such as product recalls, ethical scandals or negative media coverage. These crises can severely damage an organization's brand image and customer trust. Crisis management in the realm of reputation involves providing swift and transparent communication, addressing the root causes of the crisis, implementing measures to rebuild trust and credibility, and establishing risk management.
Financial crises
Financial crises can arise from economic downturns, market fluctuations or internal financial mismanagement. These crises can threaten the stability and solvency of an organization. Crisis management in the financial realm involves implementing financial contingency plans, seeking external support if necessary and communicating with stakeholders to maintain their confidence in the organization's financial health.
Organizational misdeed crises
Crises started by organizational misdeeds include actions that prioritize the interests of stockholders with negative consequences for stakeholders. This type of crisis usually involves decisions that serve short-term financial gains over long-term stakeholder interests, such as hiding or misrepresenting critical information or acting in deliberately illegal ways.
Crisis management goals
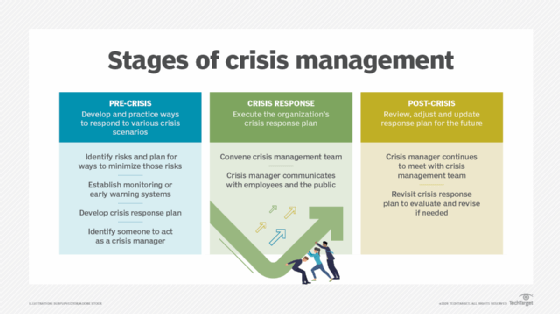
Crisis management seeks to minimize the damage a crisis causes. However, this does not mean crisis management is the same thing as crisis response. Instead, crisis management is a comprehensive process that is put into practice before a crisis even happens. Crisis management practices are engaged before, during and after a crisis and include proactive measures, such as risk assessment.
To navigate a crisis successfully, organizations should set clear goals that guide their crisis management efforts. These goals provide a framework for decision-making and help ensure a coordinated and effective response. Key goals include the following.
Ensuring safety and well-being
The primary goal of crisis management is to ensure the safety and well-being of employees, customers and other stakeholders. This involves implementing emergency response plans, providing timely and accurate information, and taking necessary actions to mitigate hazards and risks and protect individuals from harm.
Minimizing disruption to operations
During a crisis, it's important for organizations to minimize the disruption to their operations and maintain business continuity as much as possible. This may involve implementing alternative work arrangements, activating backup systems and reallocating resources to critical functions. The goal is to keep mission-critical applications running smoothly, while addressing the challenges posed by the crisis.
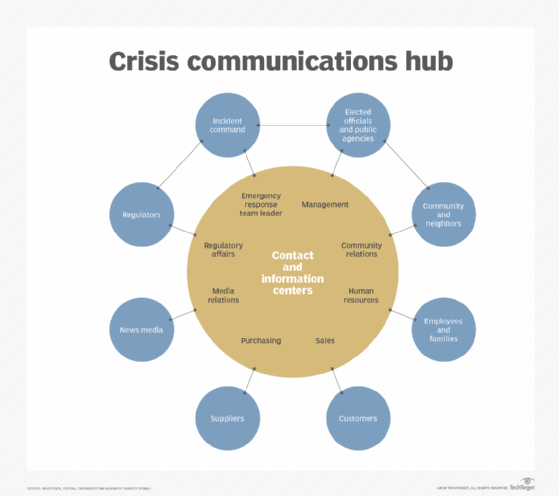
Providing crisis communication
Effective communication is a key goal of crisis management. Organizations need to establish clear and transparent channels of communication to keep stakeholders informed, address concerns and provide updates on the progress of the crisis response. This includes utilizing various communication platforms, such as traditional media, social media and internal communication channels, to reach different audiences effectively.
Protecting reputation and brand image
Maintaining a positive reputation and brand image is crucial during a crisis. Organizations should try to protect their reputation by addressing the crisis with honesty, transparency and empathy. This includes promptly addressing key issues, taking responsibility for mistakes, and implementing measures to rebuild trust and credibility.
Learning and adapting
Crisis situations provide valuable opportunities for organizations to learn and improve their crisis management strategies. After the crisis has been resolved, it's important to conduct a thorough review and analysis of the response efforts. This includes identifying strengths and weaknesses, documenting lessons learned, and implementing changes to enhance future crisis management capabilities and prevent potential crises. Organizations can also learn from the mistakes of other companies, such as the 2020 SolarWinds attack.
Recovery crisis management vs. risk management
Risk management is a part of crisis management. Before a crisis begins, pre-crisis planning identifies risks and then finds ways to mitigate or lessen those risks. It is important to note, however, that crisis management and risk management are two different things.
Risk management involves looking for ways to minimize risks to prevent them from ever happening and does not cover what to do when crises do occur. While crisis management involves risk management, it is equally concerned with figuring out the best way to respond when an incident does occur. As such, risk management is an important part of crisis management, but crisis management also covers incident response, whereas risk management and even enterprise risk management does not.
Stages of a crisis
To successfully execute a CMP and respond to a crisis, it's critical to understand the different stages of a crisis. This includes stages happening before, during and after a crisis. The following are the six stages of a crisis:
- Early warning. Organizations should look for warnings of a crisis and weigh the probabilities of one occurring. Crises cannot always be predicted, but there can be some signs, such as weather patterns, national and global economics, and negligence toward cybersecurity risks.
- Risk assessment. The risks, damages and acute problems of a crisis are now discussed by the risk management team and worst-case scenarios involving stakeholders are prepared for.
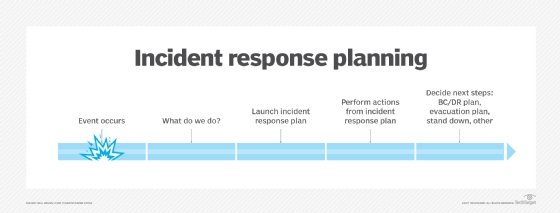
- Company response. Companies must now choose a CMP and notify all involved parties, such as employees and customers, about the crisis and the resolution plan.
- Crisis handling. The CMP is implemented, and everyone involved in the plan engages in open communication and begins working on resolving the crisis.
- Resolution. The crisis is now under control, with all relevant employees handling their resolution duties. Plans for recovering to normalcy should now be implemented.
- Recovery. In this final stage, the crisis is over, and the organization is returning to its normal daily operations. The organization should fully analyze the crisis, and lessons learned should be noted for the future.
Best practices for managing a crisis
It is essential organizations take a structured and proactive approach when a crisis occurs. There are several best practices for managing crises effectively, including the following.
Establishing a crisis management team
Successful crisis management requires establishing a dedicated crisis management team. This team should be composed of highly skilled and experienced individuals from various departments within the organization. They should have clear authority and defined roles to manage the crisis effectively. This can ensure a swift and coordinated response to prevent or mitigate the impact of a crisis.
The key to effective pre-crisis planning is to involve as many stakeholders as possible. That way, all areas of the organization are represented in the risk identification and risk planning process. Corporate crisis response teams often include representatives from the organization's legal, human resources, finance and operations staff. It is also customary to identify someone to act as a crisis manager.
Creating warning and risk assessment
As important as it is to identify risks and plan for ways to minimize those risks and their effects, it is equally important to establish monitoring systems, such as strong IT monitoring, that can provide early warning signals of any foreseeable crisis. These early warning systems can take a variety of forms and differ widely based on the identified risks.
Some early warning systems might be mechanical or electronic. For instance, thermography is sometimes used to detect a buildup of heat before a fire starts. Other early warning systems may consist of financial metrics. For example, an organization might be able to anticipate a substantial drop in revenue by monitoring its customers' stock prices.
Building crisis response and management
Clear incident management processes and workflows should be established in advance of crises. These include defining clear roles, responsibilities, escalation procedures and channels of communication. For instance, when a crisis occurs, the crisis manager is responsible for directing the organization's response in accordance with its established CMP. The crisis manager is usually also the person who is tasked with communicating to the public and stakeholders.
If a crisis affects public health or safety, then the crisis manager should make a public statement as quickly as possible. In a public crisis, the media inevitably seeks out employees for comment. It is important for the organization's employees to know ahead of time who is and is not authorized to speak to the media. Employees who are allowed to speak to the media must do so in a manner consistent with what the crisis manager is saying.
Using incident management software
Streamline crisis response efforts with incident management software, which provides a centralized platform to track and manage major incidents, assign tasks, communicate updates and analyze data for future crisis management improvements. This software can help organizations enhance their crisis response capabilities, improve team member collaboration, and ensure better documentation of incidents and their resolution.
Conduct post-crisis analysis and resolution
After a crisis subsides and business begins to return to normal, the crisis manager should continue to meet with members of the crisis management team, especially those from the legal and finance departments, to evaluate the progression of the recovery efforts. At the same time, the crisis manager needs to provide the latest information to key stakeholders to keep them aware of the current situation.
Following a crisis, it is also important for the crisis management team to revisit the organization's CMP with the goal of evaluating how well the plan worked and what aspects of the plan need to be revised based on what was learned during the crisis.
Learning from past incidents
Every crisis presents an opportunity for learning and improvement. After the resolution of a crisis, thorough post-incidents reviews should be conducted to analyze the effectiveness of the crisis response efforts. Gaps and weaknesses in the processes should be identified, and strategies should be developed to address them. Document lessons learned, and update CMPs accordingly. This can help organizations learn from past incidents and improve their organizational and operational resilience and readiness for future incidents.

Challenges of crisis management
Though crisis management is crucial for every organization, it comes with some challenges. The most challenging aspects of crisis management include the following:
- Handling time pressure and decision-making during a rapidly evolving crisis, including the gathering of facts and informed decisions.
- Implementing effective internal and external communication and successful stakeholder management, including regular updates to relevant parties.
- Maintaining business continuity, such as uninterrupted service and service management, during crises such as natural disasters.
- Providing emotional support to teams dealing with the stress, anxiety and fear of a crisis.
History of crisis management
The field of crisis management is generally considered to have originated with Johnson & Johnson's handling of a crisis in 1982 when cyanide-laced Tylenol killed seven people in the Chicago area. The company immediately recalled all Tylenol capsules in the country and offered free products in tamper-proof packaging. As a result of the company's swift and effective response, the effect to shareholders was minimized, and the brand recovered and flourished.
Today, virtually all major corporations, nonprofit agencies and public sector organizations use crisis management. Developing, practicing and updating a CMP is a critical piece of ensuring a business can respond to unforeseen disasters. The nature of the crisis management activities can vary, however, based on the organization type. For instance, a manufacturing company likely needs a CMP for responding to a large-scale industrial accident, such as an explosion or chemical spill, whereas an insurance company would be far less likely to face such risks.
Crisis management is critical to the prevention and mitigation of crises. Use this comprehensive guide and free template to plan for a crisis.